A significant security breach within the Quick Page/Post Redirect Plugin, a widely used WordPress plugin, has been identified. This plugin, which boasts over 70,000 active installations, has been compromised by a backdoor that has remained hidden for several years.
Discovery of the Security Breach
Security expert Austin Ginder uncovered the malicious activity, which had been dormant for five years. This backdoor was capable of injecting unauthorized code into websites without detection. By utilizing a custom update mechanism, the plugin was transformed into a tool for unauthorized SEO manipulation and remote execution of code.
Details of the Plugin Compromise
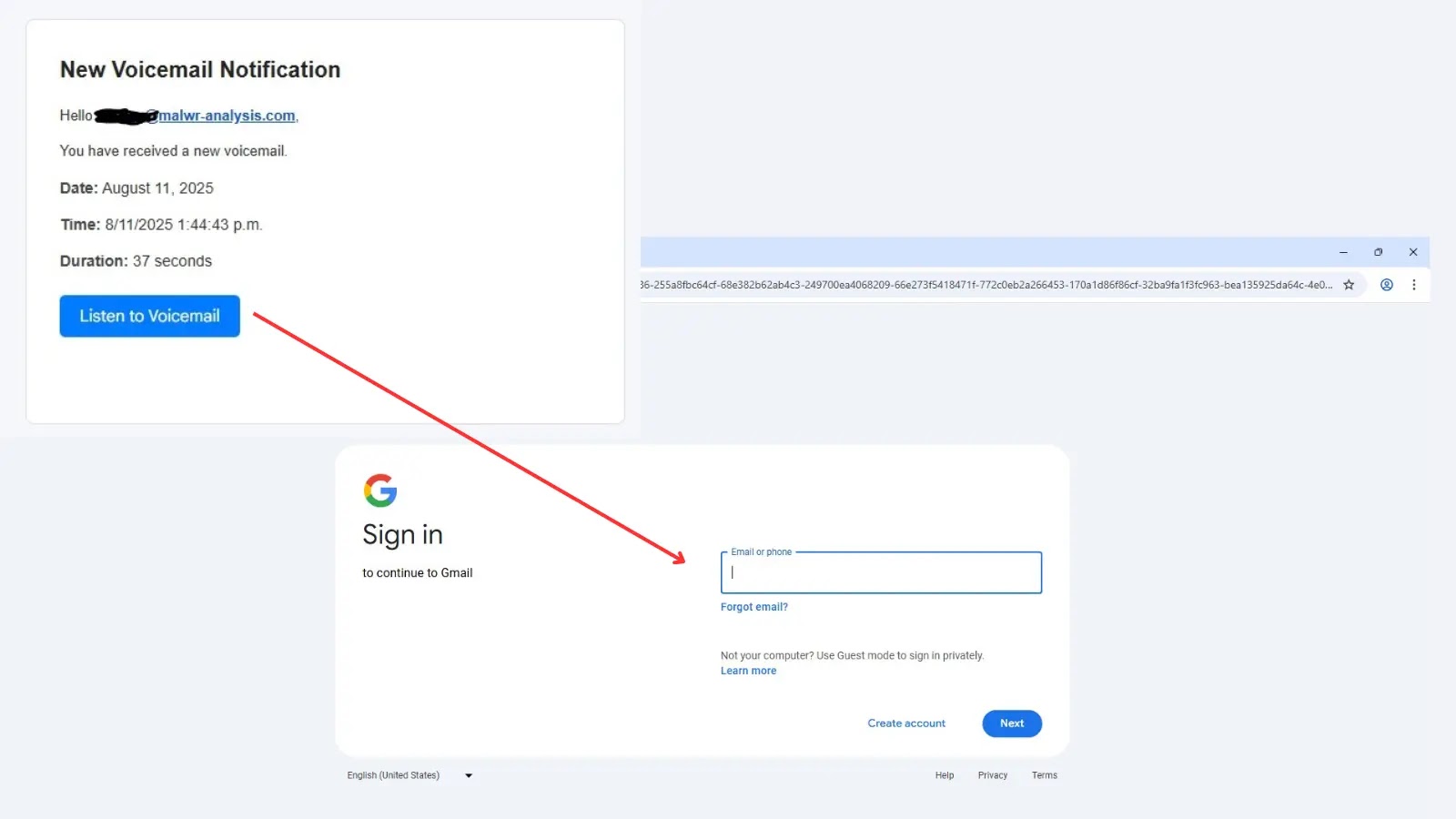
The issue came to light during routine security checks when anomalies were detected in plugin version 5.2.3. Although sites reported using this version, discrepancies in file hashes revealed tampered files. These files contained an unauthorized function that communicated with an external server, injecting content into web pages without administrator knowledge.
The hidden code specifically avoided detection by administrators, activating only for ordinary users and search engine bots. The complex attack involved two backdoors: an active one using a manipulated plugin update checker and a passive one that fetched hidden content from a remote server.
Origins of the Attack and Response
The attack was linked to the plugin’s original developer, anadnet, who introduced the malicious updater to the official repository in 2020. This allowed the compromised code to spread widely before being quietly removed from the source code. However, the installations remained connected to the attacker’s infrastructure.
The WordPress plugin review team has temporarily removed the Quick Page/Post Redirect Plugin from the directory for further investigation. Conventional vulnerability scanners often miss such sophisticated supply chain attacks due to version number spoofing.
To safeguard against these threats, administrators are advised to verify plugin integrity using WordPress’s command-line tools. Any discrepancies should prompt immediate uninstallation and replacement with secure alternatives.
Stay updated on cybersecurity developments by following us on Google News, LinkedIn, and X. Reach out to us for story features.