A newly discovered Python-based malware, DEEP#DOOR, poses a significant threat to Windows users by integrating a comprehensive backdoor with an efficient credential-stealing mechanism.
This malware operates stealthily, deeply embedding itself into compromised systems to gather sensitive information from various sources simultaneously.
How DEEP#DOOR Infiltrates Systems
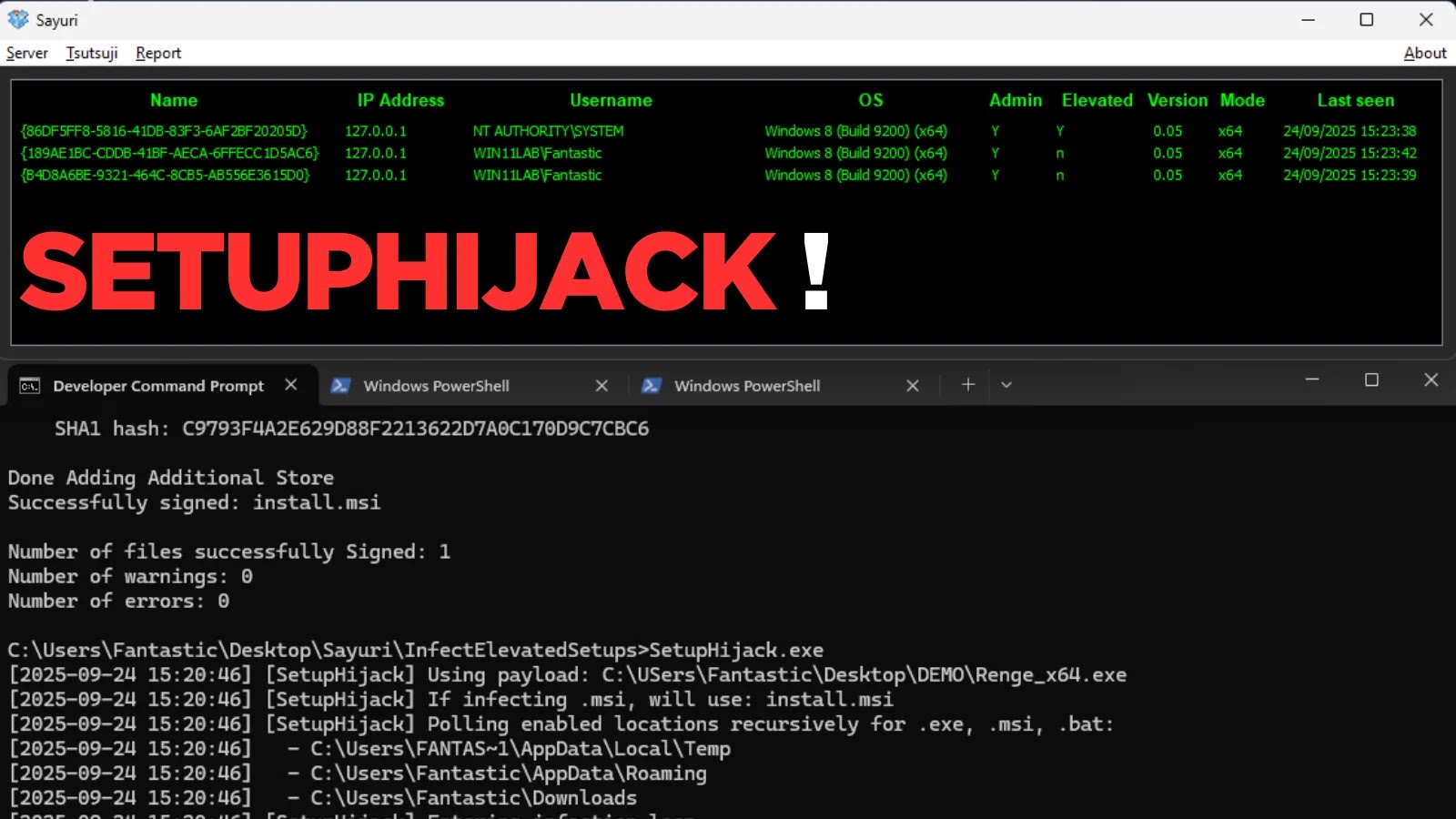
DEEP#DOOR infiltrates target systems through an obfuscated batch script commonly named “finallyJob.bat,” which serves as the initial trigger for execution.
Unlike other malware that depend on additional payloads, DEEP#DOOR carries the entire Python backdoor within the batch file, minimizing detection by network security tools.
The infection starts when a user unknowingly executes what seems to be a harmless batch file on a Windows device.
Malware Operations and Evasion Tactics
Securonix Threat Research analysts have dissected DEEP#DOOR, identifying it as a batch loader aimed at deploying a persistent backdoor and credential-stealing implant on Windows systems.
The attack sequence begins with the execution of a batch script that dynamically extracts and executes an embedded Python Remote Access Tool payload, establishing persistence through various system modifications.
Once activated, the malware communicates with attacker-managed infrastructure via a TCP tunneling service, granting remote operators extensive control, including command execution and surveillance capabilities.
Credential Theft and Security Implications
DEEP#DOOR’s credential-stealing capability is particularly damaging. It targets browser-stored passwords, cloud authentication tokens, sensitive credentials, and SSH keys, facilitating unauthorized access across impacted networks.
The malware uses specific functions to extract data from browser databases and configuration files, and it retrieves credentials from the Windows Credential Manager.
This broad-spectrum data collection can expose an organization’s entire access framework, allowing attackers easy reinfiltration even after initial malware removal.
Preventive Measures Against DEEP#DOOR
Organizations should avoid executing unknown batch files, particularly those received via email or shared links. Monitoring unusual command-line activity and auditing system configurations are essential preventive measures.
Regularly rotating cloud tokens and SSH keys, enabling Windows Defender tamper protection, and deploying network monitoring tools are recommended to mitigate the risk of DEEP#DOOR.
Additionally, behavioral analytics and anomaly detection should be prioritized over traditional antivirus solutions, given the malware’s reliance on obfuscated scripting.
Stay updated with more cybersecurity news by following us on Google News, LinkedIn, and X.