A cyber threat group identified as UAT-8302, associated with China, has been reported to target government institutions across South America and Southeastern Europe. The group utilizes a combination of custom malware and readily available open-source tools to exfiltrate sensitive information.
Organized Cyber Intrusions
Since late 2024, UAT-8302 has intensified its efforts in attacking governmental entities in Southeastern Europe throughout 2025. The group’s strategy involves penetrating networks, maintaining a low profile, and extracting valuable data.
The hackers’ proficiency lies in their ability to mask their activities. By leveraging legitimate cloud services in conjunction with custom-developed malware, they complicate the differentiation between authentic network traffic and malicious actions.
Advanced Persistent Threat Tactics
Displaying significant patience, UAT-8302 conducts thorough reconnaissance of network endpoints before advancing further. This meticulous approach is typical of state-sponsored attacks targeting critical governmental infrastructures.
According to Cisco Talos researchers, UAT-8302 is a China-linked advanced persistent threat (APT) group. Their primary mission involves gaining and sustaining prolonged access to government and related sectors globally.
The analysis by Talos highlights a shared toolkit with other China-nexus groups, suggesting a close operational collaboration among these threat actors.
Malware and Techniques
Upon breaching a network, UAT-8302 executes a systematic procedure involving credential collection, Active Directory data gathering, and network mapping. They utilize tools like Impacket and custom PowerShell scripts to understand the environment thoroughly.
Among their malware arsenal, the group deploys NetDraft, a .NET-based backdoor linked to the FinDraft family, and the CloudSorcerer backdoor. This arsenal enables comprehensive control and data extraction from compromised systems.
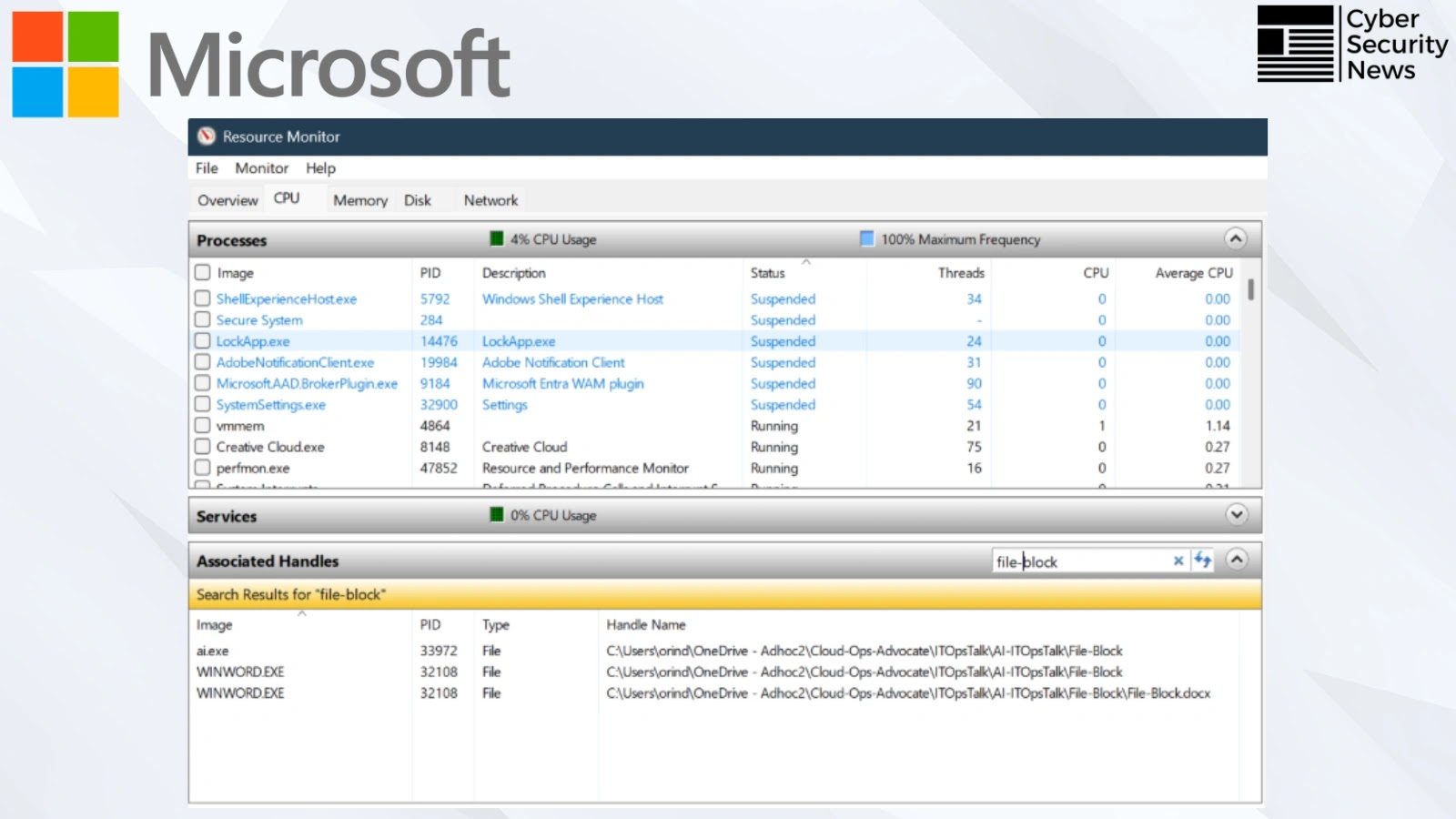
NetDraft is particularly noteworthy for its use of a DLL side-loading method, disguising its communication with a OneDrive-based command-and-control server through Microsoft Graph API, which allows it to evade detection.
Preventive Measures Against UAT-8302
To counter UAT-8302’s tactics, government agencies are advised to enhance endpoint detection systems, scrutinize outbound cloud traffic, and conduct regular audits of scheduled tasks and DLL loading behaviors.
Monitoring unusual patterns on platforms like OneDrive and GitHub, and keeping network security tools updated, can help mitigate the risks posed by this sophisticated threat group.
As cyber threats evolve, maintaining robust cybersecurity measures and staying informed on the latest threat intelligence is critical for protecting sensitive government data.