A newly identified Brazilian banking trojan, known as TCLBANKER, has been uncovered by security analysts. Targeting a total of 59 banking, fintech, and cryptocurrency platforms, this malware poses a significant threat to financial security. The malicious activity is currently being monitored by Elastic Security Labs under the code name REF3076, marking a notable advancement from the previously known Maverick malware.
The Mechanics of TCLBANKER
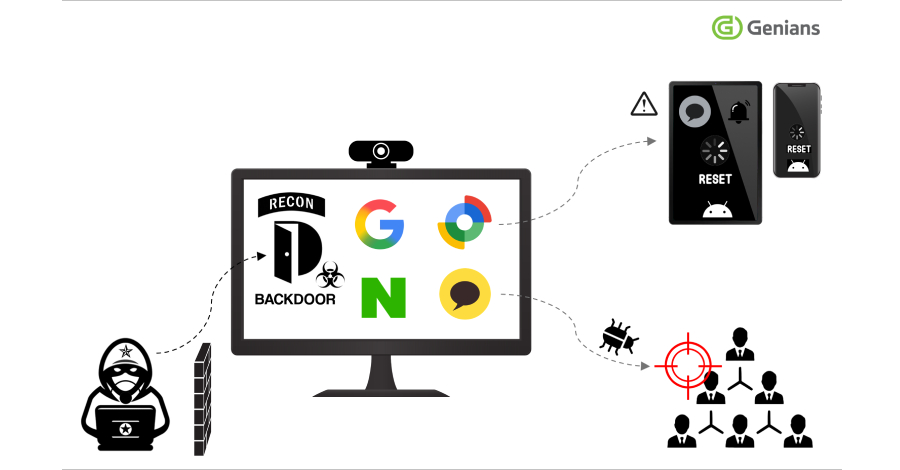
TCLBANKER uses a sophisticated loader to initiate its attack sequence, integrating a dual-module system designed for persistence and expansion. The primary components include a comprehensive banking trojan and a worm that exploits WhatsApp and Microsoft Outlook for propagation. Analysts highlight the use of a malicious MSI installer within a ZIP file to introduce the threat, leveraging a signed Logitech program to disguise its operations.
The malware employs DLL side-loading to execute a harmful DLL, ensuring it only functions when invoked by specific executables. This technique allows TCLBANKER to circumvent detection tools, replacing security hooks and disabling telemetry to maintain stealth. The trojan also incorporates measures to verify its Brazilian environment before fully activating, relying on system checks to decrypt its payload effectively.
Propagation and Attack Strategy
TCLBANKER’s propagation strategy is particularly concerning, utilizing WhatsApp Web and Outlook email accounts to disseminate itself. The trojan hijacks authenticated browser sessions to send spam and phishing messages, effectively bypassing traditional security filters. By exploiting trusted communication channels, the malware gains an advantage in spreading undetected.
The WhatsApp component automates message distribution using the open-source project WPPConnect, filtering out non-relevant contacts. Meanwhile, the Outlook component acts as a spambot, sending phishing emails from compromised accounts, thus enhancing the perceived trustworthiness of the messages.
Implications for Financial Security
This development reflects a broader trend in the evolution of Brazilian banking trojans, with TCLBANKER embodying advanced techniques once exclusive to more sophisticated cyber threats. The malware’s ability to conduct real-time social engineering via WebSocket, alongside environment-gated payload decryption, marks a significant shift toward more accessible and potent crimeware.
The campaign’s utilization of legitimate communication platforms like WhatsApp and Outlook highlights the challenges traditional security measures face. As these threats continue to evolve, there is an urgent need for innovative defense strategies capable of identifying and mitigating such sophisticated attacks.
As TCLBANKER continues to pose a threat to financial institutions, staying informed and vigilant is crucial. Security professionals and organizations must adapt to these evolving tactics to protect against potential breaches effectively.