OX Security’s recent analysis of 216 million security findings across 250 organizations over a 90-day period reveals a concerning trend: critical security risks have seen a dramatic rise, increasing by nearly 400% compared to the previous year. This surge is largely attributed to the rapid development in AI-assisted technologies, which has outpaced traditional remediation efforts.
The Growing Velocity Gap in AI Development
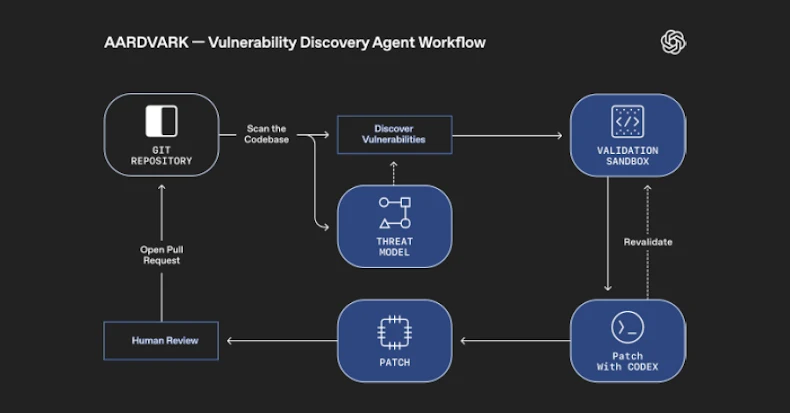
The acceleration in AI-driven development has led to the emergence of a ‘velocity gap,’ where high-impact vulnerabilities are multiplying faster than they can be addressed. The proportion of critical findings relative to overall alerts has almost tripled, escalating from 0.035% to 0.092%. This trend highlights the pressing need for enhanced remediation workflows to keep pace with these developments.
According to the report, the growth in alert volume was 52% year-over-year, yet the prioritized critical risks soared at a much higher rate. The findings suggest that the traditional metrics such as CVSS are becoming less effective in assessing real-world risks, with business context playing a more significant role.
Key Influences on Risk Assessment
The report identifies that technical severity scores are no longer the sole indicators of risk levels. Factors such as High Business Priority (27.76%) and PII Processing (22.08%) are increasingly critical in determining the potential impact of vulnerabilities. The location of a vulnerability in a system is now often more significant than the vulnerability itself, emphasizing the contextual nature of modern security challenges.
The integration of AI coding tools has directly correlated with the increase in critical findings, averaging 795 per organization, up from 202. This rise indicates the complexity and context-dependence of new vulnerabilities that traditional scanning tools fail to detect.
Sector-Specific Variations in Risk Profiles
The analysis also highlights significant sector-specific variations in security risks. For instance, insurance companies reported the highest density of critical findings at 1.76%, whereas the automotive industry generated the most alerts, likely due to extensive software development in software-defined vehicles. These differences underscore the need for tailored security strategies across different industries.
This comprehensive analysis by OX Security marks the second year of benchmarking the current state of application security, providing valuable insights into the evolving landscape of cybersecurity risks. The full report, including detailed methodology and industry benchmarks, is available for those interested in exploring further.
For more in-depth coverage and exclusive content, follow us on Google News, Twitter, and LinkedIn.