Email security systems are crucial but insufficient in completely mitigating phishing threats. Modern phishing attempts are sophisticated, often bypassing filters using novel domains, CAPTCHA verifications, fake login pages, and even legitimate remote management tools.
Challenges in Modern Phishing Campaigns
For security professionals, the primary challenge is minimizing business exposure. A single missed phishing email can delay response times, create uncertainty, and leave security teams uncertain about the extent of compromise. Advanced Security Operations Centers (SOCs) aim to close this gap, ensuring phishing threats are detected early to prevent operational disruptions.
Current phishing attacks often evade detection by exploiting the gap between email delivery and user interaction. While email security tools inspect messages, senders, links, and known indicators at delivery, many phishing schemes activate their malicious elements later, during browser interactions.
Why Phishing Threats Go Undetected
The initial stages of a phishing attack might appear benign, with links that lack a history sufficient for flagging at the time of delivery. The true threat may only emerge after user interaction, often through redirects that obscure the final malicious destination. Without an attached file, early detection becomes even more challenging.
Phishing campaigns frequently target identity access rather than solely focusing on malware delivery. This necessitates not just identifying the email but also rapidly assessing post-delivery activities to mitigate exposure, safeguard accounts, and make informed response decisions.
Leveraging Behavior-Based Analysis
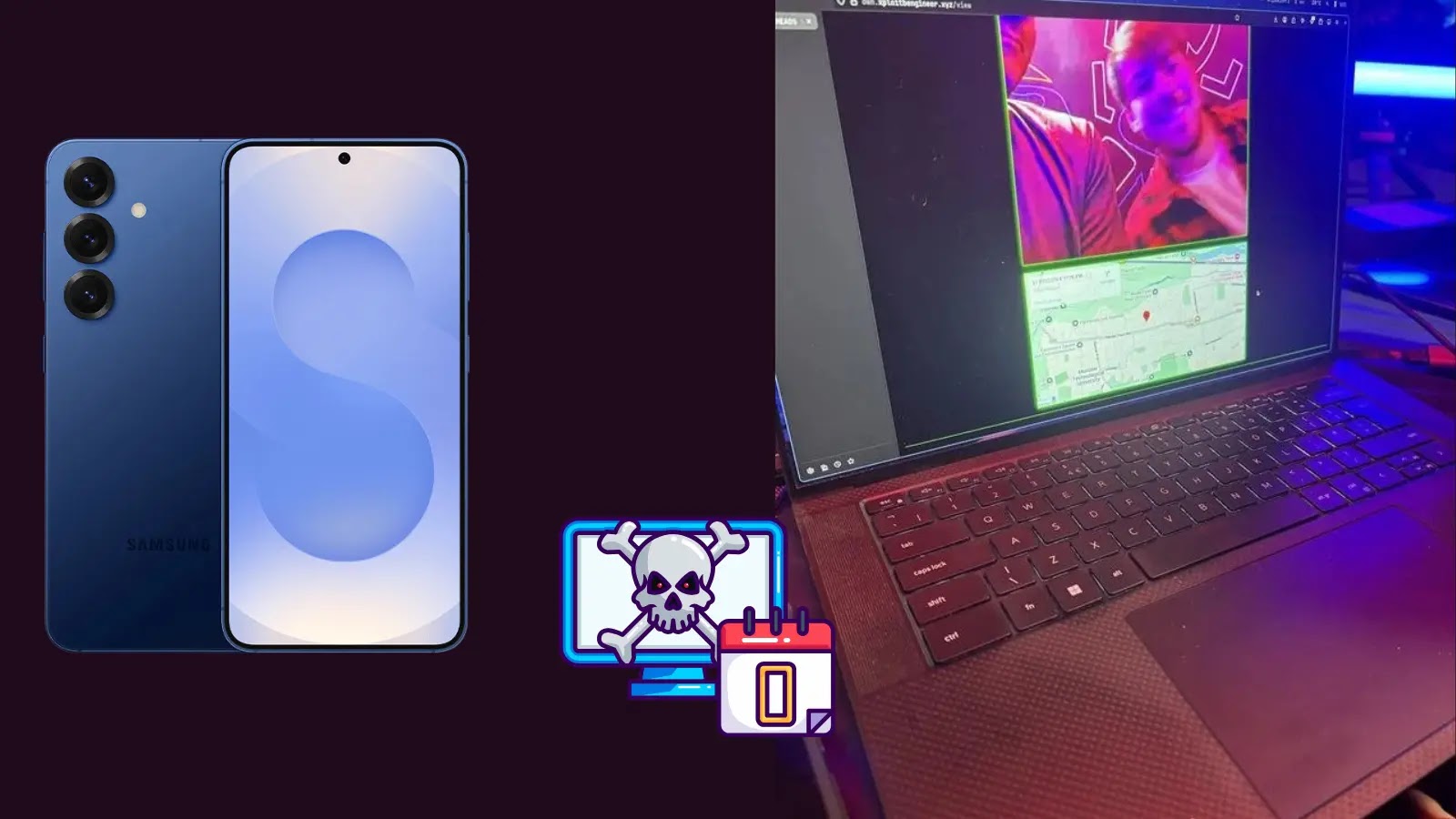
In real-world scenarios, such as a recent investigation by ANY.RUN, phishing emails seemed innocuous upon delivery but evolved into threats post-click. The attack flow typically involves fake invitations leading to credential theft or the deployment of remote management tools.
To counteract such threats, SOCs and Managed Security Service Providers (MSSPs) utilize ANY.RUN’s interactive sandbox for behavior-based analysis. This tool allows teams to safely examine the complete phishing pathway, from redirects to fake login screens, within a secure environment.
This approach enhances the speed and accuracy of threat confirmation, reduces time spent on ambiguous alerts, and helps determine the need for containment, thereby providing clearer evidence for decision-making.
Organizations employing behavior-based analysis report significant improvements, including faster threat validation, reduced MTTR (Mean Time to Resolution), and decreased workload for security teams. By enhancing phishing response capabilities, security teams can prevent missed emails from escalating into larger business incidents.