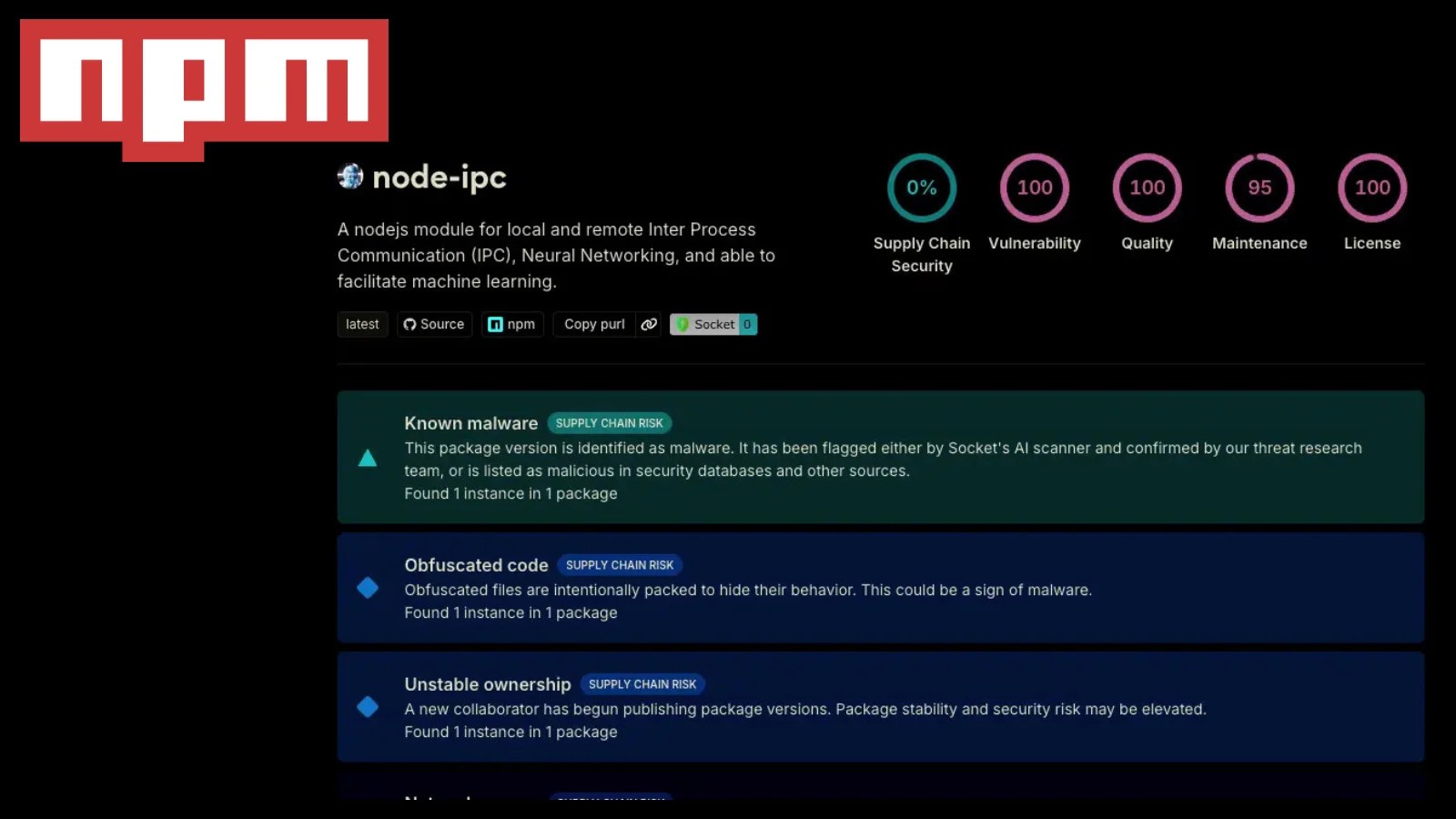
The node-ipc npm package, a crucial JavaScript library, has once again been compromised. According to reports from Socket and Stepsecurity, three recent versions of this widely-used package, with over 822,000 weekly downloads, have been found to include obfuscated malicious code. This marks the second significant breach of the node-ipc package since 2022.
Details of the Compromised Versions
The affected versions include [email protected], [email protected], and [email protected]. Security researcher Ian Ahl (@TekDefense), CTO at Permiso, identified a dormant maintainer account as the likely attack vector. The attacker exploited this vulnerability by re-registering a lapsed domain, which allowed unauthorized access to the package’s publishing rights.
The malicious components are embedded within the CommonJS entrypoint, node-ipc.cjs, through an obfuscated IIFE. However, the ESM module remains unaffected. Developers utilizing the require(“node-ipc”) function are primarily at risk, whereas purely ESM users may remain unaffected.
Technical Breakdown of the Attack
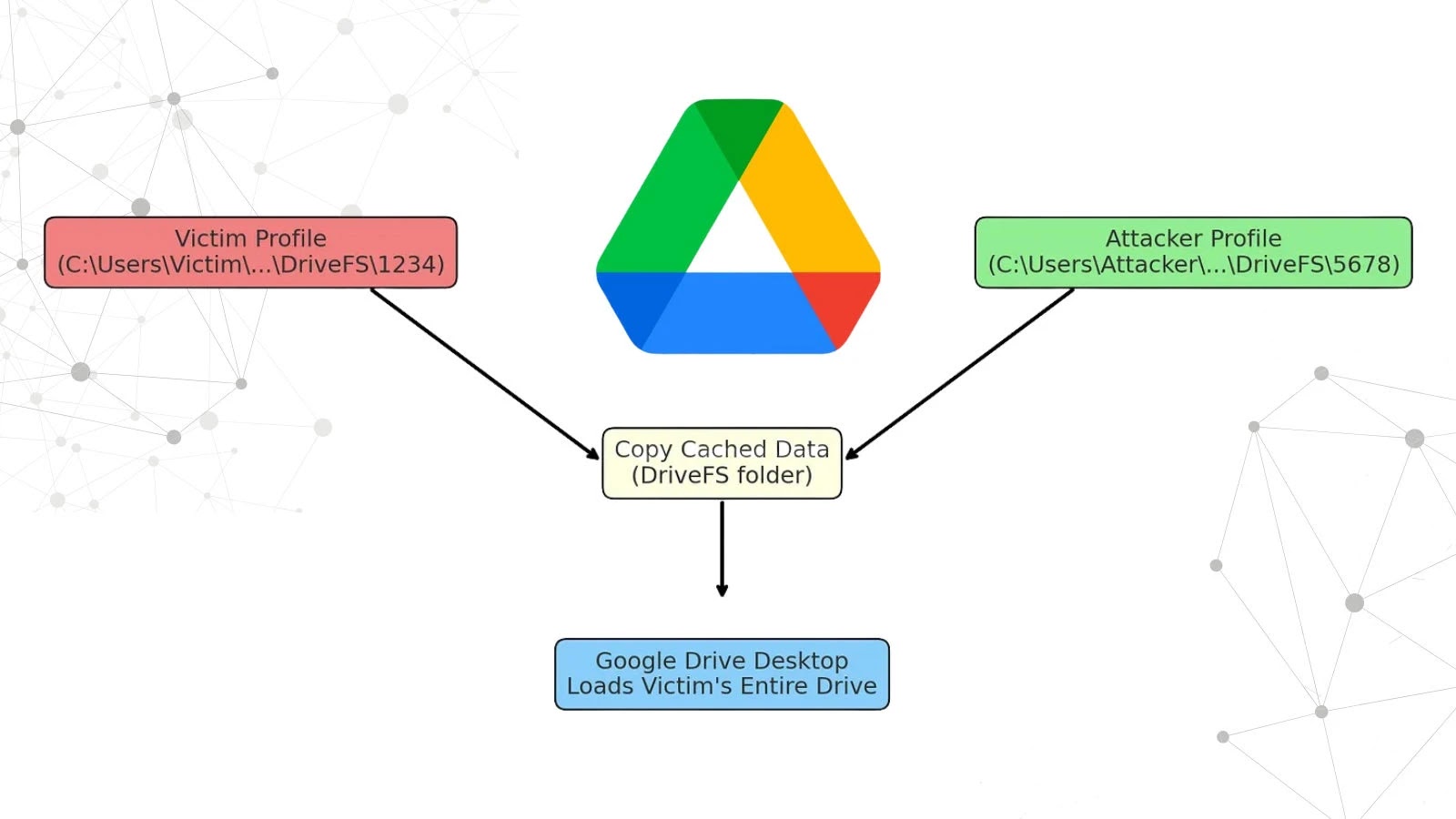
The payload activates upon module load, leveraging setImmediate() to fork a detached process. It collects host fingerprints through OS metadata and harvests credentials and configuration files from over 100 different patterns, including AWS, Azure, GCP, and more. The harvested data is archived into a gzip tarball and exfiltrated via DNS TXT queries using a deceptive Azure-like domain.
The exfiltration method can generate a substantial number of DNS TXT queries, serving as a potential detection signal. Additionally, all files in the malicious tarballs are marked with a forensic timestamp of October 26, 1985, aiding in identifying compromised copies.
Response and Recommendations
Developers are urged to immediately uninstall the compromised versions and thoroughly audit package-lock.json, yarn.lock, and local npm caches. Any exposed environment variables or credentials should be considered compromised and rotated promptly. Security teams should monitor DNS TXT query traffic and block the malicious resolver domain.
This incident underscores the importance of maintaining vigilant security practices within the software development lifecycle. Staying informed and proactive is crucial to safeguarding against such sophisticated attacks.
For more updates on this situation, follow our channels on Google News, LinkedIn, and X.