A classy Russian-aligned menace actor generally known as Hive0156 has intensified its cyber espionage campaigns towards Ukrainian authorities and army organizations, deploying the infamous Remcos Distant Entry Trojan by means of rigorously crafted social engineering assaults.
The group has demonstrated outstanding persistence in focusing on Ukraine’s protection infrastructure all through 2025, using weaponized Microsoft LNK information and PowerShell scripts as major assault vectors.
The menace actor’s operations signify a major escalation in cyber warfare techniques, with attackers leveraging extremely relevant-themed decoy paperwork to entice victims inside Ukraine’s protection institution.
These malicious campaigns exploit the continued battle by incorporating themes resembling battalion readiness checks, wartime casualties, and operational employees distribution to maximise the probability of profitable infiltration.
IBM analysts recognized that Hive0156’s Instruments, Ways, and Procedures strongly overlap with CERT-UA’s UAC-0184 actor, suggesting coordinated efforts inside Russia’s cyber operations framework.
The group has advanced its focusing on technique from completely army personnel to a broader viewers, incorporating themes associated to petitions and official correspondence in current campaigns.
Latest evaluation reveals that Hive0156 has simplified its supply mechanisms whereas sustaining operational effectiveness.
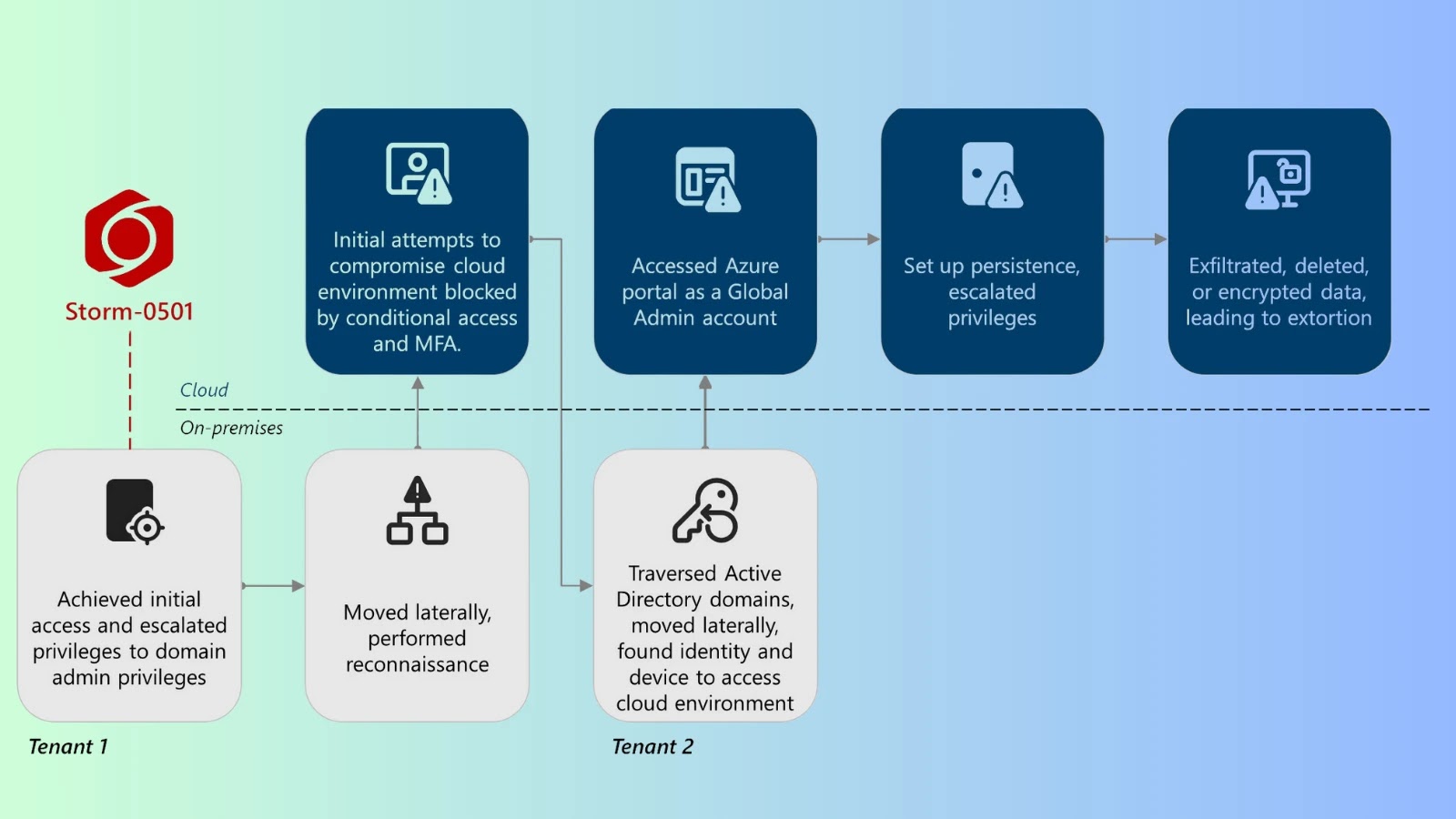
The assault chain begins with weaponized first-stage LNK or PowerShell information that set up communication with command-and-control infrastructure.
Upon profitable connection, the malware retrieves each a decoy doc and a compressed archive containing malicious elements.
Subtle Multi-Stage An infection Mechanism
The group’s an infection methodology demonstrates superior technical sophistication by means of its deployment of HijackLoader, often known as IDAT Loader, which serves as the first supply mechanism for Remcos RAT.
Hive0156 assault chain (Supply – IBM)
The HijackLoader package deal accommodates 5 crucial elements working in live performance to evade detection and set up persistent entry.
The an infection begins when victims execute PortRemo.exe, a authentic signed executable that masses the malicious sqlite3.dll file.
This patched Dynamic Hyperlink Library accommodates code that initiates the HijackLoader sequence by calling the compromised sqlite3_result_text16() perform.
The malware employs export desk manipulation to hinder static evaluation instruments like IDA Professional from correctly inspecting the file construction.
sqlite3_result_text16() → Malicious perform name
↓
Decrypt first-stage shellcode
↓
Course of PNG file containing HijackLoader modules
↓
Execute remaining Remcos payload
The encrypted PNG file, randomly named in every marketing campaign, accommodates a number of HijackLoader modules together with AVDATA for safety software program detection, ESAL for payload execution, and rshell for reminiscence administration.
These modules work collectively to inject the ultimate Remcos payload right into a distant course of, establishing covert communication channels with the attackers’ command-and-control servers spanning a number of geographic places.
Hive0156 operates marketing campaign identifiers together with hmu2005, gu2005, ra2005, and ra2005new, suggesting organized operational administration.
The group maintains geofencing restrictions limiting infections to Ukrainian IP addresses whereas filtering connections primarily based on anticipated user-agent strings, demonstrating exact focusing on capabilities that maximize operational safety whereas minimizing publicity to safety researchers.
Expertise quicker, extra correct phishing detection and enhanced safety for your small business with real-time sandbox analysis-> Attempt ANY.RUN now