A cyber threat actor known as “Mr. Raccoon” has reportedly infiltrated Adobe’s systems, claiming to have extracted a vast amount of sensitive information. This includes approximately 13 million support tickets with personal details, around 15,000 employee records, as well as comprehensive internal documents and bug bounty submissions from HackerOne, according to a report by International Cyber Digest.
Supply Chain Vulnerability Exploited
The breach allegedly did not originate directly from Adobe’s network. Instead, Mr. Raccoon is said to have leveraged access through a Business Process Outsourcing (BPO) company in India contracted by Adobe. This method underscores the increasing risks associated with third-party vendor relationships in cybersecurity.
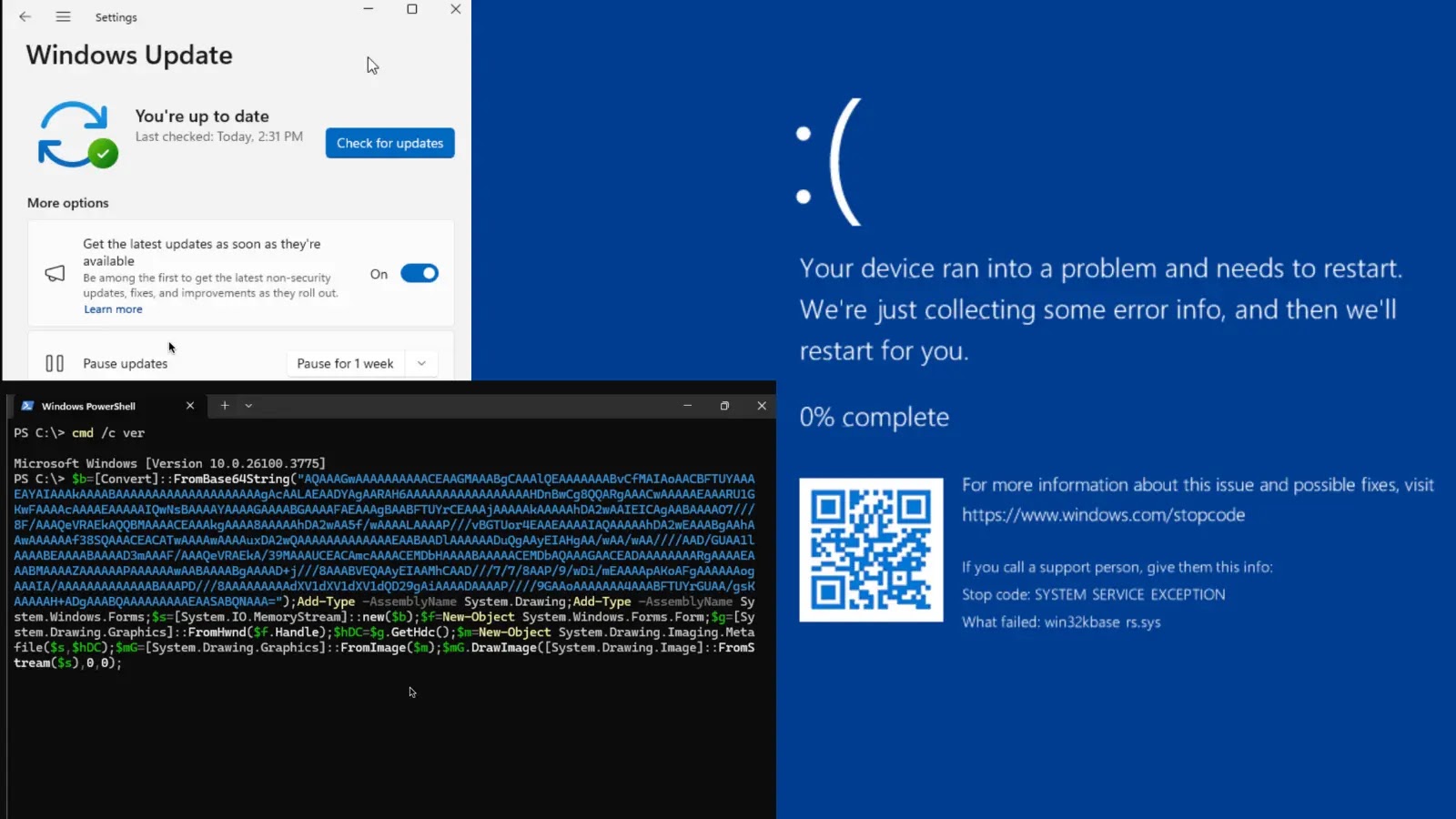
The attacker supposedly used a Remote Access Tool (RAT) delivered via a malicious email to a BPO employee. Upon securing initial access, Mr. Raccoon escalated privileges by targeting the employee’s manager through phishing, thereby widening their network control.
Security Flaws and Data Exposure
The deployment of the RAT reportedly also enabled the attacker to gain webcam access and intercept private communications, such as those on WhatsApp. This breach highlights a concerning security lapse in Adobe’s support ticketing system. Mr. Raccoon claimed that the platform allowed them to export all tickets in a single request, indicating a significant misconfiguration in access controls.
The dataset obtained is particularly sensitive, as support tickets often contain customer names, emails, account details, and technical issue descriptions. Such information is highly valuable for phishing attacks and identity theft. Furthermore, the exposure of HackerOne submissions poses a risk, as these contain undisclosed vulnerabilities that could be exploited if not addressed promptly.
Potential Impact and Precautions
At this time, Adobe has not officially confirmed the breach. Should the claims be validated, it would mark a significant data exposure event for 2026, raising critical concerns about third-party vendor security assessments and data management practices within support environments.
Security professionals are urged to review their own vendor access protocols, audit permissions for bulk data exports, and remain vigilant for any credentials or vulnerabilities from this alleged breach surfacing on dark web platforms.
Note: This article is based on unverified information from International Cyber Digest. As of now, Adobe has not confirmed the details of the breach.
Stay updated with the latest cybersecurity news by following us on Google News, LinkedIn, and X. Contact us to feature your cybersecurity stories.