An elaborate cyber attack masquerading as a Boeing Request for Quotation (RFQ) email has been targeting industrial suppliers and procurement teams. The operation, known as NKFZ5966PURCHASE, uses a deceptive Word document to initiate a sophisticated malware sequence.
Disguised as a procurement request from an individual named ‘Joyce Malave,’ the campaign entices recipients into opening a harmful DOCX file. This document sets off a complex attack chain that ultimately deploys Cobalt Strike, a potent post-exploitation tool, directly into the computer’s memory, leaving minimal evidence of intrusion.
The Onset of the Malware Campaign
First detected on March 30, 2026, by security researcher @JAMESWT_WT, the suspicious activity was linked to a DOCX file shared on X. Within a short period, multiple samples appeared on MalwareBazaar under the same campaign identifier. By April 1, three distinct versions of the malicious document were discovered, all exhibiting the same metadata, encryption protocols, and attack structure, indicating the campaign’s swift expansion.
BreakglassIntelligence analysts uncovered the full six-stage attack process, which involves DOCX, RTF, JavaScript, PowerShell, a complete Python runtime, and an AES-256 encrypted DLL. Remarkably, this chain operates without leaving a conspicuous file on the system, complicating detection efforts.
Social Engineering and Document Variations
The attackers employ straightforward social engineering techniques, impersonating ‘Joyce Malave from BOEING’ or ‘Global Services, LLC’ to engage procurement and sales departments with requests for competitive pricing on large orders. Three variants of the lure document have been identified: ‘Rfq and Payment Schedule.docx,’ ‘Product_specifications.docx,’ and ‘RFQ_PO_ATR29026II.docx,’ all containing the identical attack mechanism.
Originally created in April 2021, the base document was weaponized in January 2026, retaining its author information throughout the process. Once Cobalt Strike is executed in memory, the attacker gains full control over the compromised device, facilitating data theft and network infiltration.
Understanding the Six-Stage Attack Process
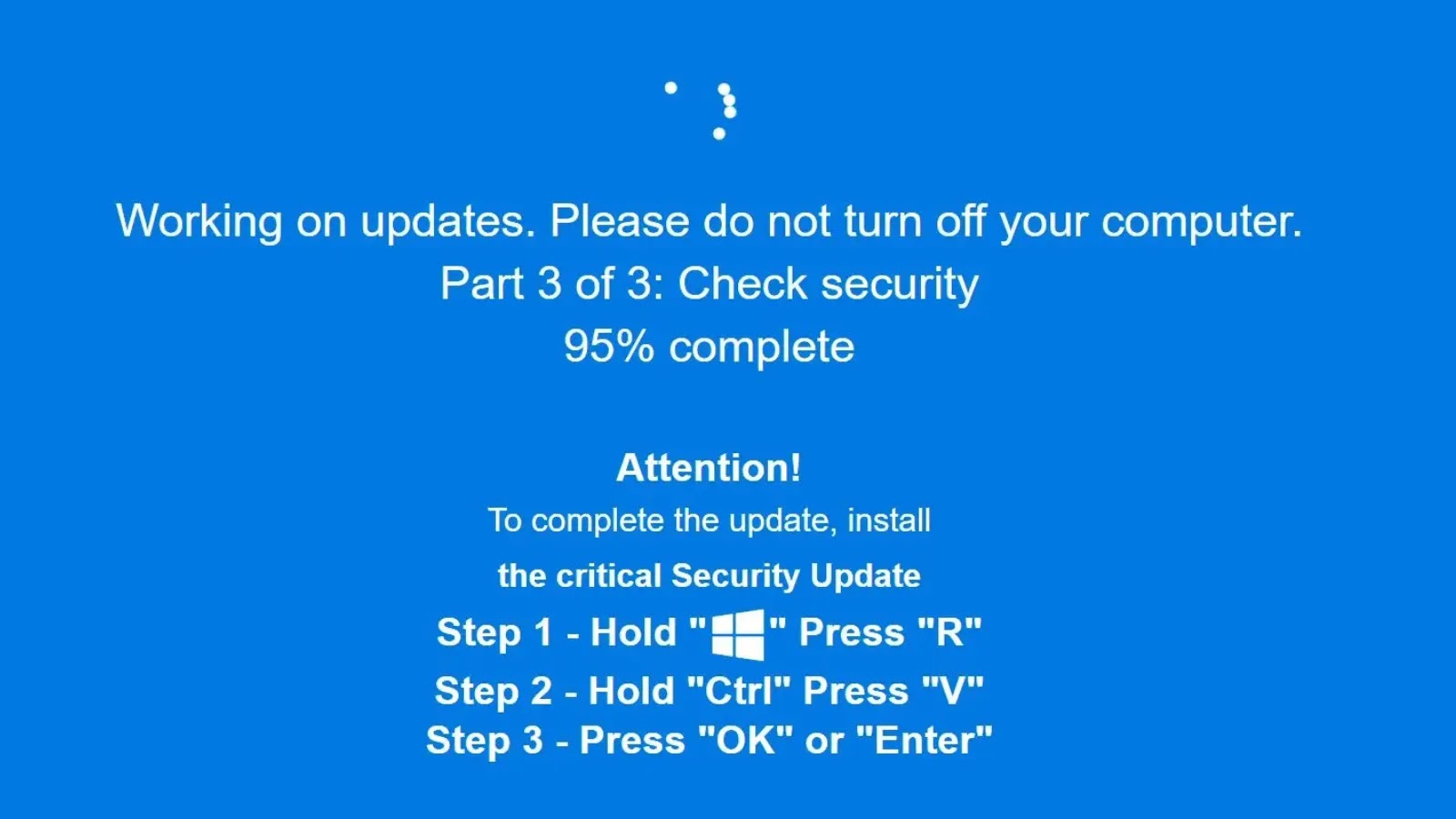
The infection commences when the victim opens the DOCX file, which contains an embedded RTF file that Word loads silently. Although this technique has been utilized since 2017, its effectiveness persists due to the limitations of email security systems, which often fail to scan beyond the surface of DOCX files.
Within the RTF, a concealed JavaScript file executes, using various techniques to avoid detection. This script triggers PowerShell to operate in a hidden window, bypassing security checks, and downloads a ZIP file from Filemail.com. The ZIP file masquerades as an .mp3 and contains a Python runtime that executes a heavily obfuscated script, ultimately decrypting a DLL file loaded into memory.
Security experts advise monitoring for suspicious registry keys and blocking associated URLs to mitigate the threat potential of such attacks. Additionally, vigilance in scanning DOCX files for embedded threats remains crucial.
Stay informed with our updates by following us on Google News, LinkedIn, and X, and make CSN your preferred source for cybersecurity news.