An Iranian-backed cyber group, Boggy Serpens, also referred to as MuddyWater, has significantly ramped up its espionage activities in recent months. This group has been targeting diplomatic entities, energy firms, maritime operators, and financial institutions in a coordinated cyber offensive. Known to be associated with Iran’s Ministry of Intelligence and Security (MOIS), Boggy Serpens has been in operation since 2017. However, its recent activities showcase a notable advancement in both their strategic approach and technical capabilities.
Strategic Evolution and Technical Enhancements
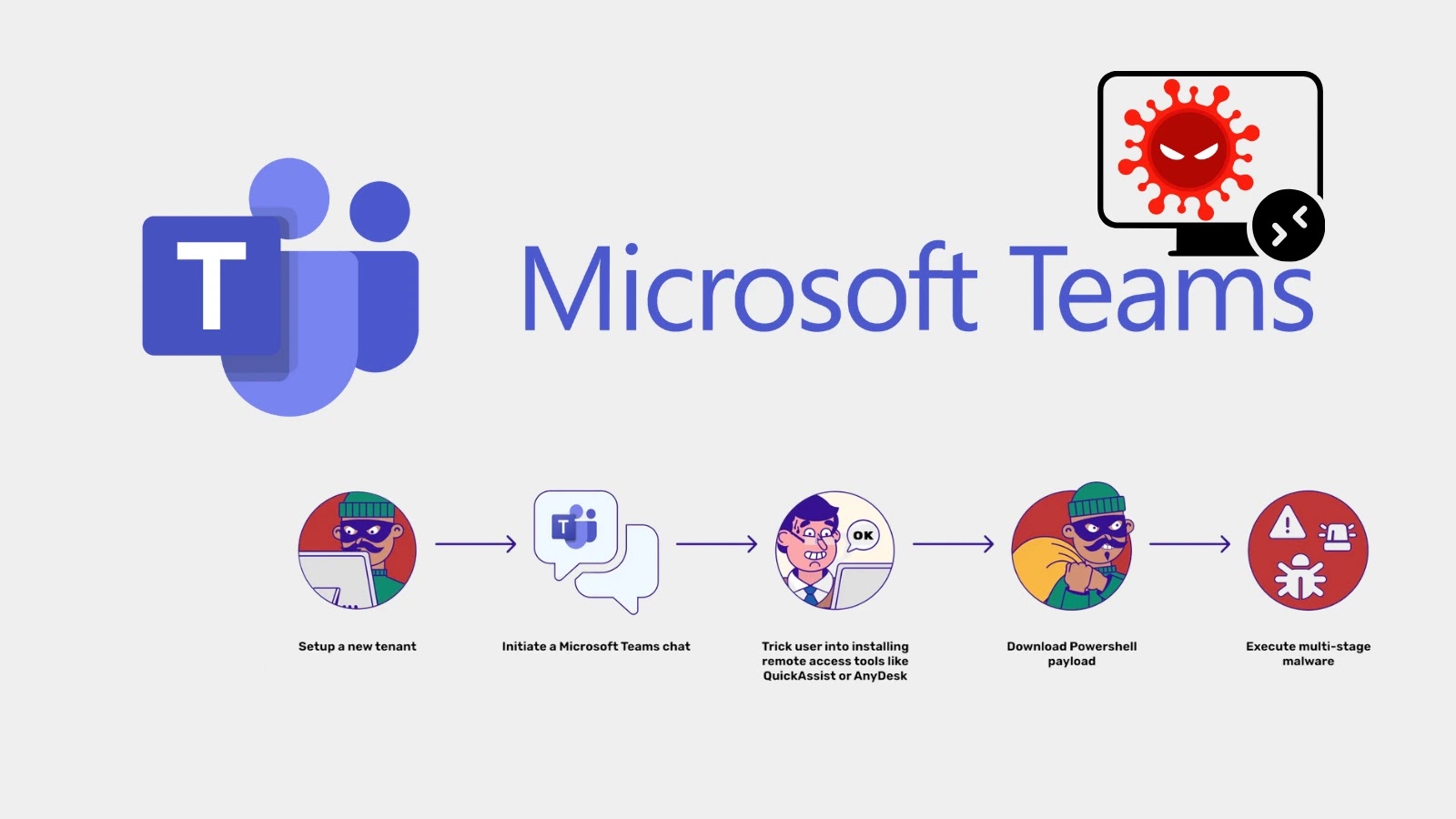
Historically, Boggy Serpens employed loud and high-volume spear-phishing campaigns, focusing more on speed than stealth. Their tactics included the use of remote monitoring tools like Atera and ScreenConnect, as well as utilities such as LaZagne and CrackMapExec. Initially, these campaigns were broad and lacked sophistication. However, the group has since transitioned to more calculated operations.
Recent analyses by Unit 42 have highlighted a significant shift in the group’s behavior, with a move towards long-term persistence and the compromise of trusted relationships. Boggy Serpens now utilizes custom implants created with Rust, a language known for its memory safety, complicating reverse engineering efforts. Furthermore, they have incorporated generative AI into their development processes to expedite the creation of new malware families.
Wide-reaching Impact and Coordinated Attacks
The group’s campaigns have had a broad geographical impact, affecting entities in Israel, Hungary, Turkey, Saudi Arabia, the UAE, Turkmenistan, Egypt, and South America. These attacks have spanned various sectors, including government, aviation, maritime, and finance. A notable example is a four-wave attack against a UAE-based marine and energy company associated with Saudi Aramco, which persisted from August 2025 to February 2026.
In August 2025, Boggy Serpens exploited a compromised email account at the Omani Ministry of Foreign Affairs to send fake diplomatic invitations to embassies and international organizations under the guise of a ‘Sustainable Peace’ seminar. This campaign illustrates the group’s ability to craft complex social engineering tactics that evade both automated filters and human vigilance.
Advanced Social Engineering Techniques
The group’s two-stage deception model begins with the use of legitimate, hijacked email accounts from government agencies or corporations. Messages from these accounts bypass spam filters due to their authenticated origins. Such tactics were employed against a telecommunications provider in Turkmenistan and Israeli organizations, where the group sent attachments disguised as ‘Cybersecurity Guidelines’ and HR-related documents.
Upon opening the attachment, the victim is prompted to ‘Enable Content,’ triggering a VBA macro that silently installs a payload, subsequently revealing a convincing document. This sophisticated approach ensures the victim perceives the interaction as routine and secure.
To mitigate these threats, organizations are advised to enforce strict macro execution policies and implement behavioral endpoint monitoring. Multi-factor authentication should be mandatory for all email accounts to minimize hijacking risks. Additionally, email controls that evaluate behavioral patterns beyond sender reputation are essential for detecting internal phishing attempts.
Regular threat hunting for UDP-based communications, process injections, and unusual registry modifications can help identify and neutralize active threats before they establish persistent access.