A crucial distant authentication bypass vulnerability has been disclosed in GNU InetUtils affecting the telnetd server element.
The flaw, reported by a safety researcher on January 19, 2026, permits unauthenticated attackers to realize root entry by exploiting improper enter sanitization within the telnetd authentication mechanism.
The vulnerability stems from how telnetd invokes the login program. When a telnet shopper connects, telnetd receives a USER atmosphere variable from the distant shopper and passes it on to /usr/bin/login with out sanitization.
An attacker can craft a malicious USER atmosphere variable containing the string “-f root”, a parameter that login (1) interprets as a flag to bypass routine authentication procedures.
By sending a telnet reference to the specifically crafted USER atmosphere variable utilizing telnet’s -a or –login parameter.
An unauthenticated distant person bypasses the login authentication system solely and positive factors quick root-level entry to the system.
The vulnerability was inadvertently launched throughout a code modification on March 19, 2015, and was included in GNU InetUtils model 1.9.3 launched on Could 12, 2015
The flaw has persevered by means of all subsequent variations as much as and together with model 2.7. GNU InetUtils variations 1.9.3 by means of 2.7 are weak.
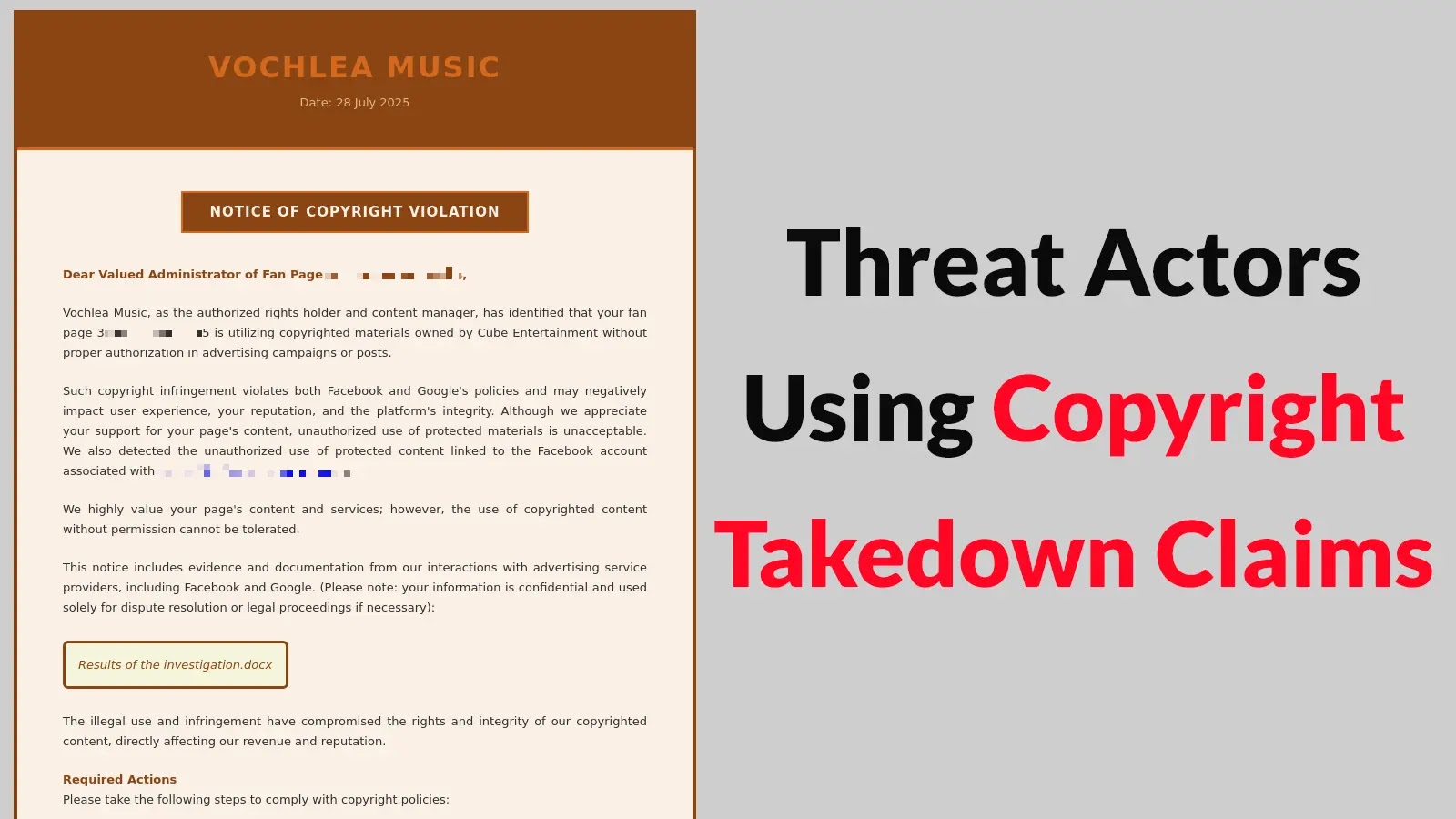
In accordance with OpenWall, organizations working telnetd from GNU InetUtils ought to instantly assess their publicity. GNU maintainers advocate three approaches:
ApproachDescriptionDisable telnetdTurn off telnet resulting from insecurity (most well-liked)Prohibit accessAllow solely trusted clientsUpgrade softwareApply patches by Eggert & Josefsson
This vulnerability demonstrates the persistent dangers related to legacy protocols like telnet.
The authentication bypass permits full system compromise with root privileges, making this a crucial safety risk for any system that exposes telnetd to untrusted networks.
Organizations ought to prioritize both updating GNU InetUtils or instantly turning off telnetd. The provision of patches implies that delayed remediation considerably will increase the chance of compromise.
Comply with us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to characteristic your tales.