A critical flaw known as React2Shell has put numerous web applications at risk as hackers exploit this vulnerability in websites using the Next.js framework. Within a mere 24 hours, a staggering 766 hosts were compromised, leading to the theft of valuable credentials such as passwords and cloud access keys.
Understanding the React2Shell Vulnerability
The issue involves CVE-2025-55182, commonly referred to as React2Shell, which has been given a maximum severity score of 10.0 on the CVSS scale. This vulnerability is found in the React Server Components (RSC) Flight protocol and specifically affects how HTTP requests to Server Function endpoints are processed. A single malicious HTTP request can allow attackers to execute code on the server without needing authentication.
In addition to CVE-2025-55182, Next.js itself has been assigned a separate tracking number, CVE-2025-66478, due to the extensive exposure it faces from this flaw. Cisco Talos researchers have linked this attack to a threat group they are monitoring as UAT-10608.
Impact and Methodology of the Attack
The attack campaign is both organized and widespread. Attackers utilize services like Shodan and Censys to identify vulnerable Next.js deployments globally. Once a susceptible target is identified, the exploit is automated, requiring no further human intervention after initiation.
The attack’s impact spans across various regions and cloud platforms, including AWS, Google Cloud, and Microsoft Azure. In just 24 hours, 766 hosts were confirmed compromised, resulting in the theft of over 10,120 files. These included sensitive credentials such as SSH keys, database passwords, and cloud access tokens.
The campaign has significant implications for supply chain security. Breached hosts exposed authentication files for package registries, posing a threat if malicious software versions are distributed.
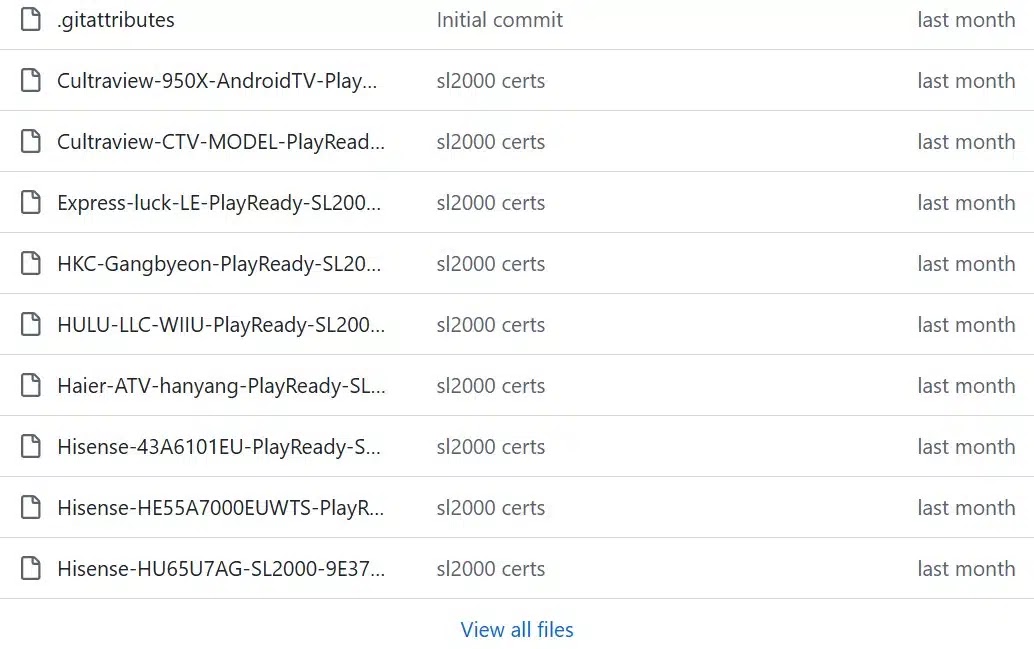
NEXUS Listener: Managing Stolen Data
To handle the vast amount of data collected, UAT-10608 employs a custom command-and-control system called NEXUS Listener. This platform, currently in its third iteration, offers a user-friendly interface for operators to manage compromised credentials and analyze attack statistics.
The attack begins when a vulnerable endpoint is discovered, and a crafted HTTP request is sent, triggering the server to execute arbitrary code. A lightweight script is deployed to retrieve further scripts for credential harvesting, which report back to the NEXUS Listener server.
Organizations using Next.js with the App Router or React Server Components are urged to update to the latest patches immediately. All potentially compromised credentials should be rotated, and security teams are advised to audit for permissive roles and monitor unusual outbound traffic to prevent further breaches.
Stay informed by following us on Google News, LinkedIn, and X for the latest updates. Set CSN as your preferred source on Google to receive more insights on cybersecurity threats.

.webp?ssl=1)