A recent investigation has revealed a significant local privilege escalation vulnerability in the Windows Error Reporting (WER) service, potentially enabling attackers to gain SYSTEM level access.
Nature of the Vulnerability
Identified as CVE-2026-20817, this critical flaw compelled Microsoft to eliminate the susceptible feature entirely, opting against traditional patching methods. The vulnerability resides in the main executable library, WerSvc.dll, of the Windows Error Reporting service.
Researchers Denis Faiustov and Ruslan Sayfiev from GMO Cybersecurity highlighted that the flaw arises from improper permission handling during client request processing. This structural weakness allows a low-privileged user to execute commands at an elevated level.
Exploitation Methodology
Exploiting this flaw involves the attacker connecting to the ALPC port using the NtAlpcConnectPort API and sending a payload through the NtAlpcSendWaitReceivePort API. This requires precise manipulation of the MessageFlags parameter and structural padding to exploit the vulnerable logic.
The vulnerability centers around ALPC messages directed to the WindowsErrorReportingServicePort. An attacker’s crafted message with a File Mapping object can trigger the ElevatedProcessStart function, reading malicious arguments via the MapViewOfFile API, and eventually invoking the CreateElevatedProcessAsUser function, initiating WerFault.exe with SYSTEM privileges under attacker control.
Microsoft’s Response and Security Measures
Microsoft’s approach to resolving this issue involved introducing a private function test that disables the SvcElevatedLaunch functionality altogether. This drastic measure returns an error code, effectively neutralizing the vulnerability by removing the feature from the codebase.
Despite this remediation, attackers can still exploit the flaw by leveraging specific command-line options and advanced Windows techniques to execute arbitrary code. Security solutions like Microsoft Defender are actively detecting and alerting such suspicious activities.
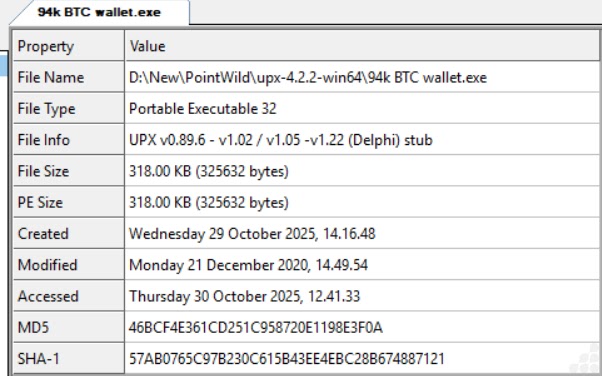
Security analysts have warned of numerous fake proof-of-concept repositories for CVE-2026-20817 appearing on platforms like GitHub. These often contain hidden malware, emphasizing the need for careful analysis of downloaded security tools.
For ongoing updates, follow us on Google News, LinkedIn, and X. Contact us to feature your cybersecurity stories.