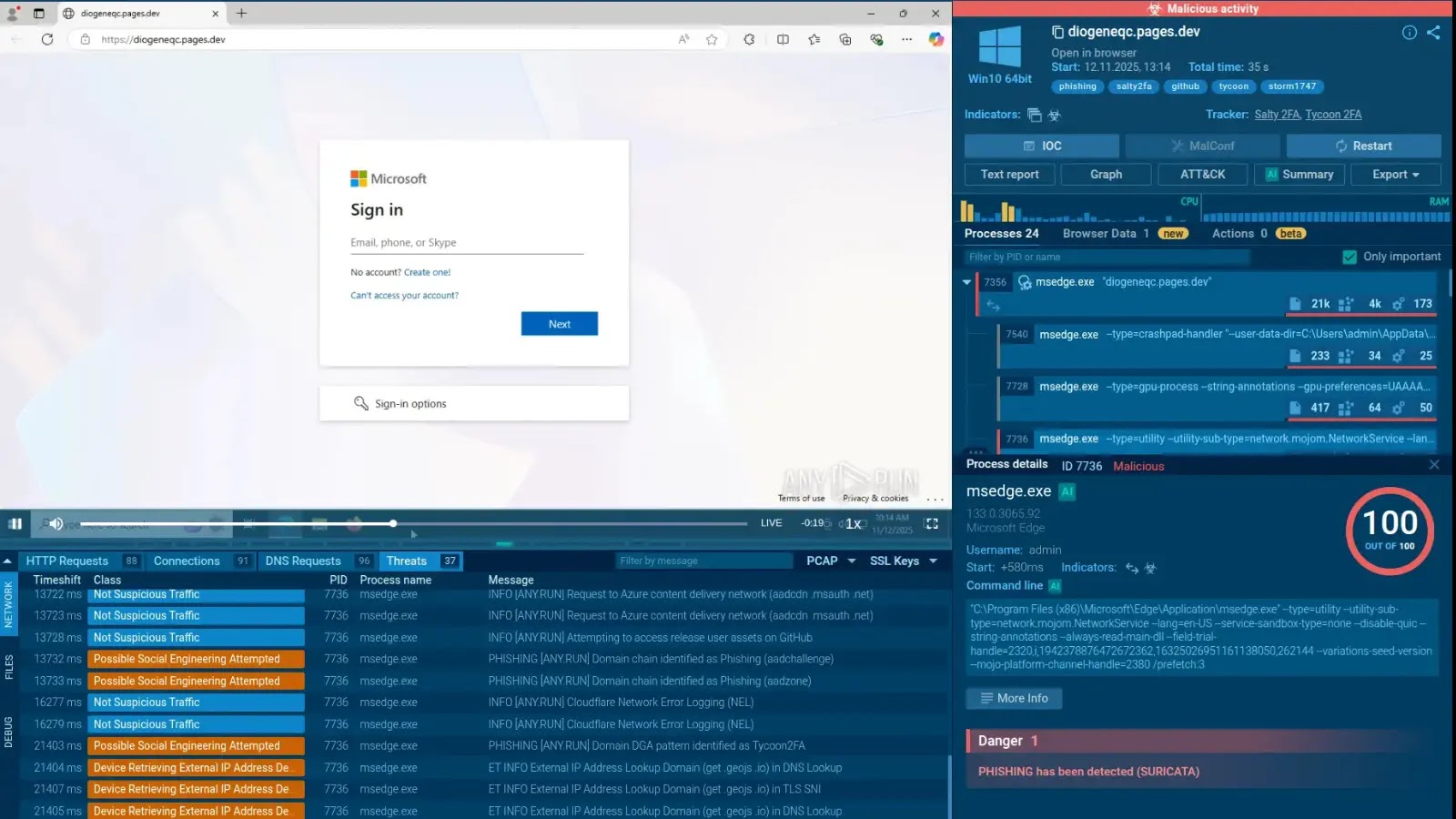
In a significant development, Dutch authorities have confiscated a Windscribe VPN server located in the Netherlands as part of an ongoing investigation. The Canadian VPN provider emphasized its privacy-centric approach, which prevented any data retrieval from the seized server.
Windscribe’s Robust Data Protection
Windscribe revealed the incident through social media, where they shared an image depicting an empty server rack slot, explaining that Dutch officials executed the seizure without prior notification. This particular server was a standard VPN node, physically removed by law enforcement aiming to gather potential logs linked to criminal activities.
Unlike typical data requests where Windscribe asserts its lack of user data, this situation involved direct hardware confiscation. The provider employs RAM-only servers, ensuring that all data is erased upon power loss or reboot. Each time the server restarts, it loads a fresh Ubuntu installation, preventing the storage of any connection timestamps, IP addresses, or browsing activities.
Company’s Transparency and User Trust
Windscribe maintains a real-time transparency report, active since 2018, which documents over 100 law enforcement and DMCA requests. The report highlights responses such as “Can’t Help You” due to the absence of stored logs. These practices are consistent with the findings of independent audits, including one by Packetlabs in 2024, which confirmed Windscribe’s non-identifying logs policy post-infrastructure upgrades.
Despite Canada being part of the Five Eyes alliance, Windscribe has never disclosed user information, supported by their use of open-source applications and cryptocurrency payment options for enhanced anonymity. Users have praised the company’s no-logs policy, viewing it as a testament to strong privacy measures in light of increasing server seizures.
Implications for VPN Providers
This incident highlights the intensifying actions by law enforcement against VPN services, used by both privacy-conscious users and cybercriminals to obscure online traffic. Providers like Windscribe showcase RAM-only and no-logs models as effective defenses, although users are encouraged to verify audits and jurisdictional implications.
Security experts recognize that while RAM disks thwart casual forensic analysis, advanced techniques could potentially capture transient data if a device is powered on. However, such scenarios are considered unlikely in this case. The event underscores the growing scrutiny on VPN infrastructures, testing their resilience while maintaining privacy commitments.
With more than 100 million users, Windscribe’s infrastructure faces ongoing challenges but continues to uphold its privacy assurances. As of now, Dutch officials have not provided further details regarding the investigation.
Stay informed on cybersecurity developments by following us on Google News, LinkedIn, and X. Reach out to feature your stories with us.