In the evolving landscape of cybersecurity, the efficiency of the Security Operations Center (SOC) is critical. A significant challenge faced by many SOCs is the bottleneck at the Tier 1 triage stage, despite having advanced detection tools. The delay in validating alerts can lead to resource wastage, unnecessary engagement of senior teams in low-value cases, and prolonged confirmation times for real incidents. By enhancing Tier 1 with improved visibility, automated workflows, and enriched context, organizations can accelerate decision-making and reduce operational risks.
Challenges in Traditional Tier 1 Triage
Traditional triage processes often require analysts to gather context across multiple platforms manually. This method struggles against modern cyber threats that employ encrypted traffic, fileless techniques, and rapidly changing methods of attack. When Tier 1 teams cannot swiftly differentiate between benign, suspicious, or malicious activities, decision-making is delayed, escalation quality decreases, and active threats may persist longer than necessary. This inefficiency not only raises SOC costs but also extends the time attackers remain undetected, increasing business disruption risks.
Leveraging Interactive Sandboxing for Faster Analysis
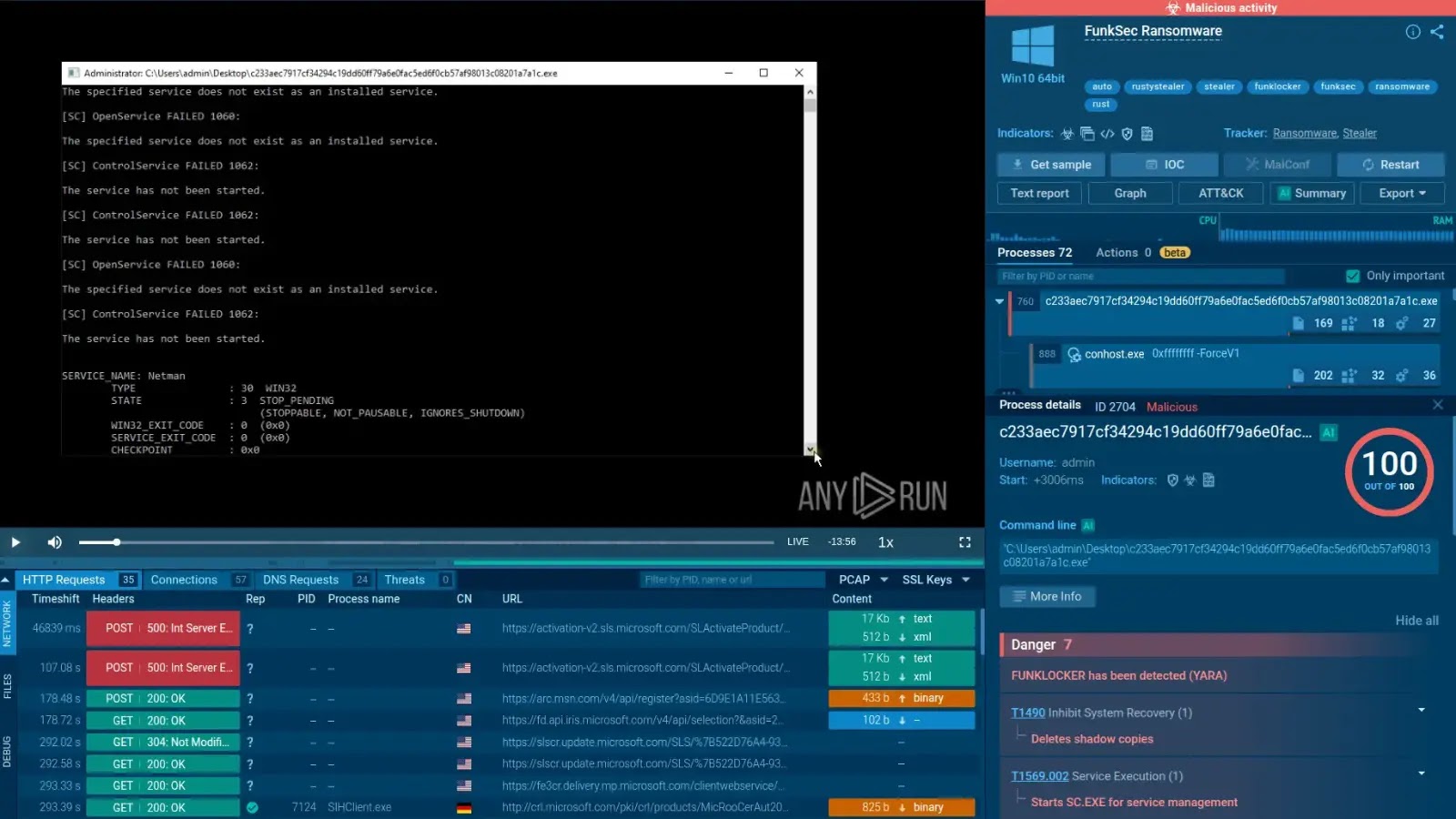
To combat these challenges, many SOCs are adopting interactive sandboxing solutions like ANY.RUN. This tool enhances visibility by decrypting encrypted HTTPS traffic, allowing analysts to examine full network communications. For instance, in a controlled environment, ANY.RUN can extract session keys, providing detailed insights into suspicious activities. A notable example includes analysis of a phishing kit targeting Microsoft 365 accounts, where the sandbox enabled rapid confirmation of malicious intent within just 56 seconds.
This approach allows SOCs to achieve comprehensive attack visibility and quicker verdicts on suspicious activities. It also provides stronger case context for containment and response, effectively transforming the triage process into one driven by evidence and agility.
Automation and Integration for Seamless SOC Operations
Modern threats often require more than basic automation due to their complexity. ANY.RUN addresses this by combining automation with interactivity, handling complex interactions like CAPTCHA checks without constant manual input from Tier 1 teams. Additionally, the platform generates structured reports that summarize the attack chain and key investigation details, streamlining the escalation process and reducing the need for manual documentation.
Integrating ANY.RUN with existing security stacks such as SIEM, EDR, and SOAR platforms further enhances SOC efficiency. This integration ensures that indicators of compromise and behavioral evidence are seamlessly transferred into SOC workflows, enabling faster responses and improved threat context for decision-making.
By utilizing ANY.RUN, organizations report benefits such as reduced Tier 1 workload, fewer escalations to Tier 2, decreased mean time to resolution (MTTR), and lower infrastructure costs. These improvements demonstrate the potential for ANY.RUN to transform Tier 1 into a rapid decision layer that enhances overall SOC performance and minimizes business disruption risks.