Over the weekend, a complicated ransomware assault compromised Collins Aerospace’s Muse check-in and boarding programs, forcing key hubs together with Heathrow, Brussels, and Berlin to return to guide processes.
Airways reported tons of of delayed and cancelled flights as safety groups raced to comprise the breach, restore encrypted knowledge, and deploy software program patches.
The Guardian said that on Friday night, menace actors deployed a ransomware payload believed to be a variant of the REvil/Sodinokibi household towards Collins Aerospace’s digital machines in its cloud-hosted atmosphere.
Collins Aerospace Techniques Ransomware Assault
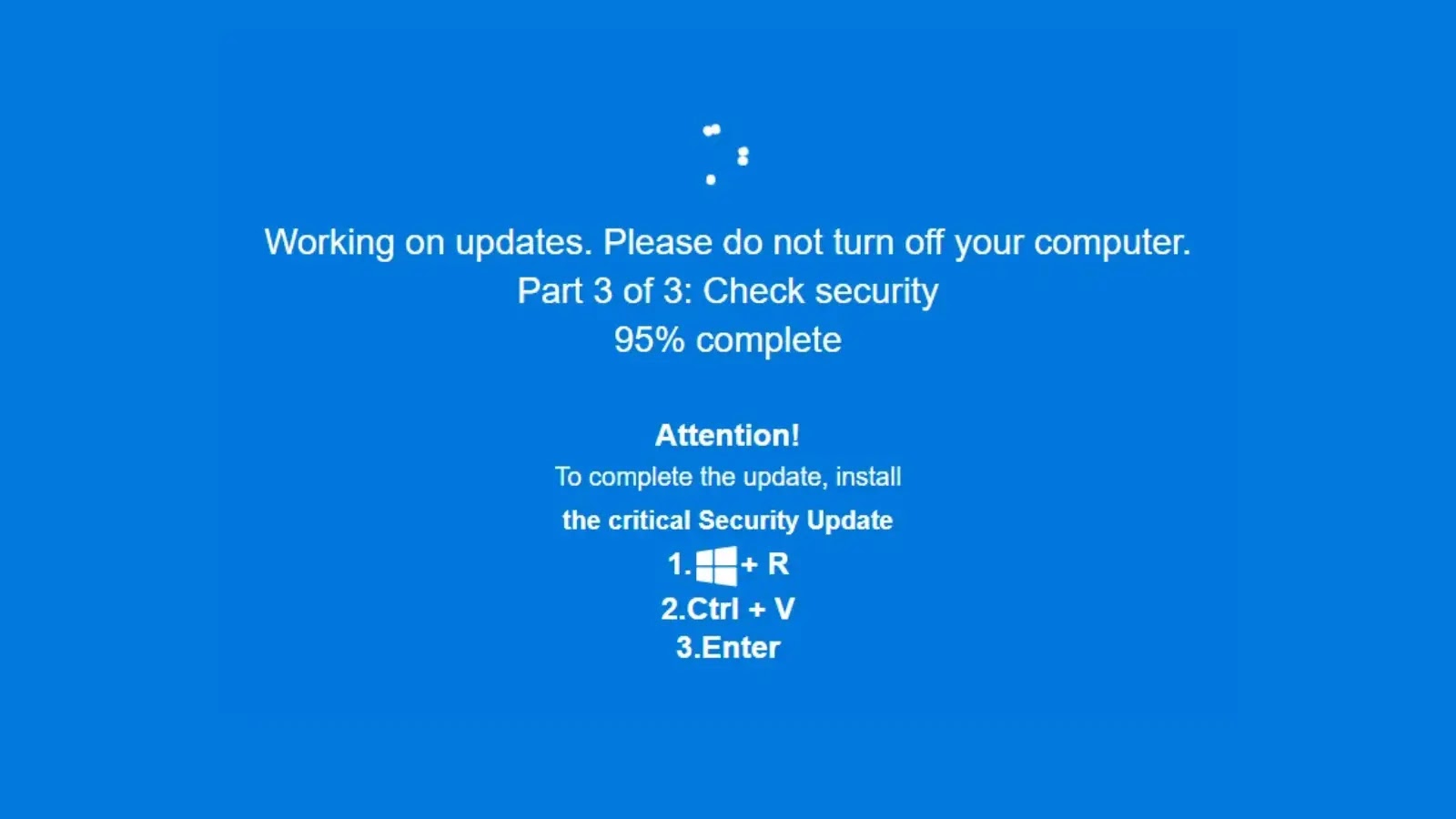
The assault leveraged a spear-phishing e-mail containing a malicious macro, which executed a PowerShell script to obtain the payload from a command-and-control (C2) server.
As soon as lively, the ransomware used AES-256 encryption to lock file shares and digital disks, appending the extension “.locked” and dropping a ransom word demanding cost in Monero.
Preliminary forensic evaluation signifies the intruders exploited a zero-day vulnerability within the Citrix ADC equipment to achieve a foothold, earlier than escalating privileges through Home windows Registry modifications and deploying Mimikatz for credential harvesting.
Lateral motion was detected throughout the community utilizing SMB and RDP protocols, with persistence established by way of scheduled duties and modified Group Coverage Objects (GPOs).
The European Union Company for Cybersecurity (ENISA) confirms that Collins Aerospace skilled file encryption on its main Area Controllers, propagating the influence to airport kiosks, bag-drop programs, and boarding gates.
Whereas Collins Aerospace works on decryptor utilities and hotfixes, airport operators have applied guide check-in counters and paper boarding passes, extending passenger processing occasions by as much as two hours, Guardian stated.
Heathrow experiences that “the overwhelming majority of flights are working as regular, though check-in could take longer than regular.”
Brussels Airport cancelled 40 departing and 23 arriving flights on Monday alone, and Dublin warned of potential future disruptions regardless of no instant cancellations.
Jonathan Corridor KC, the UK authorities’s impartial terrorism laws reviewer, has prompt {that a} state-sponsored actor doubtlessly leveraging superior persistent menace (APT) ways might be behind the breach.
Nonetheless, Collins Aerospace has not publicly attributed the assault to any group. In its Monday assertion, RTX, the mum or dad firm, affirmed that “system integrity is being verified” and urged prospects to use the newest Muse software program replace (model 7.4.2).
Passengers are suggested to confirm flight standing on-line and arrive not more than three hours earlier than long-haul departures and two hours earlier than short-haul companies.
Observe us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to characteristic your tales.