The notorious cybercriminal group Funnull has made headlines again with their latest exploit, the RingH23 toolkit, which is targeting CDN nodes and the MacCMS content management system. This new development has escalated their operations, redirecting unsuspecting users to illegal websites at an alarming scale.
Funnull’s Evolution and New Threats
Funnull, also known as Fangneng CDN, has a long history of involvement in Southeast Asia’s cybercrime scene. Although registered as a legitimate CDN provider in the Philippines, the group has been linked to major scams, including fraudulent investment schemes resulting in losses over $200 million. Despite being sanctioned by the U.S. Treasury in May 2025, Funnull has resurfaced with a more sophisticated approach.
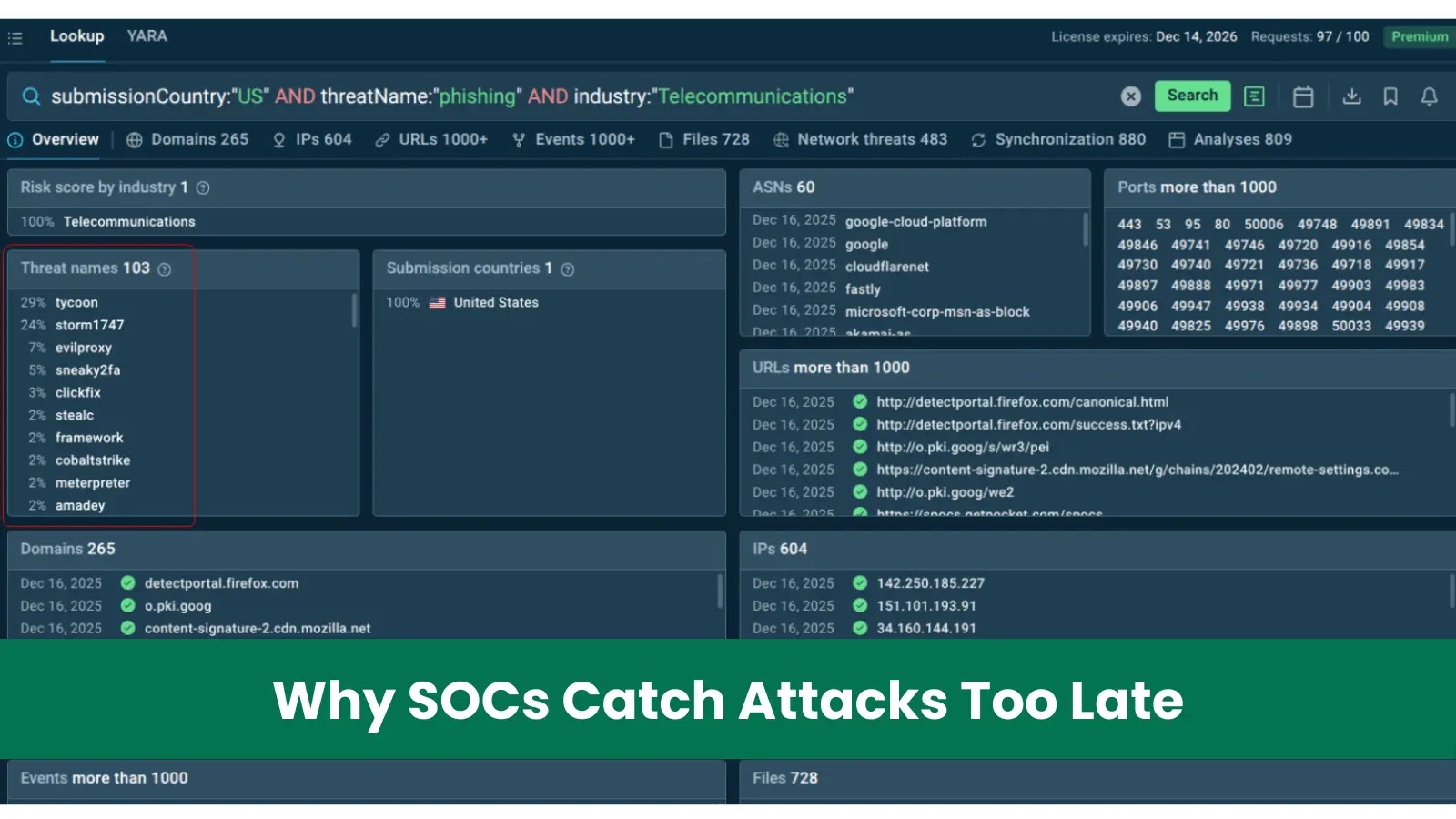
XLab analysts first detected the group’s renewed activities in July 2025. Their Cyber Threat Insight and Analysis System (CTIA) identified a suspicious ELF binary from the domain download.zhw[.]sh, which had evaded detection on VirusTotal. The domain client.110[.]nz recorded an unprecedented 1.6 billion DNS resolutions, indicating a widespread operation rather than isolated incidents.
Infection Strategies and Techniques
Funnull employs two primary infection strategies. The first involves compromising GoEdge CDN management nodes to execute remote SSH commands, deploying the RingH23 toolkit. In the second method, they compromise the maccms.la update channel, inserting a malicious PHP backdoor that activates upon the administrator’s first login, evading forensic analysis by expiring the payload link shortly.
XLab’s telemetry data revealed over 10,748 infected IP addresses, mostly from streaming sites. One spoofed domain imitating Cloudflare amassed 340,000 unique visits in a single day, highlighting the massive reach of this operation. Researchers estimate that over one million users are daily subjected to malicious redirects due to this campaign.
Inside the RingH23 Toolkit
The RingH23 toolkit features a modular design, showcasing professional black-market development. The entry point, infect_init, is a Golang-based infector that executes after verifying credentials with a C2 server. It then spreads the download_init stage across connected servers, deploying various payloads including backdoors and rootkits.
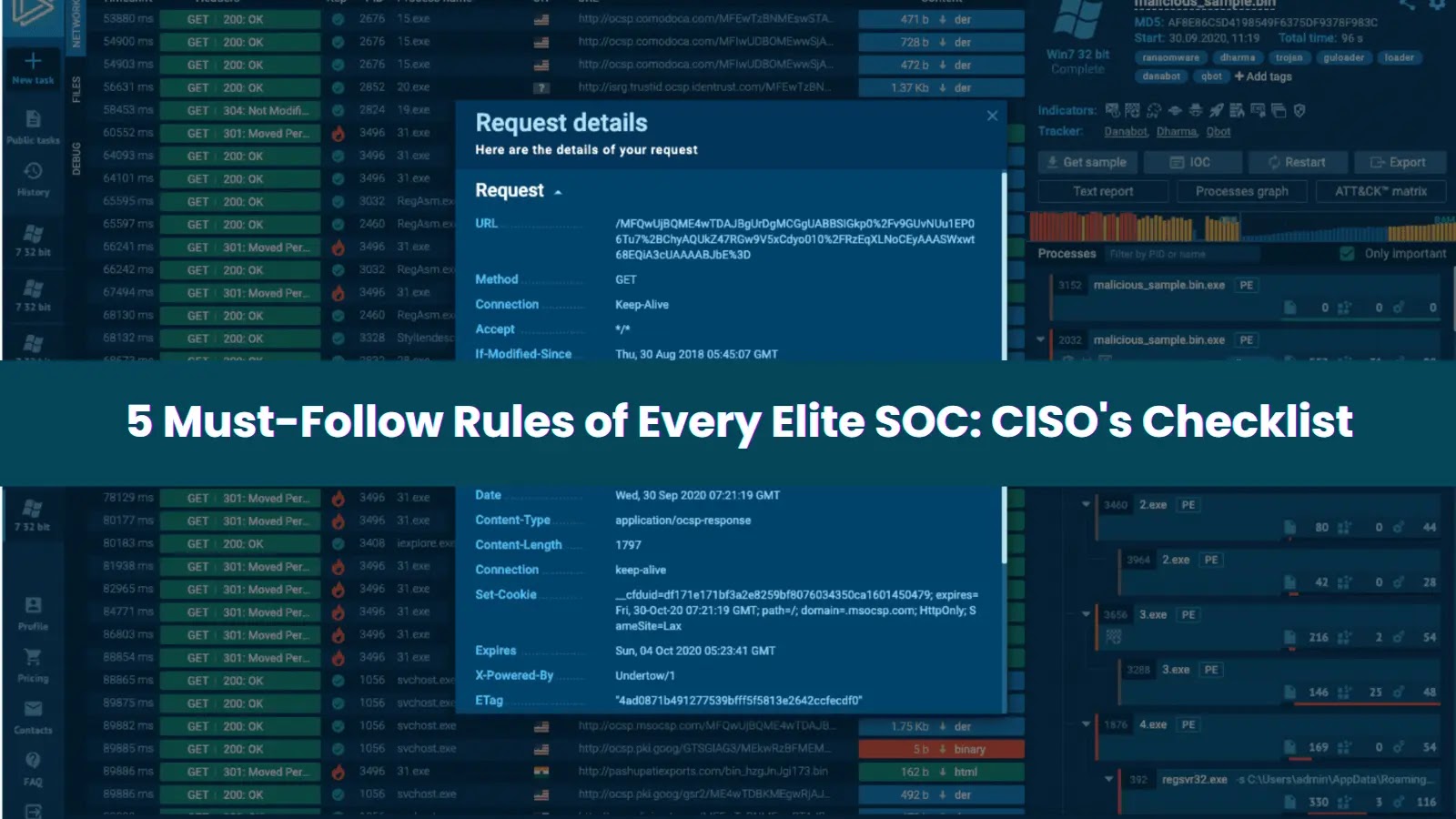
The advanced Badredis2s backdoor uses encrypted WebSocket tunnels to maintain C2 communication, while the Badnginx2s module injects malicious JavaScript into outbound traffic. The Badhide2s rootkit conceals these activities, with defenders advised to set specific environment variables to reveal hidden components.
XLab advises discontinuing the use of maccms.la, auditing server files for malicious injections, and removing specific files to break infection cycles. Stay updated on this evolving threat through our channels on Google News, LinkedIn, and X.