A newly identified malware, GhostSocks, is making waves by converting compromised systems into residential proxies, effectively disguising malicious activities. This malware operates silently on infected devices, causing the traffic from cyber attackers to blend in with normal household internet usage.
Understanding GhostSocks’ Unique Approach
Unlike typical malware that focuses on data theft or file encryption, GhostSocks leverages the victim’s internet connection to mask attacker activities as legitimate traffic. This strategy significantly hinders security measures from identifying malicious behavior, providing cybercriminals with a strategic advantage.
GhostSocks initially appeared on the Russian cybercrime forum xss[.]is, marketed as a Malware-as-a-Service (MaaS) product. Developed in GoLang, it employs the SOCKS5 proxy protocol to establish covert communication channels, utilizing a relay-based command-and-control (C2) system to obscure the true source of the attack.
Rising Threat and Notable Incidents
The malware’s popularity grew in 2024 when it partnered with Lumma Stealer, a prevalent information-stealing malware. This collaboration led to a rapid increase in its adoption within the cybercriminal community. Darktrace experts observed a rise in GhostSocks activities from late 2025, particularly within the education sector where it was detected alongside Lumma Stealer.
GhostSocks is particularly alarming due to its multifunctionality. Beyond routing traffic, it possesses a backdoor capability, allowing cybercriminals to execute commands and deploy further malicious payloads. The ransomware group Black Basta has reportedly used GhostSocks to maintain prolonged, covert access to networks, highlighting its role as more than just a proxy tool.
Evading Detection and Persistent Risks
GhostSocks is designed with evasion in mind, wrapping its communications in Transport Layer Security (TLS) encryption to blend seamlessly with normal encrypted traffic. This makes it challenging for traditional signature-based tools to detect it based solely on traffic patterns.
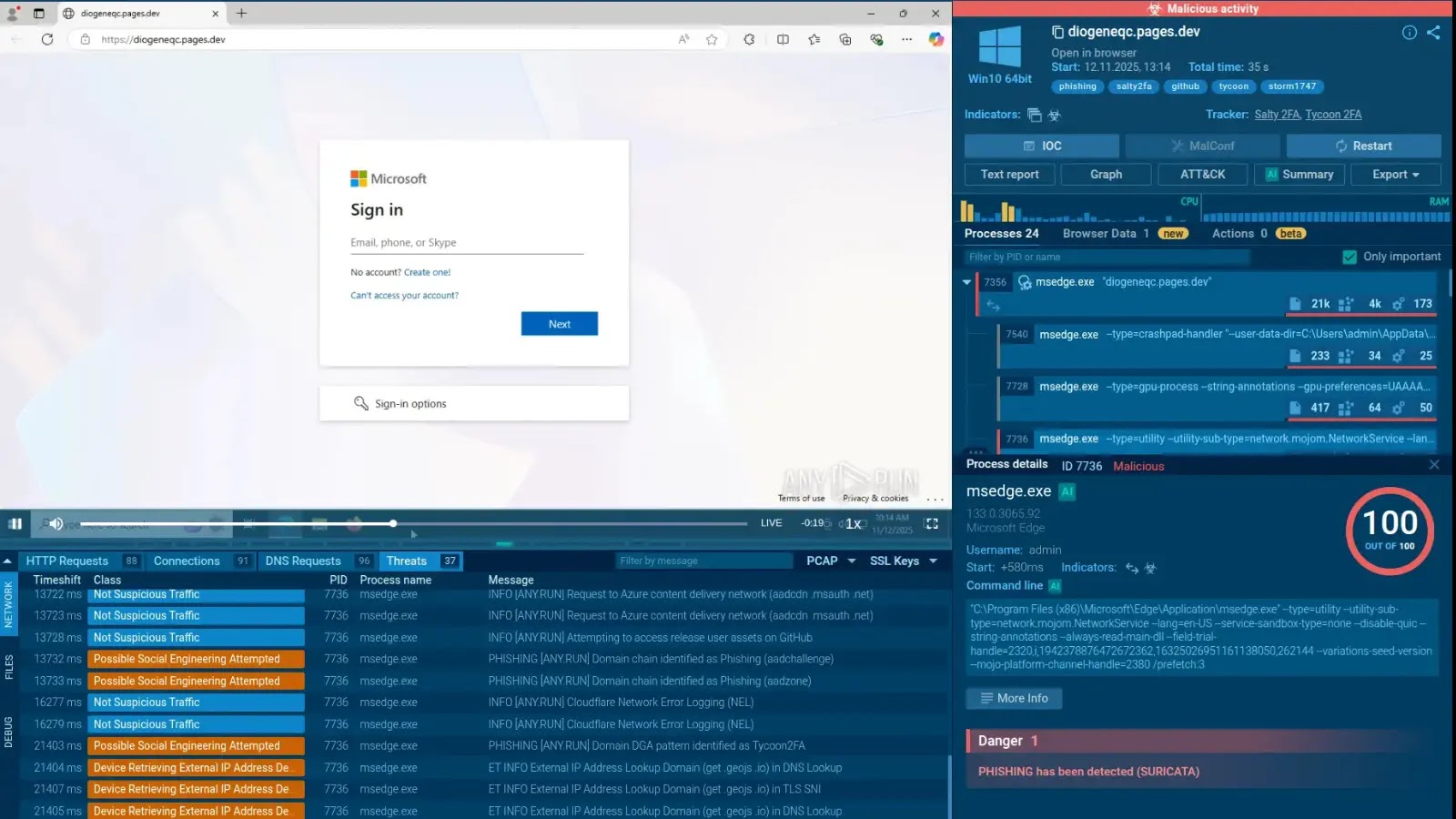
A December 2025 incident revealed GhostSocks’ stealth capabilities when an infected device attempted to connect using an unusual self-signed SSL certificate. This connection led to the download of a file named “Renewable.exe,” linked to GhostSocks, as confirmed by multiple OSINT sources.
Countermeasures and Future Outlook
To counter GhostSocks, security teams are advised to monitor connections to uncommon endpoints using self-signed SSL certificates. Enabling automated response systems is crucial to prevent delayed containment, as manual verification can slow down reaction times.
Keeping updated indicators of compromise, such as file hashes and associated hostnames, and enforcing strict outbound traffic controls are essential strategies to disrupt GhostSocks’ ability to maintain C2 communications.
The persistence of GhostSocks underscores the need for vigilant cybersecurity measures. As attackers continue to adapt and refine their techniques, organizations must remain proactive to mitigate the risks posed by advanced threats like GhostSocks.

.webp?ssl=1)