Iran’s Ministry of Intelligence and Security (MOIS) is orchestrating a sophisticated cyber campaign employing multiple hacker identities. This campaign, initially perceived as separate hacktivist activities, is now revealed to be a unified state-directed operation.
Unmasking the Hacker Identities
Among the hacker personas are Homeland Justice, Karma, and Handala. Initially, these groups were thought to function independently. However, thorough investigations have shown that they are all part of a coordinated effort led by the Iranian government. This operation integrates cyber intrusions, data theft, and psychological influence tactics targeting various international entities.
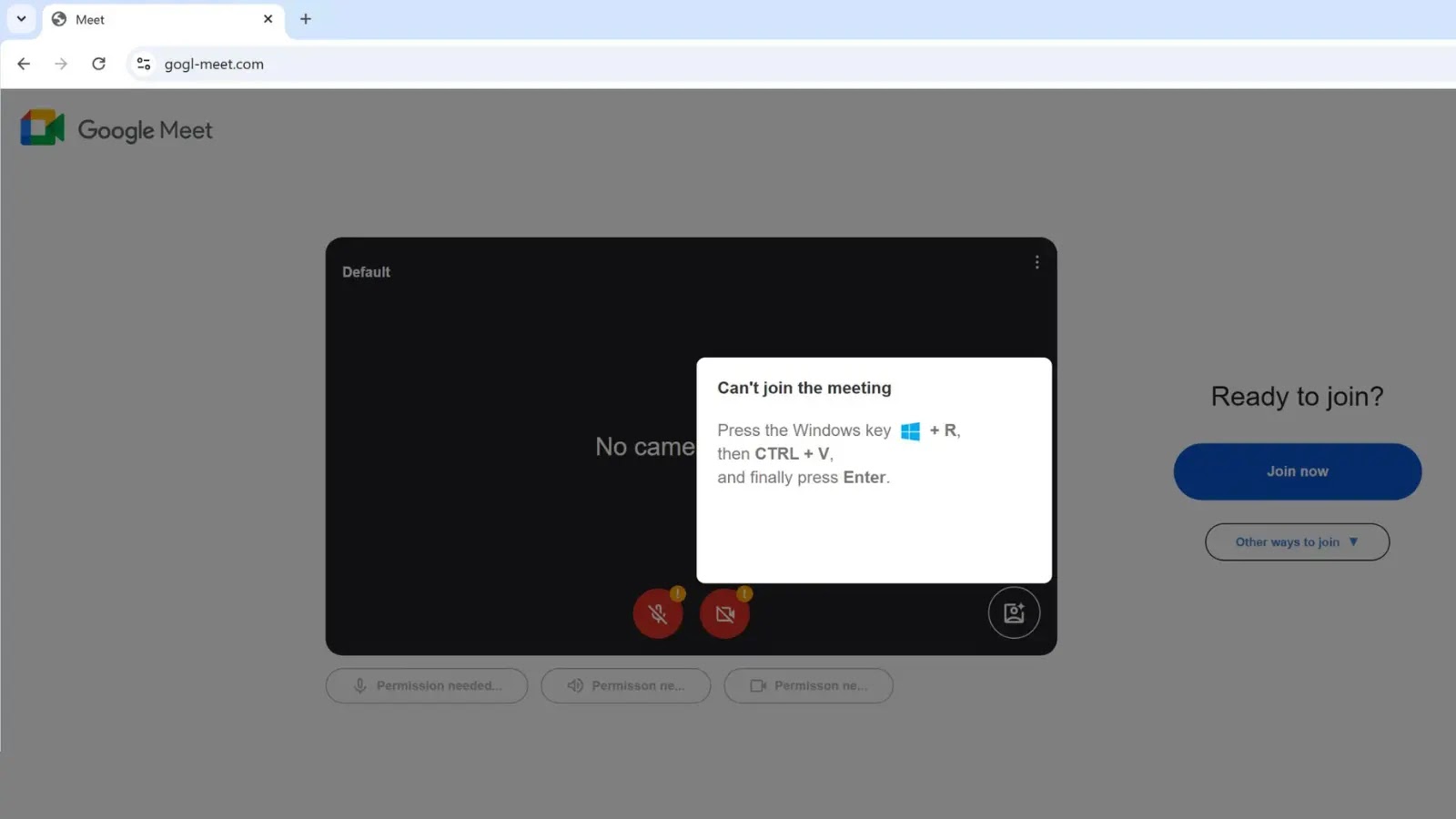
The campaign began to gain attention in 2022 when Homeland Justice launched attacks on the Albanian government. Iranian operatives had infiltrated Albania’s systems over a year before these attacks became public, using their access to exfiltrate sensitive information and conduct destructive activities.
Expansion and Rebranding of Cyber Operations
In 2023, the campaign expanded under new personas. The group rebranded from Homeland Justice to Karma, and later KarmaBelow80, shifting their focus to Israeli targets. Despite the change in identities, the tools and techniques remained consistent, indicating a singular control behind these operations.
DomainTools researchers identified a pattern in domain usage and command-and-control tactics, further linking these activities to a single entity. By 2024, the operation evolved once more, adopting the Handala identity to focus on information warfare and targeted harassment.
Impact and Measures Against the Campaign
The U.S. Justice Department took action in March 2026, confiscating domains linked to these operations. These domains were used to distribute stolen data and incite violence. Security experts have labeled this threat as Void Manticore, also known as MOIST GRASSHOPPER, underlining its connection to MOIS.
This campaign exemplifies the integration of cyber attacks with psychological operations to manipulate public perception. It shows a strategic use of diverse identities to mask the central control and achieve distinct objectives.
Experts recommend vigilance against suspicious activities, particularly in internet-facing services. Organizations are advised to enforce strong network security measures and monitor for signs of manual intrusion.
For ongoing updates and insights into cyber threats, follow us on Google News, LinkedIn, and X. Stay informed and protect your digital assets against evolving cyber threats.

.webp?ssl=1)