LeakNet, a notorious ransomware group, has significantly evolved its attack methods. Previously targeting around three victims monthly, they are now expanding rapidly with tools that evade typical security measures.
Innovative Approaches: ClickFix Strategy
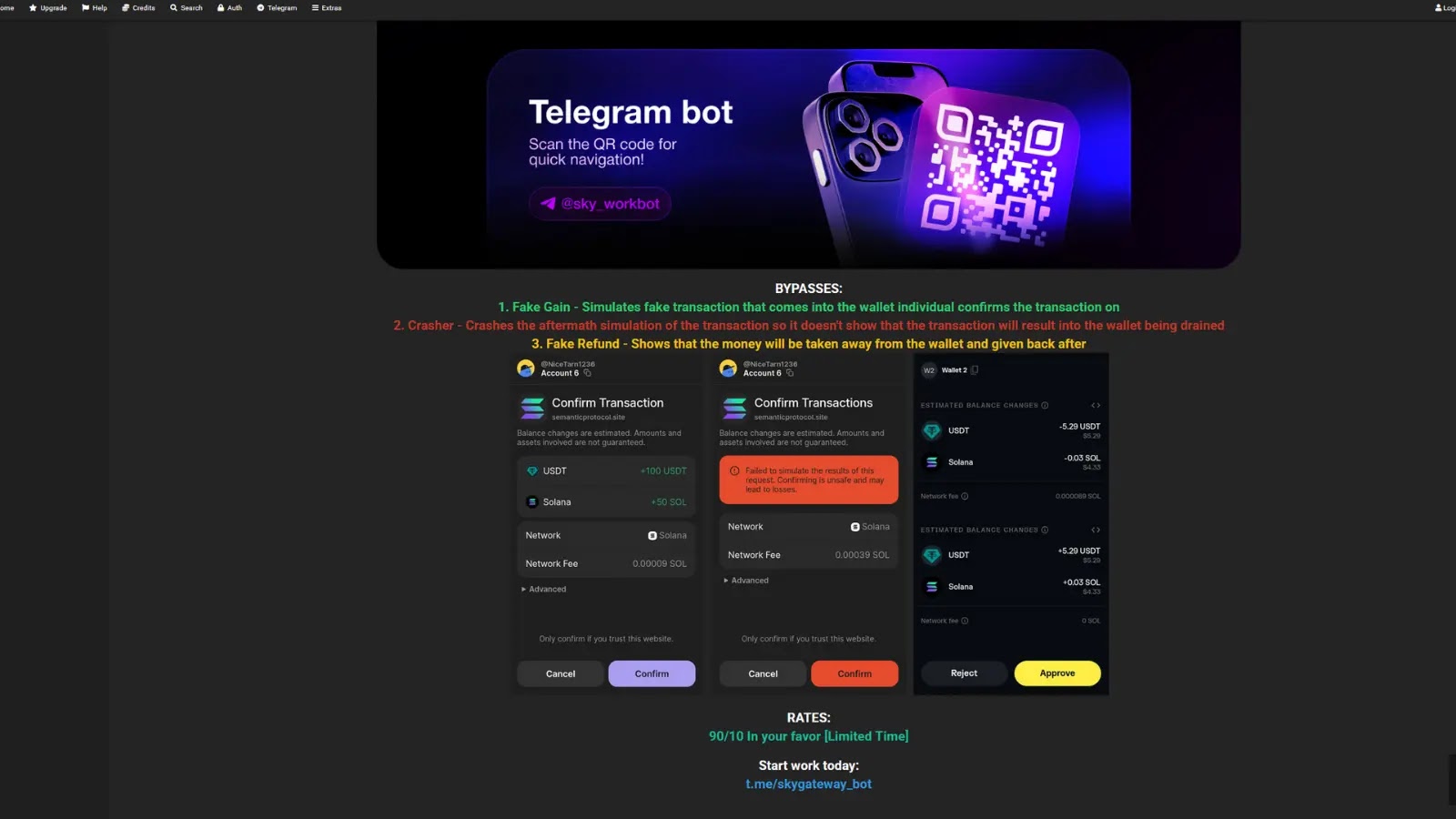
LeakNet has adopted ClickFix, a social engineering tactic, indicating a shift in their victim acquisition process. Unlike their previous reliance on initial access brokers (IABs) for stolen credentials, they now embed fake verification pages on legitimate websites.
These pages mimic common security checks, such as Cloudflare’s, tricking users into executing harmful commands. This tactic doesn’t target specific victims but instead casts a wide net, increasing the likelihood of successful attacks.
Analyzing LeakNet’s Tactical Shift
Security researchers from ReliaQuest have attributed several recent incidents to LeakNet. This shift away from IABs allows LeakNet to expand its victim pool and streamline operations, as evidenced by ClickFix’s role in distributing a majority of top malware families tracked in 2025.
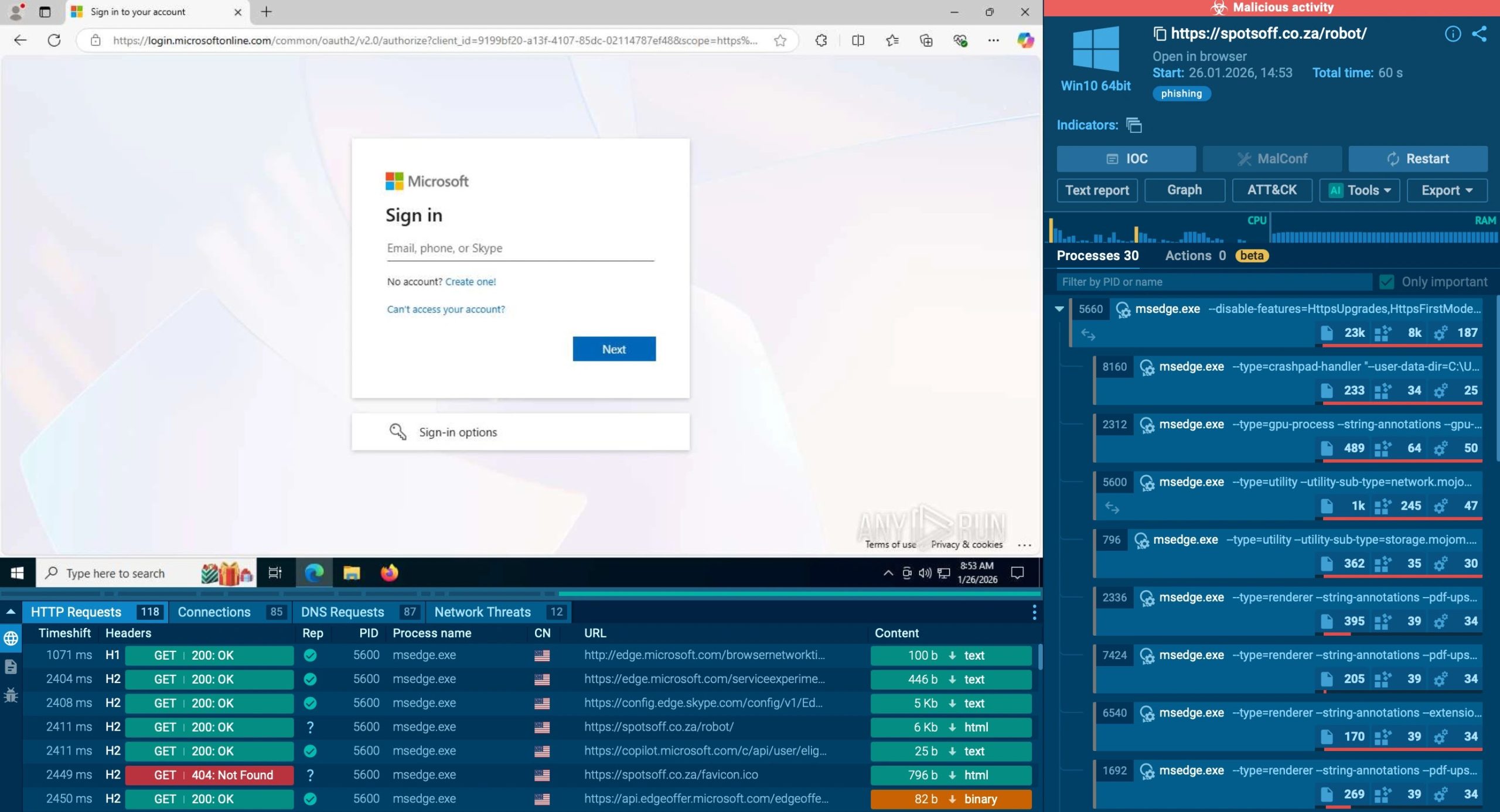
This change heightens risks for any employee browsing the web, as the lures are hosted on genuine websites, reducing the likelihood of detection by conventional network defenses. Behavioral monitoring becomes crucial, especially for spotting suspicious command executions.
The Deno Loader: A Stealthy Threat
LeakNet’s enhanced arsenal includes a stealthy loader leveraging the Deno JavaScript runtime. By using a bring-your-own-runtime (BYOR) strategy, they avoid deploying detectable malicious binaries, opting instead to use the legitimate Deno executable to execute malicious code.
The loader operates entirely in memory, initiated through PowerShell and Visual Basic scripts, making it difficult for traditional security tools to detect. This method ensures that no standard files are written to the system, maintaining a low profile.
Defensive Measures and Future Outlook
Organizations are advised to block newly registered domains and restrict standard users from executing certain commands. Security teams should monitor for unusual activities, such as PsExec usage and unexpected outbound connections, to preemptively isolate compromised systems.
Understanding LeakNet’s consistent attack patterns provides an opportunity for defenders to intercept and disrupt the attack chain before ransomware deployment. Staying informed on these evolving threats is key to maintaining robust cybersecurity defenses.