In a complicated provide chain phishing assault, risk actors hijacked an ongoing e-mail thread amongst C-suite executives discussing a doc awaiting remaining approval.
The intruder, posing as a official participant, replied instantly with a phishing hyperlink mimicking a Microsoft authentication kind. Researchers attribute this to a compromised gross sales supervisor account at an enterprise contractor, permitting seamless insertion right into a trusted enterprise dialog.
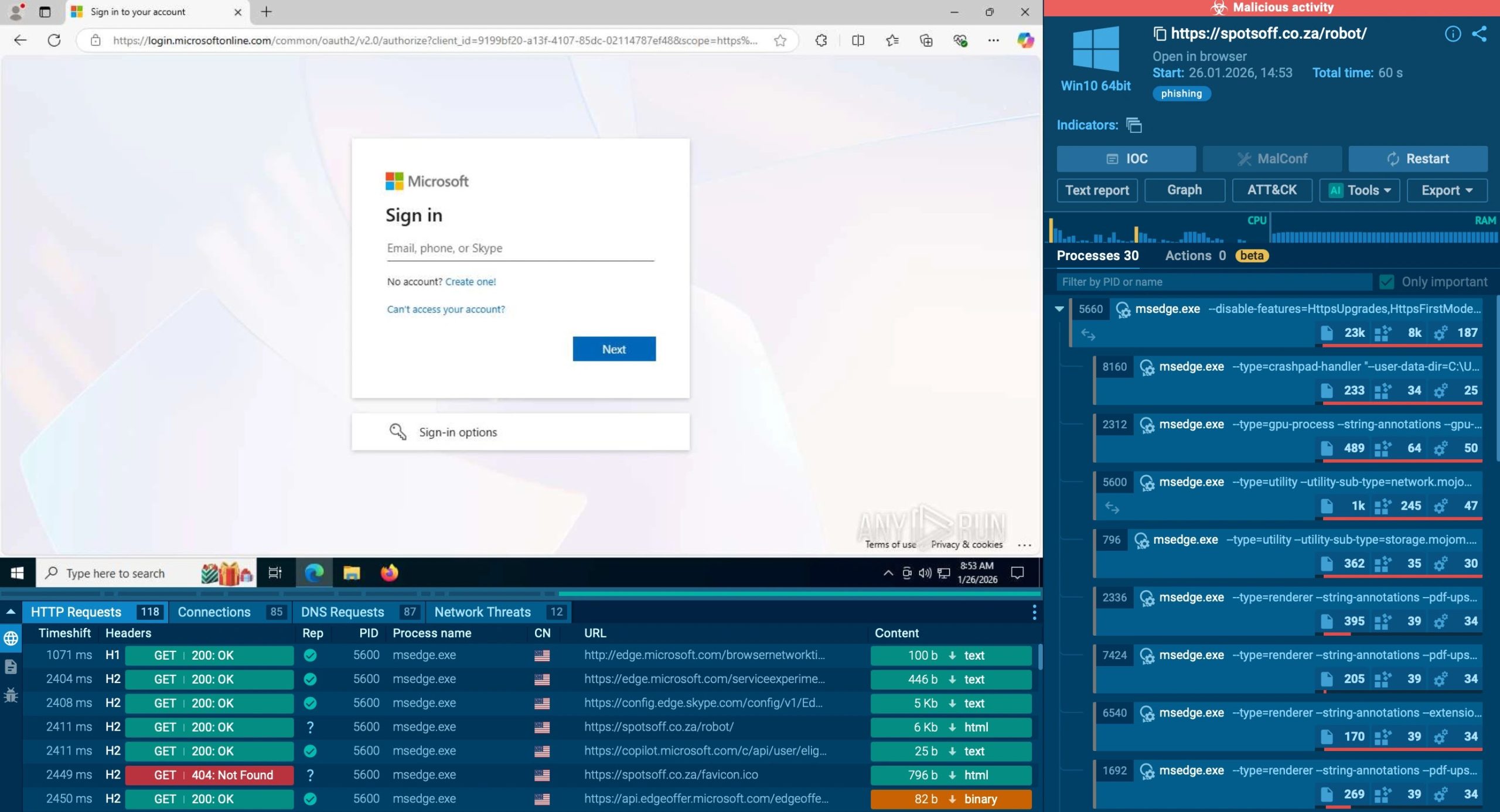
Assault Chain (Supply: ANY.RUN)
This incident underscores a rising tactic: adversaries exploiting actual enterprise communications fairly than crafting chilly phishing lures. By early January 2026, evaluation revealed ties to a broader marketing campaign energetic since December 2025, primarily concentrating on Center Jap corporations.
Examined samples within the ANYRUN Sandbox uncovered the EvilProxy phishkit, a proxy-aware phishing device that evades conventional session-based detection, whereas TI lookups confirmed overlapping infrastructure.
Equip your SOC with early phishing detection, Convey MTTD to fifteen seconds with ANY.RUN Combine now
Assault Mechanics and Execution Chain
The assault unfolds by way of layered social engineering. It begins with a provide chain assault (SCA) phishing e-mail despatched to the contractor. This triggers seven forwarded messages, constructing plausibility because the payload ripples by way of inside channels.
E-mail Thread (Supply: ANY.RUN)
The ultimate reply embeds a phishing hyperlink resulting in:
An antibot touchdown web page protected by Cloudflare Turnstile CAPTCHA.
A phishing web page with one other Turnstile layer for human verification.
EvilProxy deployment, capturing credentials by way of man-in-the-middle proxying.
Faux Cloudflare Verification (Supply: ANY.RUN)
This chain mimics official Microsoft 365 flows, utilizing dynamic HTML/PDF attachments with embedded scripts. No zero-days or exploits have been wanted; success hinged on enterprise belief and dialog hijacking. Infrastructure rivals phishing-as-a-service (PhaaS) platforms in scale, with rented domains and bot mitigation to filter analysts.
ANYRUN Sandbox detonation visualized the complete chain: community callbacks to C2 servers, credential exfiltration, and session token theft—all in underneath 60 seconds.
Detected in Sandbox (Supply: ANY.RUN)
Indicators pivoted to dozens of victims, with a Center East focus probably tied to regional finance and power sectors. EvilProxy’s resurgence, publish its 2023 debut, highlights PhaaS evolution: modular kits now combine Turnstile and geo-fencing, complicating takedowns.
Not like technical vulnerabilities, these assaults weaponize human workflows. Compromised contractor accounts grant “perfect-looking” emails, bypassing DMARC and filters. Enterprises face elevated threat as distant work normalizes async approvals.
Risk Lookup (Supply: ANY.RUN)
Mitigation Methods and IOCs
Defend with course of hardening:
Flag HTML/PDFs with dynamic content material; sandbox suspicious recordsdata pre-interaction.
Implement four-eyes precept: separate initiation from approval.
Practice by way of life like SCA simulations mimicking hijacked threads.
ANYRUN equips SOCs with behavioral stories, slashing MTTD/MTTR.
Key IOCs:
CategoryIndicatorsURI PatternPOST ^(/bot/Domainshimsanam[.]combctcontractors[.]comstudiofitout[.]rost-fest[.]orgkomarautikat[.]hueks-esch[.]deavtoritet-car[.]comkaraiskou[.]edu[.]grDomain Sample^loginmicrosoft*
Give your staff sooner risk validation
Detect hidden phishing flows instantlly Contact ANY.RUN staff