LucidRook Malware Targets Taiwan
A newly detected cyber threat known as LucidRook has been discovered targeting institutions in Taiwan. The malware disguises itself as genuine security software, deceiving users into executing it. This malicious campaign is primarily aimed at non-governmental organizations and possibly universities within Taiwan.
Deceptive Tactics and Distribution
The attackers have carefully crafted the malware to appear as a legitimate cybersecurity product by imitating its icon and application name. The campaign employs spearphishing emails containing shortened URLs, leading to password-protected compressed files. These files include decoy documents, such as a government-issued letter intended for Taiwanese universities, to lend authenticity to the attack.
Cisco Talos researchers identified this activity, linking it to a threat group known as UT. The group has been observed conducting spearphishing campaigns against Taiwanese entities to deploy LucidRook, distinguished by its Lua-based architecture and sophisticated design.
Technical Aspects and Intrusion Methods
LucidRook operates as a stager, embedding a Lua interpreter with Rust-compiled libraries within a Windows DLL. This campaign’s distinctiveness lies in its deception and technical complexity. Accompanying LucidRook, a reconnaissance tool called LucidNight was also found, indicating a tiered toolkit approach, possibly used to assess targets before deploying the full malware suite.
The infection process initiates with a spearphishing email prompting the download of an archive. The malware, disguised as a Trend Micro product, uses a fake icon and application name. It also drops decoy documents to distract victims while the malware executes silently.
Persistence and Data Exfiltration
Upon infiltration, the malware exploits legitimate Windows binaries, utilizing DLL search order hijacking. It places a stager file in a hidden directory, operating seamlessly with legitimate executables. To maintain persistence, the malware uses an LNK file in the Windows Startup folder, masquerading as Microsoft Edge.
LucidRook collects extensive system data, including usernames, computer details, and running processes, storing this information in encrypted files. These files are then uploaded to compromised FTP servers operated by Taiwanese companies, retrieving additional payloads securely.
To evade detection, LucidRook employs advanced obfuscation techniques, including a non-standard safe mode that restricts dynamic library loading and a complex string concealment method.
Defensive Measures and Recommendations
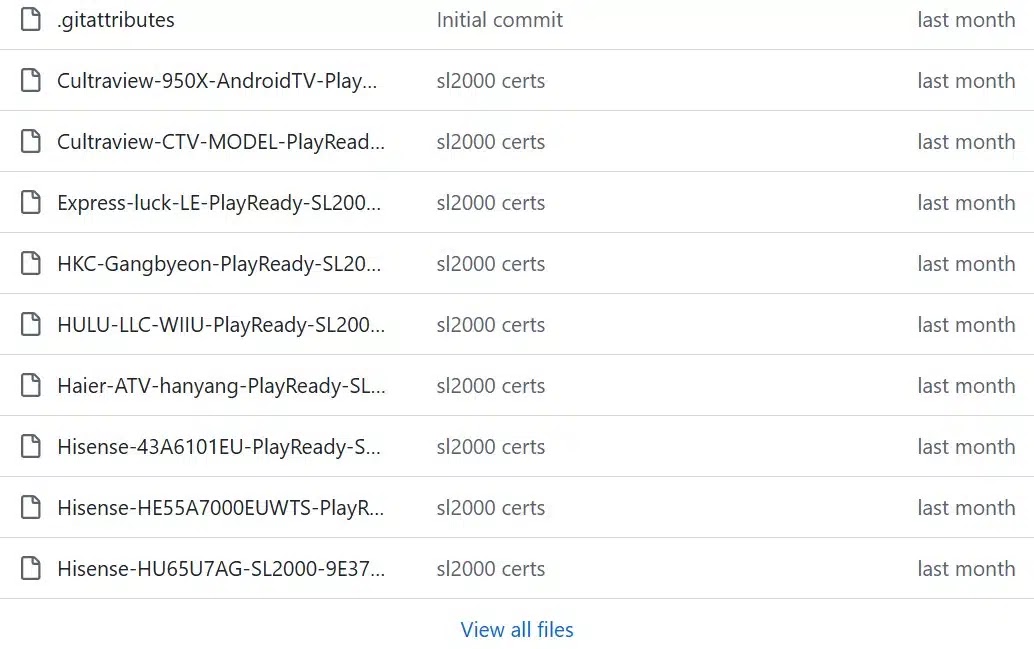
Cisco Talos has provided indicators of compromise on GitHub to assist in identifying this threat. Organizations are advised to enhance email filtering to detect spearphishing attempts, monitor for unusual DLL loading activities, secure FTP credentials, and utilize Snort detection rules released by Cisco Talos for effective protection against LucidRook and related threats.
Stay updated by following us on Google News, LinkedIn, and X. Make CSN your preferred source for instant updates.