A significant security vulnerability affecting MongoDB has been identified, posing a serious risk to servers worldwide. Known as CVE-2026-25611, this flaw carries a CVSS score of 7.5 and enables attackers to crash servers without authentication, using minimal network resources.
Understanding the Vulnerability
This vulnerability is present in all versions of MongoDB that have compression enabled, starting from version 3.4, with the feature being on by default from version 3.6 onwards. The issue affects both on-premise deployments and MongoDB Atlas, the cloud database service. Recent data from Shodan reveals that over 207,000 MongoDB instances are publicly accessible and vulnerable to exploitation.
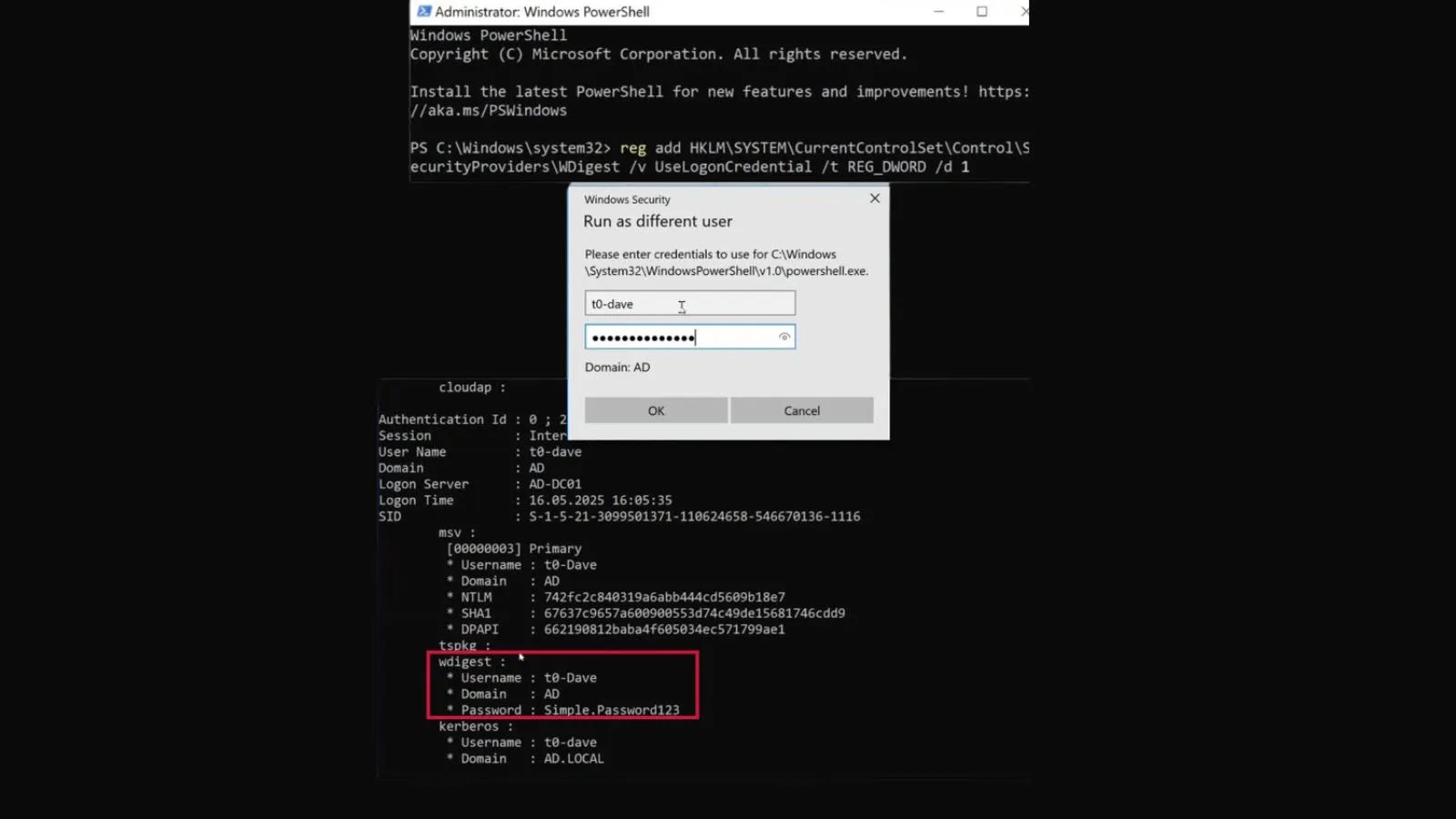
Mechanism of the Attack
The core of the vulnerability lies in the OP_COMPRESSED component of MongoDB’s wire protocol. When a server receives a compressed message, it allocates memory based on an unverified ‘uncompressedSize’ value. Attackers can exploit this by sending a small 47KB compressed packet that claims an uncompressed size of 48MB, leading to a memory amplification ratio of 1,027:1.
As SentinelOne reports, this amplification means that by opening numerous connections, an attacker can rapidly deplete a server’s resources. For instance, a server with 512MB of RAM could be overwhelmed in just two seconds with 10 concurrent connections.
Mitigation and Defensive Measures
To mitigate this threat, it is crucial for administrators to update their MongoDB installations to the latest patched versions: 8.2.4, 8.0.18, or 7.0.29. If immediate updating is not feasible, disabling compression through the –networkMessageCompressors=disabled flag is advised.
Moreover, enhancing network defenses by restricting database access to trusted networks and setting connection limits can help reduce risks. It is also recommended to avoid exposing MongoDB Atlas clusters to the public internet.
Organizations should monitor their systems for unusual spikes in memory usage and high volumes of connections to port 27017, which may indicate an ongoing attack. By staying vigilant and implementing these security measures, businesses can safeguard their data and infrastructure from potential exploits.
For ongoing cybersecurity updates and insights, follow our channels on Google News, LinkedIn, and X.