The RedAlert espionage campaign represents a sophisticated threat exploiting civilian vulnerabilities during the Israel-Iran conflict. By crafting a compromised version of the ‘Red Alert’ emergency app, attackers have turned a vital defense tool into a surveillance instrument.
Exploiting Fear Amidst Conflict
In the midst of ongoing tensions, cybercriminals have engineered a malicious app named RedAlert.apk, masquerading as the official emergency alert application. Distributed through SMS phishing, this counterfeit app bypasses the Google Play Store, compelling users to sideload it under the guise of a necessary update.
This campaign strategically capitalized on wartime anxiety, making it difficult for individuals to discern the legitimacy of the app. Once installed, the app mimicked the authentic interface, ensuring users remained oblivious to its true nature.
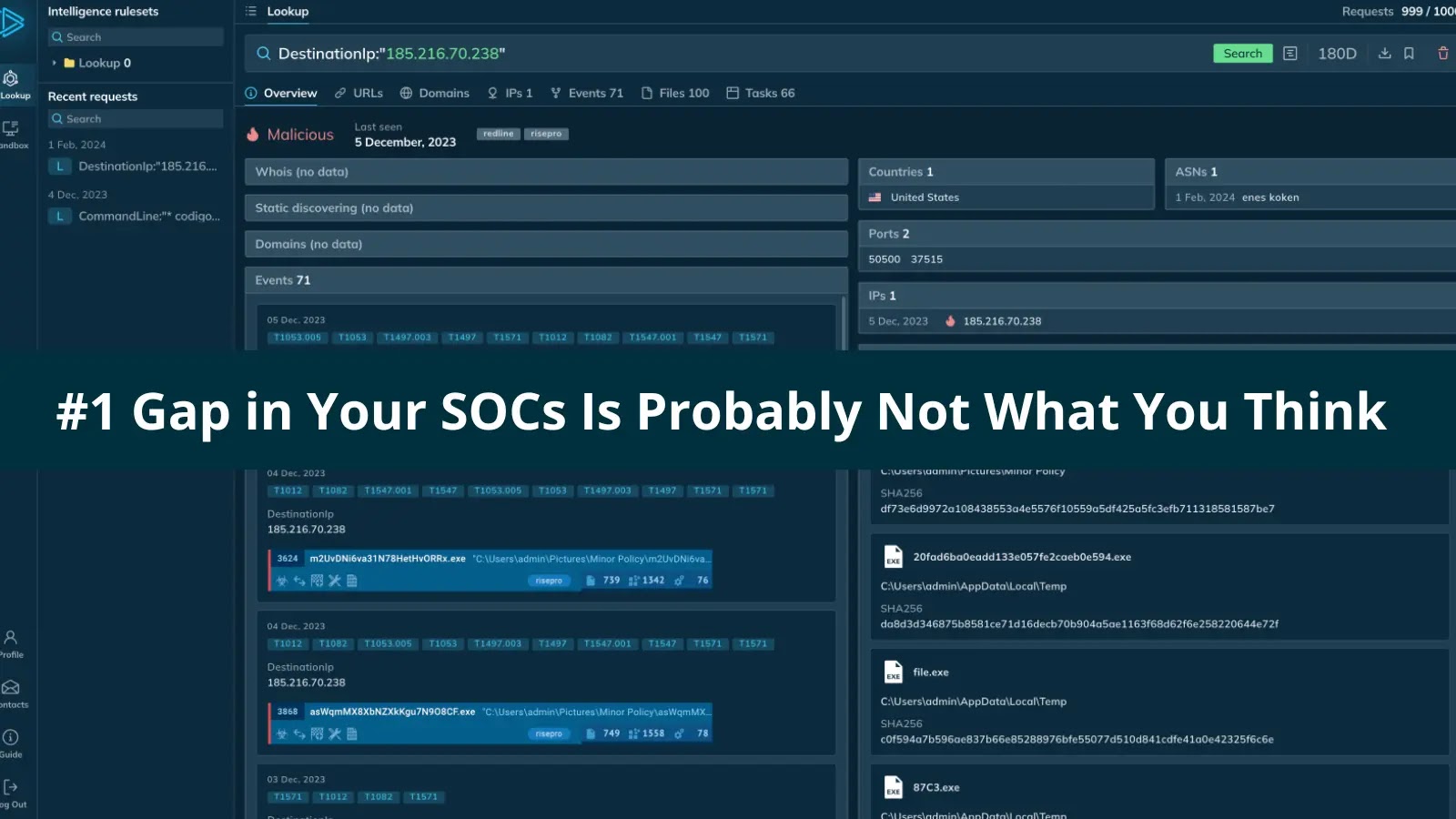
Technical Details and Data Harvesting
CloudSEK analysts discovered the layers of this campaign through detailed reverse engineering. The malware cleverly masked its operations, demanding high-risk permissions under the pretense of emergency functionality, and promptly activating data collection modules post-approval.
The extracted data, including GPS locations and SMS content, was relayed to attacker-controlled servers, offering insights into civilian movements and potential military activities. This data served more than just espionage; it facilitated bypasses of two-factor authentication and orchestrated misinformation campaigns.
Complex Infection Mechanism
The RedAlert.apk utilized a three-stage infection process, designed to evade detection. Initially, it employed a technique called Package Manager Hooking to disguise its true signature. A hidden file within the app was then executed in memory, circumventing static security checks.
The final stage unleashed a full spyware suite, establishing communication with the attackers’ command-and-control servers. This elaborate design underscores the campaign’s intent to maintain stealth and maximize data extraction.
To mitigate risks, users are advised to delete the fake app and reset their devices, while cybersecurity teams should block traffic to the attackers’ servers and enforce strict mobile device management policies.
Stay updated on developments by following us on Google News, LinkedIn, and X. Set CSN as your preferred news source for timely updates.