A classy new phishing assault approach referred to as “ConsentFix” that mixes OAuth consent phishing with ClickFix-style prompts to compromise Microsoft accounts with out requiring passwords or multi-factor authentication.
The assault leverages the Azure CLI app to realize unauthorized entry to sufferer accounts.
The ConsentFix assault operates solely inside the browser context, making it troublesome for conventional safety instruments to detect.
If a private e mail deal with is used, a enterprise deal with is prompted
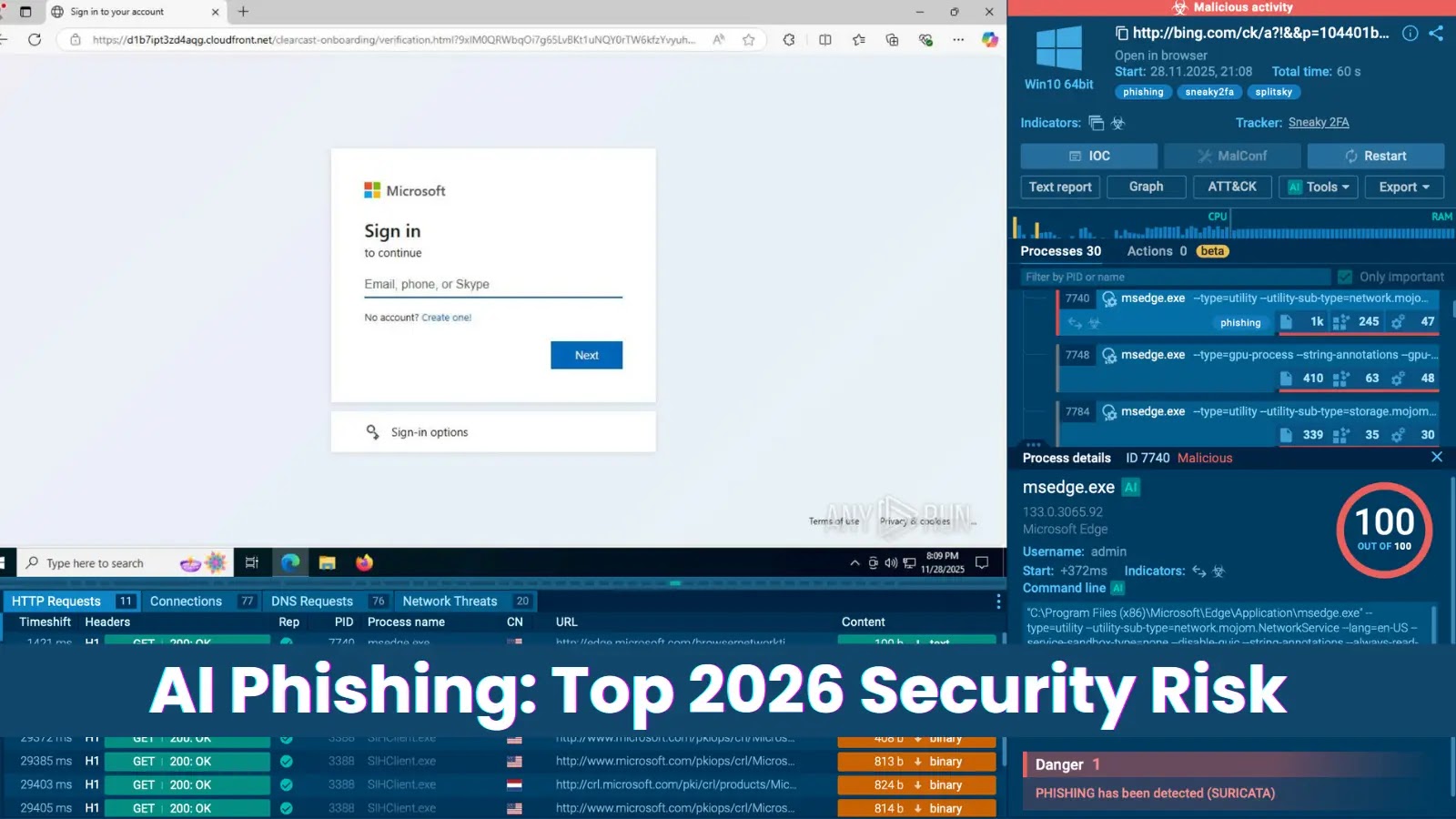
Victims are directed to malicious or compromised web sites by Google Search outcomes.
These websites comprise a pretend Cloudflare Turnstile verification that collects e mail addresses and filters for focused organizations.
As soon as a qualifying e mail is entered, victims are prompted to click on a “Signal In” button that opens a professional Microsoft login web page in a brand new tab.
If customers are already logged into their Microsoft account, they choose their account from a dropdown menu.
The browser then redirects to a localhost URL containing an OAuth authorization code related to the sufferer’s Microsoft account.
The sufferer is instructed to repeat this localhost URL and paste it again into the phishing web page.
enable entry by URL
This straightforward copy-paste motion grants the attacker full entry to the sufferer’s Microsoft account through Azure CLI.
Successfully circumventing all password-based safety measures and phishing-resistant authentication like passkeys.
Why Azure CLI Is Susceptible
Azure CLI is a first-party Microsoft utility implicitly trusted in Entra ID and exempt from commonplace OAuth consent necessities.
In contrast to third-party purposes, Azure CLI can request permissions with out administrative approval and can’t be blocked or deleted.
This makes it a super goal for exploitation. The marketing campaign employs subtle detection evasion strategies, together with conditional email-based focusing on.
displaying the response URL and redirect
Synchronized IP blocking throughout a number of compromised websites and selective JavaScript loading based mostly on customer IP addresses.
These methods stop safety evaluation, making the assault practically unattainable to determine solely by URL-based checks.
professional Microsoft web page and is redirected to a localhost URL containing a code related to their Microsoft account
PushSecurity urges organizations to observe Microsoft Azure CLI login occasions, which ought to sometimes be restricted to system directors and builders. Any uncommon interactive Azure CLI logins needs to be investigated.
Safety groups must also allow and monitor AADGraphActivityLogs to detect suspicious Azure AD enumeration exercise and look ahead to non-interactive logins from surprising geographic places.
Observe us on Google Information, LinkedIn, and X for every day cybersecurity updates. Contact us to characteristic your tales.