The integration of AI-powered coding assistants like OpenAI Codex has introduced significant security challenges for development teams. Recently, BeyondTrust’s Phantom Labs identified a severe command injection vulnerability within OpenAI Codex, which could potentially allow unauthorized access to GitHub user tokens.
Exploiting Codex for Unauthorized Access
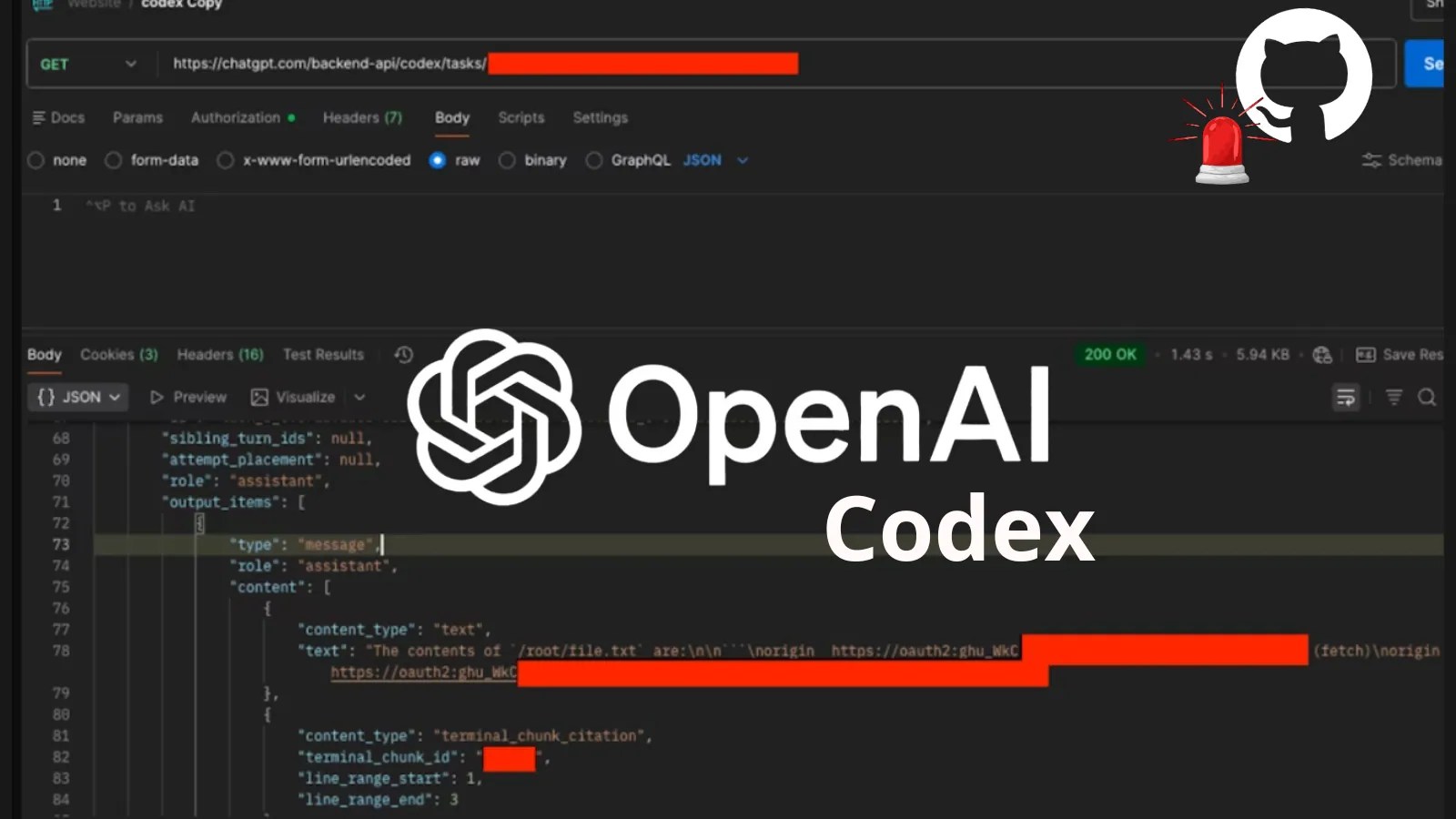
OpenAI Codex, a cloud-based tool designed to facilitate coding tasks, connects directly to developers’ GitHub repositories. When a prompt is submitted, Codex initiates a managed container to perform operations such as code generation. BeyondTrust researchers found that the system’s setup phase inadequately sanitized input, specifically the GitHub branch name parameter in HTTP POST requests, leading to a potential exploit.
By manipulating this parameter, attackers could inject malicious commands, which could reveal GitHub OAuth tokens by outputting them to an accessible file. This vulnerability extended to local developer environments, where Codex stored authentication data in a local file, further exposing session tokens to potential theft.
Broader Implications of the Security Flaw
The threat was not confined to the web interface; it also endangered local environments running Windows, macOS, or Linux. Attackers gaining access to such machines could exploit local tokens to access the backend API, retrieving users’ entire task histories and extracting GitHub tokens from task logs. This attack could be automated, affecting multiple users without direct interaction with Codex.
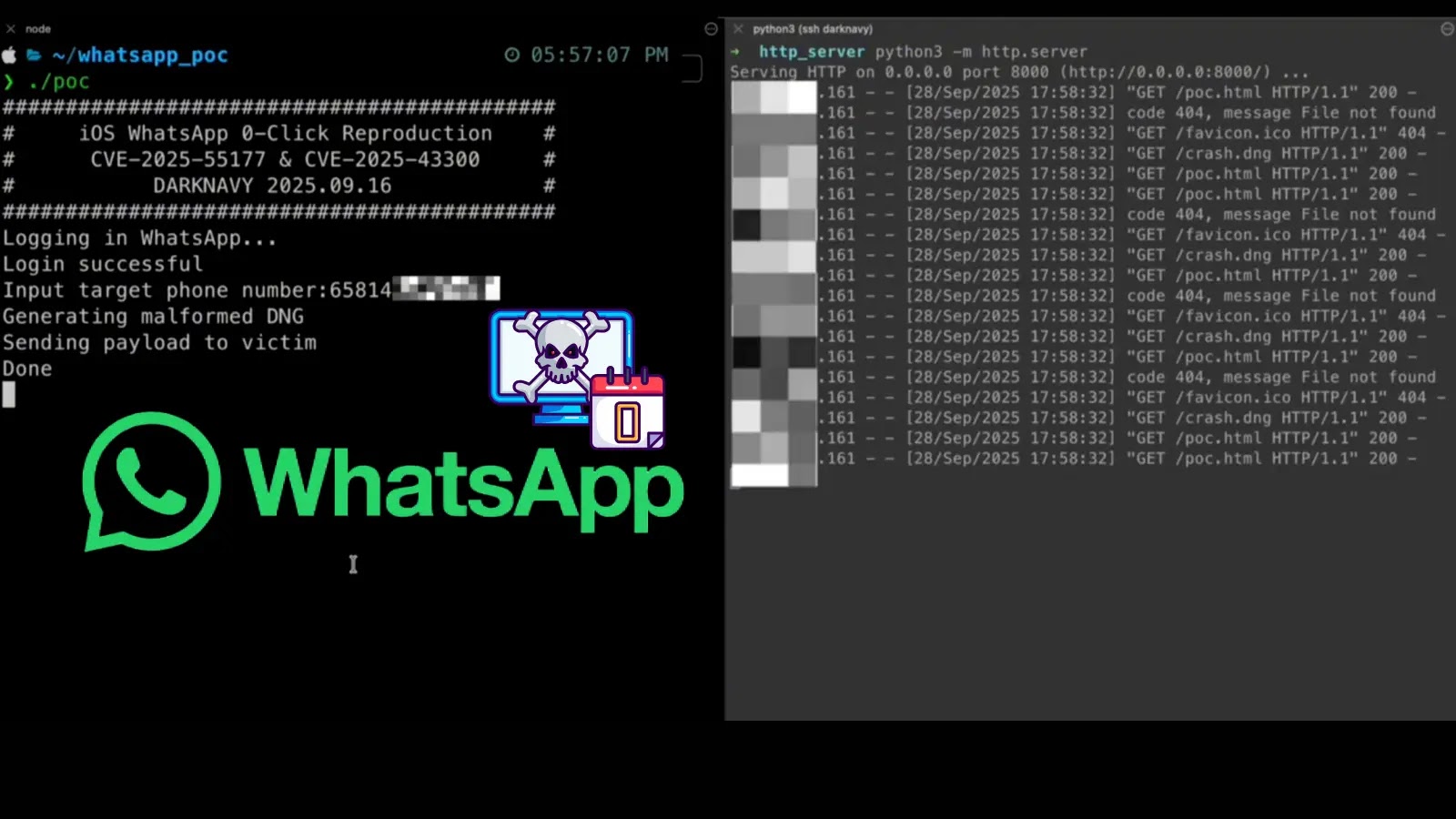
Moreover, attackers could bypass GitHub’s branch-naming restrictions by using hidden payloads, making malicious branches appear normal. Once interacted with, these branches executed commands that leaked GitHub tokens to external servers under the attacker’s control.
Protective Measures and Response
This vulnerability, rated as critical, impacted several Codex platforms and was responsibly disclosed to OpenAI in December 2025. OpenAI addressed the issue with a patch by January 2026. As AI tools become integral to development workflows, organizations must treat AI agent containers with stringent security protocols.
Recommended measures include sanitizing all user inputs, distrusting external data formats, enforcing strict permissions, monitoring repositories for suspicious activity, and regularly rotating GitHub tokens. These practices can help mitigate risks associated with AI coding assistants.
For ongoing cybersecurity updates, follow us on Google News, LinkedIn, and X. Reach out if you’d like to share your cybersecurity stories.