A recent phishing campaign has emerged, targeting software developers by exploiting GitHub Discussions. The attackers are disseminating counterfeit Visual Studio Code security notifications, deceiving users into downloading harmful software.
Deceptive Security Alerts
This malicious operation involves posting numerous fake security advisories on GitHub, masquerading as warnings about critical vulnerabilities in Visual Studio Code. Developers are urged to install a ‘patched’ version via an external link, which is, in reality, a conduit for malware.
The campaign is characterized by a flood of posts across GitHub repositories, each mimicking official security notices with titles like ‘Severe Vulnerability – Immediate Update Required’ and ‘Critical Exploit – Urgent Action Needed.’ These posts often include fabricated CVEs and fictitious version details to enhance their credibility.
Widespread Impact and Automation
GitHub Discussions automatically notify repository participants, extending the reach of these fake alerts beyond the platform. Security analysts from Socket.dev identified the campaign as a coordinated spam effort, with posts generated by new or inactive accounts, tagging numerous developers in unrelated repositories for maximum exposure.
The deceptive alerts include links leading to file-sharing services rather than legitimate distribution channels. This approach exploits GitHub’s collaborative environment to turn an everyday workspace into a malware delivery mechanism.
Advanced Phishing Techniques
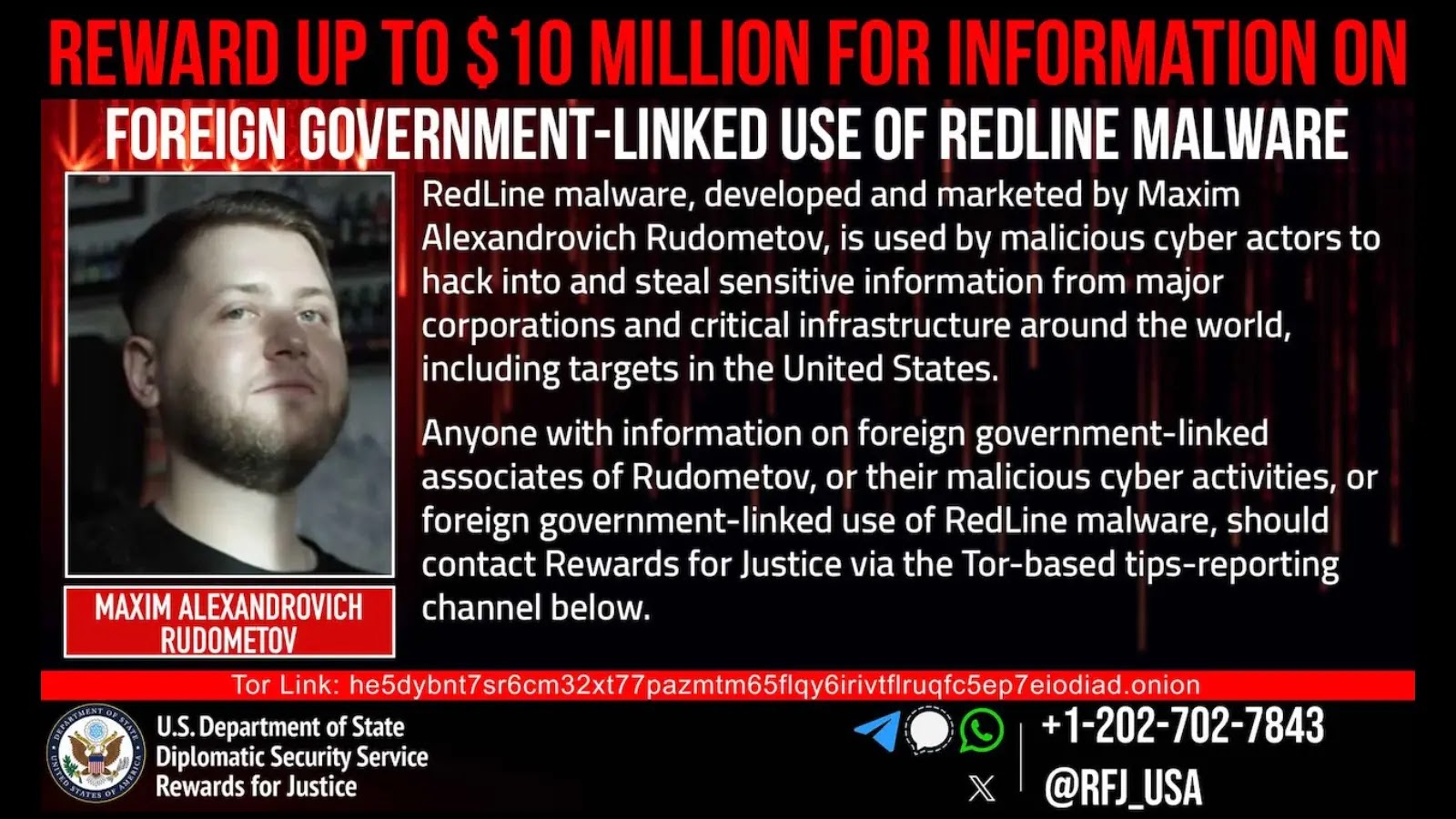
An investigation into the campaign revealed a sophisticated multi-step redirection chain designed to evade detection. Clicking the malicious link reroutes users through a Google share endpoint, then differentiates based on browser cookies, ultimately directing them to an attacker-controlled domain.
Once on this domain, an obfuscated JavaScript payload executes, collecting detailed browser fingerprint data to distinguish real users from bots. This information is silently submitted to the attackers, allowing them to tailor further attacks.
Recommendations for Developers
Developers are advised to remain vigilant against unsolicited security alerts in GitHub Discussions, particularly those containing external download links or unverifiable CVEs. Official Microsoft channels should be the sole source for VS Code updates, and suspicious discussions should be reported to GitHub.
Staying informed and cautious can help mitigate the risks posed by this and similar phishing campaigns. For more updates on cybersecurity, follow us on Google News, LinkedIn, and X.

.webp?ssl=1)