The cybersecurity panorama witnessed a dramatic shift in June 2025 because the Qilin ransomware group emerged because the dominant risk actor, orchestrating an unprecedented surge in high-value focused assaults throughout a number of sectors and geographical areas.
This escalation represents a basic transformation in ransomware operations, shifting past conventional monetary motivations to embody strategic and political goals that threaten world infrastructure stability.
Qilin’s meteoric rise to prominence adopted the shutdown of RansomHub’s operations, creating an influence vacuum that the group quickly exploited by refined recruitment methods and tactical improvements.
The ransomware-as-a-service (RaaS) ecosystem skilled vital disruption as Qilin absorbed large-scale subsidiary actions from defunct operations, dramatically increasing their operational capability and geographical attain.
This consolidation enabled the group to outperform all different ransomware organizations, affecting the very best variety of victims and establishing an unprecedented stage of market dominance.
The group’s assault methodology demonstrates a calculated shift towards high-impact targets, systematically compromising authorities businesses throughout america, Colombia, the United Arab Emirates, and France in fast succession.
ASEC analysts recognized this sample as indicative of coordinated campaigns designed to maximise social disruption and political strain.
The concentrating on of world model corporations, together with leisure venues and important infrastructure suppliers, represents a strategic evolution that mixes conventional extortion with status injury ways.
Superior Goal Choice and Assault Vectors
Qilin’s refined concentrating on methodology reveals a multi-layered strategy that prioritizes most affect potential over easy monetary achieve.
The group demonstrates specific experience in figuring out and exploiting vulnerabilities inside interconnected techniques, specializing in entities that function vital nodes in world provide chains.
Their assaults towards automotive producers, power corporations, and medical establishments mirror an understanding of cascading failure eventualities the place single-point compromises can set off widespread operational disruptions.
The technical sophistication of Qilin’s operations extends past standard ransomware deployment, incorporating superior reconnaissance methods and protracted entry mechanisms that allow extended community infiltration earlier than payload execution.
This strategy permits the group to ascertain a number of failsafe positions inside compromised networks, guaranteeing continued entry even after preliminary detection and remediation makes an attempt.
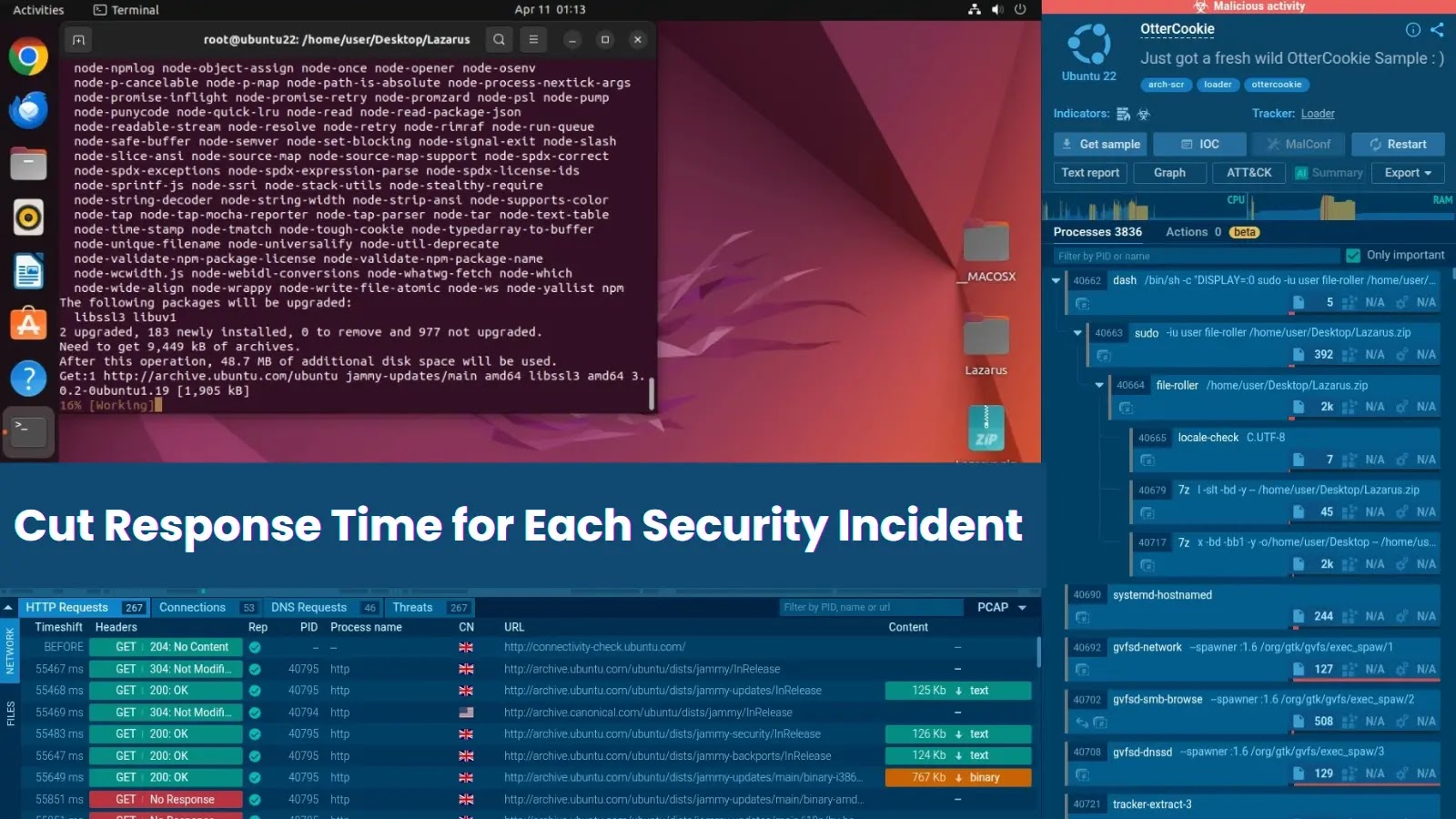
Examine stay malware habits, hint each step of an assault, and make sooner, smarter safety selections -> Attempt ANY.RUN now