The emergence of Pegasus and Predator spyware and adware over the previous a number of years has remodeled the panorama of cellular gadget safety.
These superior malware strains—deployed by refined risk actors for surveillance and espionage—have repeatedly demonstrated their capability to take advantage of zero-click vulnerabilities, leaving high-profile people and at-risk communities uncovered.
Essential forensic evaluation has lengthy relied on remnants inside iOS system logs, significantly the shutdown.log file, to discern traces of such infections even after the malware makes an attempt to erase itself.
With the discharge of iOS 26, forensic methodologies face an unprecedented setback. iVerify analysts recognized that Apple’s newest OS model now overwrites the shutdown.log file upon every gadget reboot, as an alternative of appending new log entries.
This seemingly innocuous change—whether or not intentional or inadvertent—has vital penalties for digital proof preservation.
Any gadget up to date to iOS 26 that’s subsequently restarted will see all prior shutdown.log content material erased, destroying potential indicators of compromise linked to Pegasus, Predator, or comparable threats.
Beforehand, refined spyware and adware like Pegasus would try and purge or tamper with shutdown.log as a part of its anti-forensics ways, a course of that also left behind refined indicators for vigilant analysts.
iVerify researchers have detailed that this “double erasure”—malware deletion adopted by OS-level overwriting—now absolutely sanitizes this essential artifact, hampering investigations and masking profitable compromises way more successfully than earlier ways.
An infection Mechanism and Proof Erasure in iOS 26
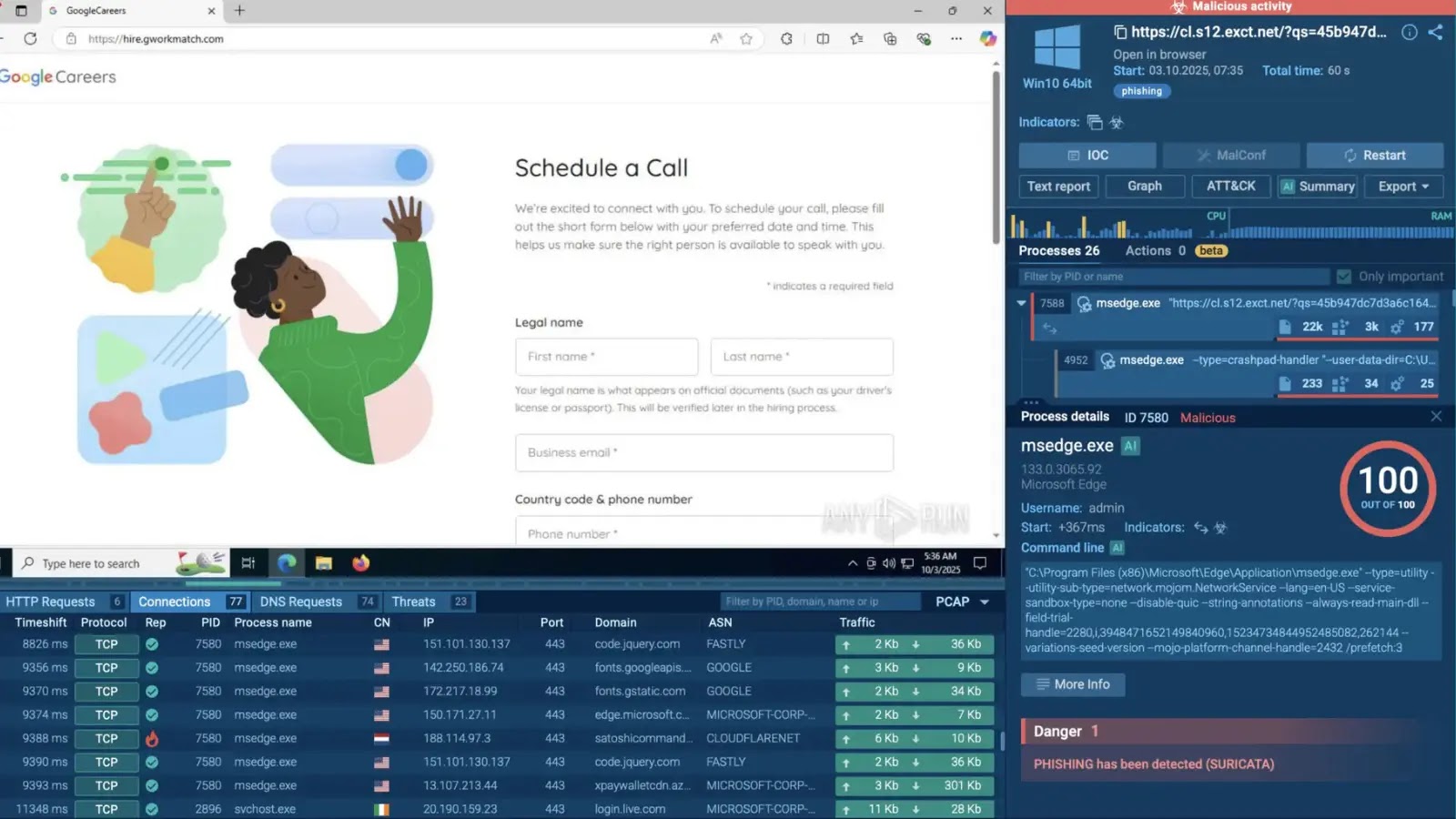
Inspection of historic shutdown.log entries revealed distinctive markers left by Pegasus in previous infections, akin to references to processes like com.apple.xpc.roleaccountd.stagingcom.apple.WebKit.Networking.
Since iOS 26, such forensic alerts should not merely buried—they’re irretrievably deleted on the following boot.
Boot and reboot occasions (Supply – iVerify)
The log’s prior construction, which appended every shutdown entry, supplied investigators a chronological view important for tracing an infection timelines.
The technical transition to full overwriting exhibits a before-and-after comparability of the shutdown.log habits after reboot.
This method-level change, reported by iVerify because the foremost group uncovering this growth, alters the stability between attackers and defenders, elevating pressing questions on digital proof, person safety, and malware accountability.
Comply with us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most well-liked Supply in Google.