A recent development in the cybersecurity landscape has seen a new variant of the VoidStealer infostealer bypass Google Chrome’s Application-Bound Encryption (ABE) without employing code injection or high-level system privileges. This marks a significant evolution in malware capabilities and has captured the attention of security experts worldwide.
Introduction of VoidStealer Variant
Introduced as part of VoidStealer version 2.0 on March 13, 2026, this new variant utilizes a debugger-based method to extract encrypted browser credentials directly from memory. This innovative approach represents a major shift in credential theft techniques, challenging existing security measures.
Google’s ABE, implemented with Chrome 127 in July 2024, was designed to significantly impede malware access to sensitive browser data, such as stored passwords and cookies. It achieves this by linking the encryption key, known as the v20_master_key, to a system-level service operating with high privileges on Windows systems.
Evolution and Detection Challenges
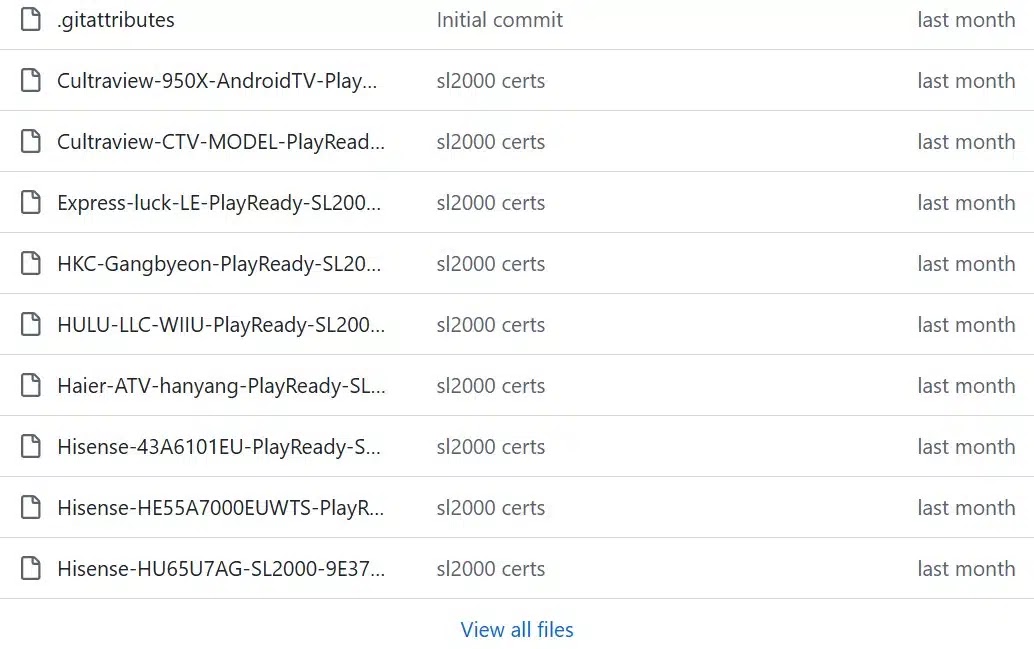
Despite the enhanced security provided by ABE, cybercriminals have continuously developed methods to circumvent it. GenDigital analysts have identified VoidStealer as a Malware-as-a-Service (MaaS) offering, which first emerged on dark web forums in December 2025, including HackForums.
VoidStealer’s rapid evolution is notable, with a swift progression from version 1.0 to 2.1 in a mere three months. The transition from traditional injection-based methods to a debugger-based approach, as seen in version 2.0, sets VoidStealer apart as the first in the wild to employ this technique.
Technical Details of the Bypass
The primary threat of this variant lies in its minimal detection footprint. Unlike other ABE bypass techniques that require elevated privileges or direct browser code injection, VoidStealer leverages standard Windows debugging APIs, which are less likely to trigger security alerts.
VoidStealer targets both Google Chrome and Microsoft Edge. The method, inspired by the open-source ElevationKatz project, involves using a debugger to set hardware breakpoints when the v20_master_key appears in memory as plaintext. This process is initiated by creating a suspended browser process and attaching a debugger, which then monitors for specific debug events.
Once key browser DLLs load, VoidStealer scans them to locate relevant sections where the encryption key becomes accessible. By setting hardware breakpoints across all threads, it extracts the key using minimal memory operations, thereby evading detection.
Implications and Defensive Measures
The availability of this technique through ElevationKatz suggests a potential increase in similar bypass attempts by other infostealers. As a countermeasure, security teams should consider any process that attaches a debugger to a browser as suspicious and monitor for unusual memory access patterns.
To enhance detection capabilities, organizations should flag processes that initiate browsers using hidden or headless modes, and alert on unexpected debugger attachments. The known indicator of compromise for VoidStealer v2.0 is identified as: f783fde5cf7930e4b3054393efadd3675b505cbef8e9d7ae58aa35b435adeea4.
For further updates, follow us on Google News, LinkedIn, and X, and set CSN as a preferred source on Google.