A vital distant code execution (RCE) vulnerability within the well-liked “Alone” WordPress theme is being actively exploited by attackers to realize full management of weak web sites.
The vulnerability, assigned CVE-2025-5394 with a most CVSS rating of 9.8, impacts over 9,000 websites utilizing variations 7.8.3 and under of the charity-focused theme.
Key Takeaways1. Important RCE flaw within the Alone WordPress theme permits full website takeover.2. 120,900+ energetic assaults deploying malicious backdoors since July twelfth.3. Replace instantly if utilizing older variations.
Technical Particulars of WordPress Plugin Vulnerability
The vulnerability stems from a lacking functionality test within the alone_import_pack_install_plugin() perform, which handles plugin installations throughout theme setup.
The flawed code permits unauthenticated attackers to take advantage of the wp_ajax_nopriv_alone_import_pack_install_plugin AJAX motion to add arbitrary information disguised as plugins from distant sources.
The weak perform processes POST information with out correct authentication:
This design flaw permits attackers to put in malicious plugins containing webshells and backdoors by sending crafted requests to /wp-admin/admin-ajax.php?motion=alone_import_pack_install_plugin.
The vulnerability permits each native plugin slugs and distant sources through the plugin_source parameter, making exploitation trivial for cybercriminals.
Threat FactorsDetailsAffected ProductsAlone – Charity Multipurpose Non-profit WordPress Theme ≤ 7.8.3ImpactRemote Code Execution (RCE), Full Website TakeoverExploit PrerequisitesUnauthenticated exploitation possibleCVSS 3.1 Score9.8 (Important)
Theme RCE Vulnerability Actively Exploitation
Exploitation started on July twelfth, 2025, two days earlier than the vulnerability’s public disclosure, indicating attackers monitor software program patches for newly fastened safety points.
Wordfence safety researchers have documented over 120,900 blocked exploit makes an attempt since monitoring started.
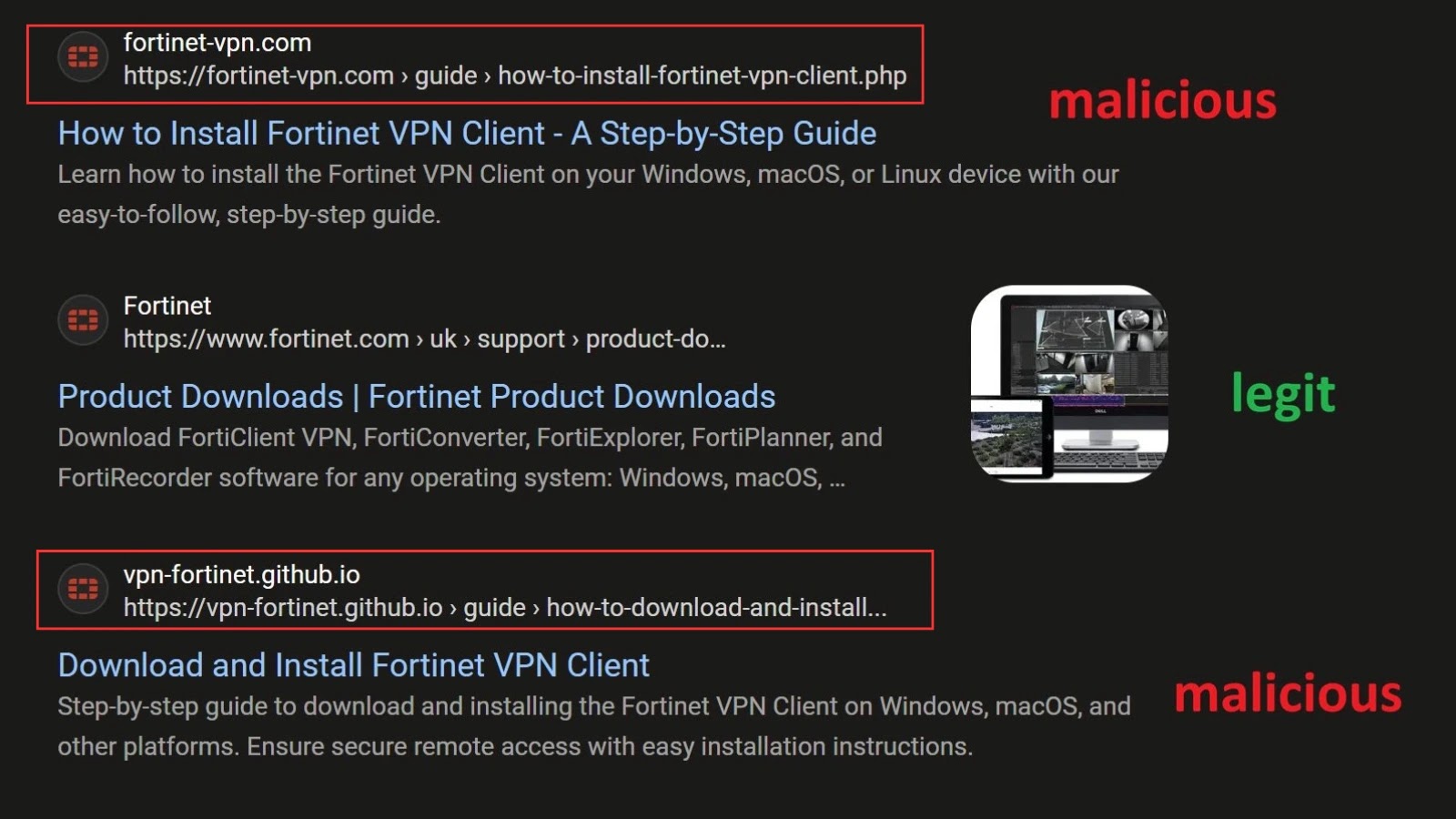
Attackers are deploying subtle malware via malicious zip information with names like wp-classic-editor.zip and background-image-cropper.zip. One captured backdoor pattern demonstrates typical obfuscation strategies:
Probably the most energetic attacking IP addresses embody 193.84.71.244 (39,900+ requests) and 87.120.92.24 (37,100+ requests). Malicious domains internet hosting exploit payloads embody cta.imasync[.]com and dari-slideshow[.]ru.
Web site directors should instantly replace to the Alone theme model 7.8.5 or later, which patches the vulnerability. Wordfence firewall customers obtained safety guidelines on Might thirtieth, 2025, with free tier customers shielded from June twenty ninth.
Safety groups ought to study /wp-content/plugins and /wp-content/improve directories for suspicious plugin installations and overview entry logs for requests matching the exploit sample.
Combine ANY.RUN TI Lookup together with your SIEM or SOAR To Analyses Superior Threats -> Attempt 50 Free Trial Searches