Over 600 Fortinet FortiGate firewall systems have been compromised in a campaign driven by artificial intelligence, targeting exposed ports and weak credentials, according to a report by AWS.
Details of the AI-Powered Attack
This wave of cyber attacks took place from January 11 to February 18, focusing on the exploitation of exposed configurations rather than known vulnerabilities. AWS identified the perpetrators as unsophisticated threat actors utilizing commercial AI services to execute known attack methods.
Attackers scanned for management interfaces via ports 443, 8443, 10443, and 4443, using common credentials to gain initial access. The approach was described as opportunistic, targeting appliances vulnerable to automated mass scanning rather than specific sectors.
Global Impact and Techniques Used
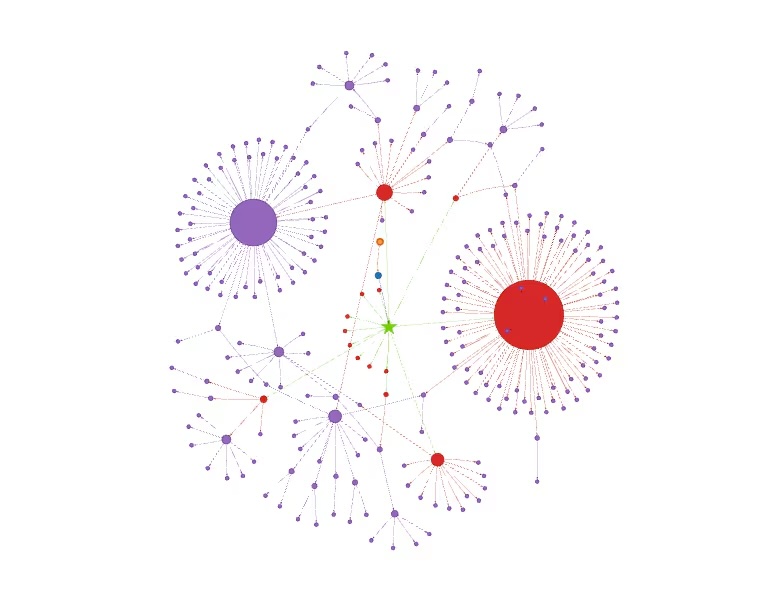
The breaches affected multiple FortiGate devices within the same organizations, with some IP clusters indicating involvement of managed service providers or large networks. AWS reported compromised devices across 55 countries, spanning Africa to Europe.
Post-compromise, attackers utilized open-source tools to extract NTLM password hashes, access entire domain credential databases, and perform lateral movements through pass-the-hash or pass-the-ticket attacks. They also targeted Veeam Backup & Replication servers to extract credentials and potentially destroy backups in preparation for ransomware attacks.
AI’s Role in Cyber Operations
At least two commercial large language models (LLMs) were employed by the hackers to plan, generate tools, and manage operations, including evaluating the duration and success of attacks. The plans were influenced by academic research on offensive AI agents, indicating the actor’s interest in state-of-the-art AI penetration testing techniques.
Scripts likely generated through AI were used on the threat actor’s infrastructure to parse configurations, extract credentials, automate VPN connections, and conduct mass scanning. AWS noted that the attack toolkit, which would usually suggest a large development team, was created by a single actor or a small group using AI assistance.
The attack is believed to have been carried out by a financially motivated, Russian-speaking actor with low-to-medium technical capabilities, as evidenced by the heavy reliance on AI across all phases of the operation.
Related topics: Mississippi Hospital System closes all clinics after a ransomware attack, FBI reports $20 million losses from ATM jackpotting attacks in 2025, and Fortinet addresses vulnerabilities in FortiCloud SSO authentication.