Behind the scenes of legislation enforcement in cyber: what will we find out about caught cybercriminals? What introduced them in, the place do they arrive from and what was their perform within the crimescape?
Introduction: One view on the scattered battle towards cybercrime
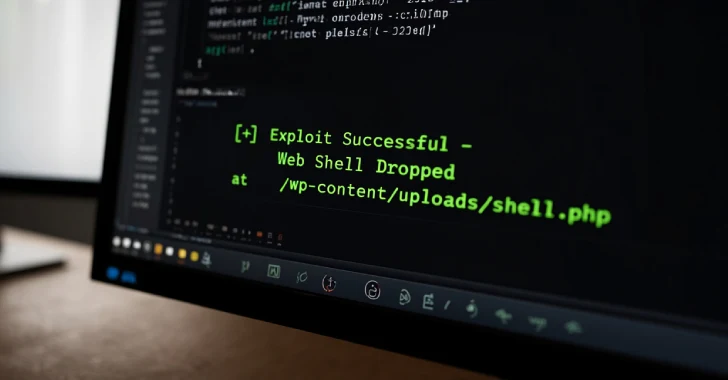
The rising sophistication and diversification of cybercrime have compelled legislation enforcement companies worldwide to reply by way of more and more