Since mid-2025, a cybercriminal group known as TA416 has intensified its efforts to target European government and diplomatic entities. This resurgence comes after a brief hiatus and is linked to various other threat groups including DarkPeony and RedDelta. The recent campaigns have focused on sophisticated malware delivery methods to infiltrate systems.
TA416’s Renewed Focus on Europe
Research indicates that TA416 has been orchestrating a series of cyber attacks across Europe, targeting entities aligned with the European Union and NATO. These attacks involve the deployment of the PlugX malware, leveraging advanced techniques such as OAuth redirects and Cloudflare Turnstile abuses, to bypass security measures.
The group’s activities are not limited to Europe. Following geopolitical tensions in the Middle East, particularly the U.S.-Israel-Iran conflict, TA416 has expanded its operations to gather intelligence in that region as well. This shift underscores their strategic interest in areas of global conflict.
Technical Overlaps and Tactics
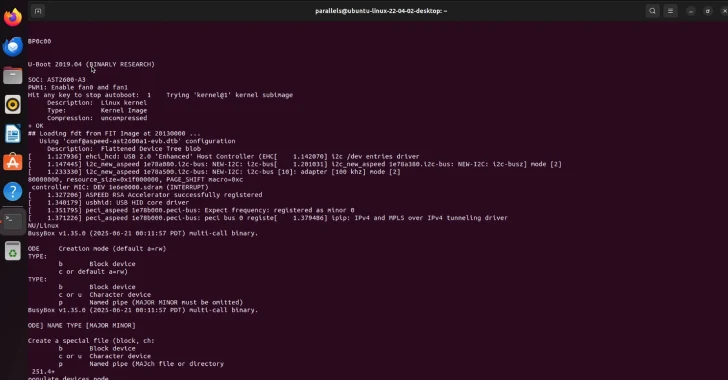
TA416 shares technical methodologies with another notorious group, Mustang Panda. Both utilize DLL side-loading to execute malware, although they employ different tools. TA416’s operations have been characterized by the consistent use of the PlugX backdoor, which facilitates encrypted communications with its command server after evading detection through anti-analysis measures.
Their attack methods have evolved, incorporating OAuth-based phishing techniques and leveraging platforms like Microsoft Azure and Google Drive to distribute malicious payloads. This adaptability highlights their persistent threat to global cybersecurity.
Implications and Future Outlook
The reemergence of TA416 in European cyber activity reflects a broader pattern of China-linked cyber operations focusing on long-term infiltration and data collection. According to recent analyses, these operations have shifted from broad strategic goals to more targeted, identity-centric objectives.
As organizations worldwide continue to report incidents involving TA416, the need for heightened cybersecurity measures becomes increasingly apparent. This includes addressing vulnerabilities in internet-facing infrastructures and enhancing detection mechanisms to counteract evolving threats.
Looking forward, the persistent threat posed by TA416 and similar groups suggests that geopolitical developments will continue to influence cyber attack strategies, necessitating ongoing vigilance and collaboration among international cybersecurity bodies.