The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently updated its Known Exploited Vulnerabilities (KEV) catalog, adding four significant vulnerabilities. These flaws are found in SimpleHelp, Samsung MagicINFO 9 Server, and D-Link DIR-823X series routers, all of which are currently subject to active exploitation. In light of this, federal agencies are required to address these vulnerabilities by May 8, 2026.
Details of the Newly Added Vulnerabilities
The vulnerabilities identified include CVE-2024-57726, a critical flaw in SimpleHelp with a CVSS score of 9.9. This missing authorization issue enables technicians with limited privileges to generate API keys with excessive permissions, potentially allowing them to elevate their access to server admin roles.
Another vulnerability, CVE-2024-57728, affects SimpleHelp as well. With a CVSS score of 7.2, it involves a path traversal issue where admin users can upload files arbitrarily across the system by using a specially crafted zip file, leading to arbitrary code execution.
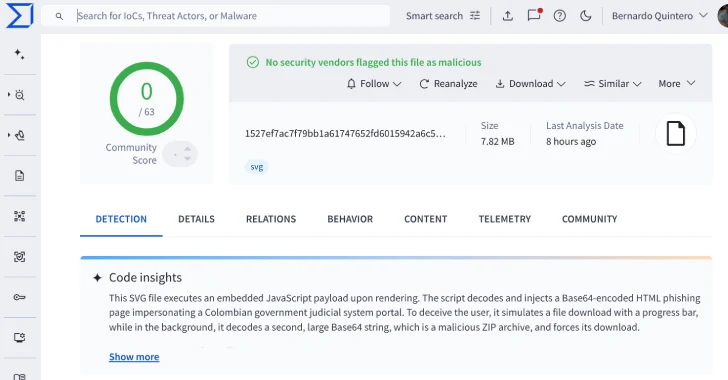
CVE-2024-7399, impacting Samsung MagicINFO 9 Server, is a path traversal vulnerability that allows attackers to write files with system authority. Additionally, CVE-2025-29635 in D-Link DIR-823X routers is a command injection flaw that permits authorized users to execute unauthorized commands remotely.
Potential Impacts and Ongoing Exploits
The SimpleHelp vulnerabilities have been flagged as potential precursors to ransomware attacks, although their specific use in such campaigns remains unclear. However, reports from cybersecurity firms such as Field Effect and Sophos indicate their exploitation in ransomware operations, notably by the group known as DragonForce.
The Samsung MagicINFO vulnerability has been associated with the deployment of the Mirai botnet, a notorious malware strain. Akamai has reported attempts to exploit the D-Link vulnerability to distribute a Mirai variant named ‘tuxnokill’.
Mandatory Actions for Federal Agencies
To mitigate these risks, the Federal Civilian Executive Branch (FCEB) agencies must promptly apply security patches. In the case of the D-Link vulnerability, they should cease using the affected routers entirely by the specified deadline in May 2026.
CISA’s directive underscores the critical importance of proactive cybersecurity measures to safeguard against increasingly sophisticated threats. As cyber adversaries continue to exploit known weaknesses, staying ahead with timely updates and strategic defenses will be vital for national security.