The Cybersecurity and Infrastructure Security Agency (CISA) has recently included a significant vulnerability affecting Cisco’s Catalyst SD-WAN Controller in its Known Exploited Vulnerabilities (KEV) catalog. This critical move requires Federal Civilian Executive Branch (FCEB) agencies to address the flaw by May 17, 2026. The vulnerability, identified as CVE-2026-20182, presents an authentication bypass that allows remote attackers to gain administrative control over affected systems without verification, scoring a perfect 10.0 on the CVSS scale for its severity.
Details of the Cisco Vulnerability
This newly disclosed vulnerability in Cisco’s SD-WAN systems poses a significant threat due to its potential to grant unauthenticated remote access to attackers. Cisco has linked the active exploitation of this flaw to a known threat actor, UAT-8616, which previously leveraged another vulnerability, CVE-2026-20127, for unauthorized system access. By exploiting CVE-2026-20182, UAT-8616 can perform actions such as adding SSH keys and modifying configurations to escalate privileges to the root level.
Furthermore, Cisco’s observations indicate that the infrastructure used by UAT-8616 overlaps with Operational Relay Box (ORB) networks. This overlap is part of a broader pattern where multiple threat clusters have been exploiting similar vulnerabilities, such as CVE-2026-20133, CVE-2026-20128, and CVE-2026-20122, since March 2026.
Exploits and Threat Clusters
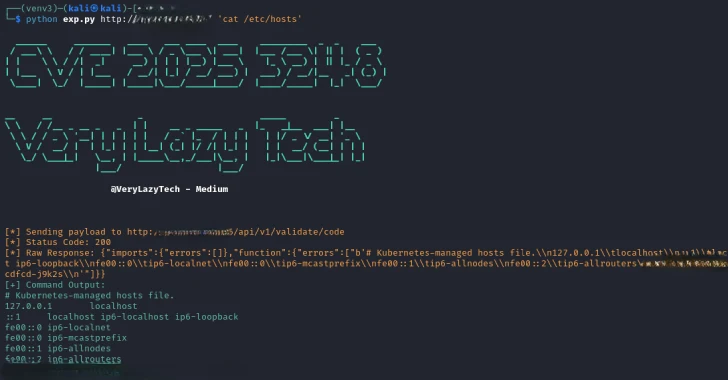
Exploiting publicly available proof-of-concept codes, attackers can deploy web shells on compromised systems to execute arbitrary commands. One notable web shell, dubbed XenShell, utilizes a PoC from ZeroZenX Labs. Analysis has linked at least ten distinct threat clusters to the exploitation of these vulnerabilities. These clusters deploy various tools and frameworks, including Godzilla, Behinder, and Sliver, indicating a coordinated effort to exploit these security weaknesses.
For instance, Cluster 1 has been active since March 6, 2026, deploying the Godzilla web shell, while Cluster 3 uses both XenShell and a Behinder variant. Other clusters focus on deploying malware agents, command-and-control frameworks, and cryptocurrency miners such as XMRig. The diversity in tactics underscores the versatility and resourcefulness of these malicious actors in targeting vulnerable systems.
Recommendations and Future Outlook
Cisco strongly advises its customers to adhere to the guidance provided in their security advisories to mitigate these vulnerabilities effectively. By following the recommended security measures, organizations can better protect their infrastructures from these high-severity exploits. As cyber threats continue to evolve, staying informed and proactive in applying security patches remains critical.
Looking ahead, the cybersecurity landscape is likely to witness an increase in sophisticated attacks exploiting similar vulnerabilities. Organizations must prioritize updating their security protocols and systems, given the potential for significant impacts from such cyber threats.