Cybersecurity experts have revealed a sophisticated cyberattack leveraging the CloudZ remote access tool (RAT) and an undocumented plugin named Pheno to facilitate credential theft. Researchers from Cisco Talos, Alex Karkins and Chetan Raghuprasad, have shed light on this intrusion aimed at stealing credentials and potentially intercepting one-time passwords (OTPs).
Novel Attack Vector Exploits Phone Link
This innovative attack exploits CloudZ’s custom Pheno plugin to hijack the communication bridge between PCs and phones by misusing Microsoft’s Phone Link application. The plugin can monitor active Phone Link processes, potentially intercepting sensitive data such as SMS and OTPs without needing to infect the phone itself. This strategy highlights the risks associated with cross-device syncing features, which can inadvertently open pathways for credential theft and bypass two-factor authentication.
Importantly, the attack does not require compromising the mobile device directly, showcasing how legitimate features can be manipulated for malicious purposes. This malware campaign has reportedly been active since January 2026, although it has not been attributed to any specific threat group.
Technical Details of the Attack Chain
Phone Link, integrated into Windows 10 and 11, enables users to connect their computers with Android or iOS devices via Wi-Fi and Bluetooth, facilitating calls and messages. Threat actors have been observed attempting to exploit this application using CloudZ RAT and Pheno by confirming Phone Link activity on victim systems and accessing the SQLite database used for storing synchronized data.
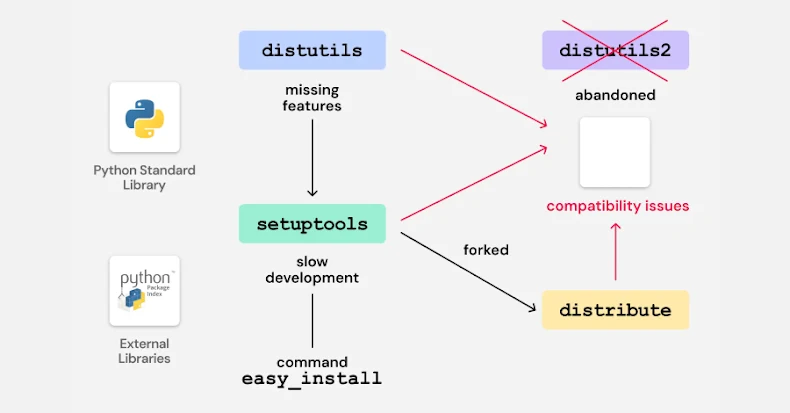
The attack begins with an unidentified initial access method, allowing the deployment of a fake ConnectWise ScreenConnect executable. This executable downloads and executes a .NET loader, incorporating a PowerShell script to establish persistence through a scheduled task. The intermediate loader conducts hardware and environment checks to avoid detection before deploying the modular CloudZ trojan.
Functionality and Impact of CloudZ RAT
Once active, the .NET-compiled trojan decrypts its configuration and connects to a command-and-control (C2) server, awaiting instructions to exfiltrate credentials and deploy additional plugins. Supported commands include system metadata collection, shell command execution, web browser data exfiltration, and Phone Link recon log extraction.
The Pheno plugin conducts reconnaissance on the Phone Link application, writing the data to a staging folder. CloudZ then retrieves this data and transmits it to the C2 server. This highlights the advanced capabilities of CloudZ and its plugins, posing significant threats to affected systems.
The use of CloudZ RAT and its Pheno plugin underscores the evolving nature of cyber threats, where legitimate software functionalities are exploited to bypass security measures. This attack serves as a reminder of the importance of robust security protocols and continuous monitoring to mitigate such risks in modern computing environments.