Ravie LakshmananJan 23, 2026Network Safety / Vulnerability
Fortinet has formally confirmed that it is working to fully plug a FortiCloud SSO authentication bypass vulnerability following stories of recent exploitation exercise on fully-patched firewalls.
“Within the final 24 hours, we have now recognized quite a lot of circumstances the place the exploit was to a tool that had been totally upgraded to the newest launch on the time of the assault, which instructed a brand new assault path,” Fortinet Chief Data Safety Officer (CISO) Carl Windsor stated in a Thursday submit.
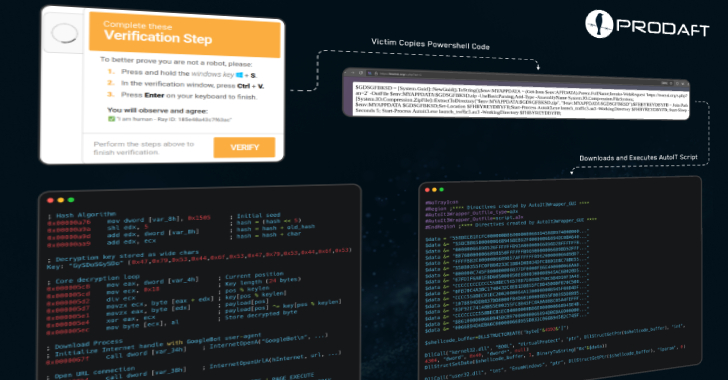
The exercise basically mounts to a bypass for patches put in place by the community safety vendor to deal with CVE-2025-59718 and CVE-2025-59719, which may permit unauthenticated bypass of SSO login authentication through crafted SAML messages if the FortiCloud SSO function is enabled on affected units. The problems had been initially addressed by Fortinet final month.
Nonetheless, earlier this week, stories emerged of renewed exercise during which malicious SSO logins on FortiGate home equipment had been recorded towards the admin account on units that had been patched towards the dual vulnerabilities. The exercise is much like incidents noticed in December, shortly after the disclosure of the CVE-2025-59718 and CVE-2025-59719.
The exercise entails the creation of generic accounts for persistence, making configuration adjustments granting VPN entry to these accounts, and the exfiltration of firewall configurations to totally different IP addresses. The risk actor has been noticed logging in with accounts named “[email protected]” and “[email protected].”
As mitigations, the corporate is urging the next actions –
Prohibit administrative entry of edge community machine through the web by making use of a local-in coverage
Disable FortiCloud SSO logins by disabling “admin-forticloud-sso-login”
“You will need to observe that whereas, right now, solely exploitation of FortiCloud SSO has been noticed, this subject is relevant to all SAML SSO implementations,” Fortinet stated.