The GlassWorm malware campaign has recently intensified with a new attack that utilizes stolen GitHub tokens to inject malicious code into a vast array of Python repositories. This operation, affecting numerous Python projects such as Django apps and PyPI packages, is executed by embedding obfuscated code into crucial files like setup.py and app.py. StepSecurity highlights that this malicious code is activated whenever a user executes a pip install command from a compromised repository.
Details of the Attack
Beginning as early as March 8, 2026, this campaign sees attackers gaining unauthorized access to developer accounts. Once inside, they rebase legitimate commits on the default branch with malware-infused code, force-pushing these changes while maintaining the original commit’s metadata. This sophisticated method ensures the malicious modifications are seamlessly integrated without raising immediate suspicions.
The latest iteration of this malware activity, dubbed ForceMemo, unfolds through a series of calculated steps. Initially, GlassWorm malware compromises developer systems via malicious Visual Studio Code extensions. The malware is engineered to extract sensitive information, including GitHub tokens, which are then used to push harmful changes across all repositories managed by the targeted accounts.
Mechanism and Payload
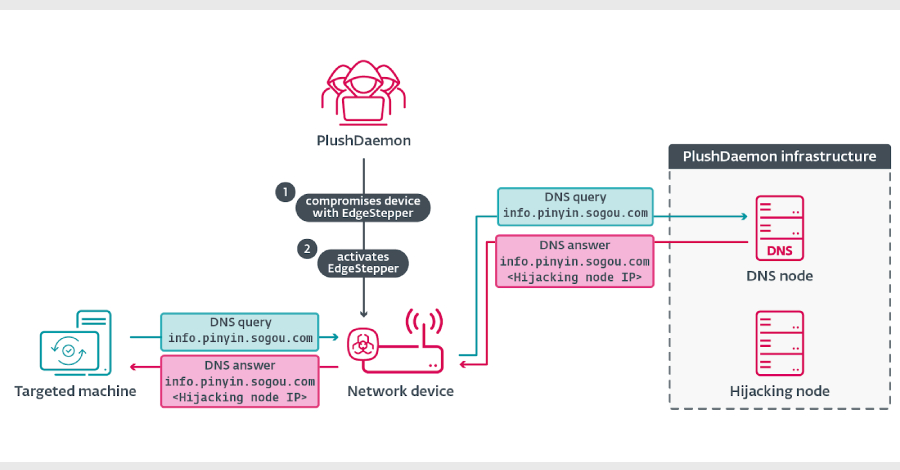
The attackers append a Base64-encoded payload to Python files, incorporating checks to bypass execution if the system locale is set to Russian. If not, the malware consults the transaction memo field of a Solana wallet, previously linked to GlassWorm, to retrieve the payload URL. This process allows the download of additional payloads, including encrypted JavaScript, designed for cryptocurrency and data theft.
StepSecurity notes that the earliest transaction linked to the command-and-control address occurred on November 27, 2025, predating the first GitHub repository compromises by several months. The address has been active, frequently updating the payload URL, sometimes multiple times within a day.
Broader Implications and Response
This disclosure coincides with reports from Socket, indicating that GlassWorm continues to evolve its strategies, employing extensionPack and extensionDependencies for a transitive distribution model. Meanwhile, Aikido Security associates the malware’s author with a broader campaign compromising over 151 GitHub repositories using concealed obfuscation techniques.
The persistent use of a Solana wallet and diverse delivery methods suggest that ForceMemo is a newly developed vector by the GlassWorm operators. By expanding their attack surface from VS Code extensions to GitHub account takeovers, the threat actors demonstrate a sophisticated understanding of software supply chain vulnerabilities.
StepSecurity emphasizes that this attack method is unique in its approach of rewriting git history while preserving commit messages and authorship, leaving no visible trace within GitHub’s interface. This underscores a significant challenge in detecting and mitigating such supply chain attacks, urging developers and security teams to enhance their protective measures.