Google has officially launched the Device Bound Session Credentials (DBSC) for all Windows users on its Chrome 146 browser, advancing its efforts to enhance security against session theft. This new feature, previously tested in beta, is set to expand to macOS users in future updates.
Enhancing Browser Security
The introduction of DBSC marks a significant milestone in Google’s strategy to combat the prevalent threat of session theft. This cyber threat often involves the unauthorized collection of session cookies from web browsers, which can be exploited to access user accounts.
Typically, attackers use malware, such as Atomic, Lumma, and Vidar Stealer, to infiltrate systems and extract these cookies. The extended lifespan of session cookies makes them valuable targets, enabling cybercriminals to gain unauthorized access to accounts and potentially sell these credentials for profit.
How DBSC Works
Originally announced in April 2024, DBSC aims to mitigate such threats by cryptographically linking authentication sessions to specific devices. This approach renders stolen cookies ineffective, as they cannot be used on unauthorized devices.
Google explains that this is achieved through hardware-backed security modules like the Trusted Platform Module (TPM) on Windows and the Secure Enclave on macOS. These modules generate unique key pairs that remain secure within the device.
New session cookies are issued only when Chrome proves possession of the private key, ensuring that any stolen cookies expire quickly and become useless to attackers.
Future Developments and Privacy Considerations
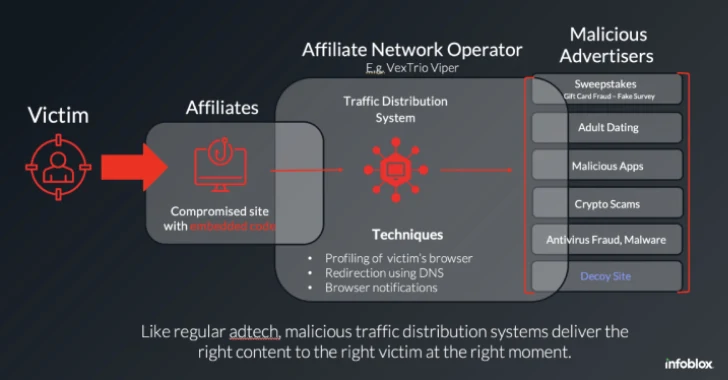
Since the implementation of DBSC, Google has observed a notable decrease in cases of session theft, indicating the effectiveness of this security measure. The company plans to extend DBSC to a broader range of devices and enhance its integration with enterprise environments.
Google collaborated with Microsoft to develop this standard, aiming to establish it as an open web standard. The DBSC architecture is designed to prioritize user privacy, with distinct key approaches preventing websites from tracking user activities across sessions or sites.
As part of its commitment to privacy, the protocol minimizes data exchange, ensuring that it secures sessions without enabling cross-site tracking or serving as a device fingerprinting mechanism.