Google has released crucial security updates for its Chrome web browser to address two critical zero-day vulnerabilities, marking a significant move to enhance user safety. These vulnerabilities, identified as CVE-2026-3909 and CVE-2026-3910, have been actively exploited in the wild, prompting swift action from Google.
Details of the Vulnerabilities
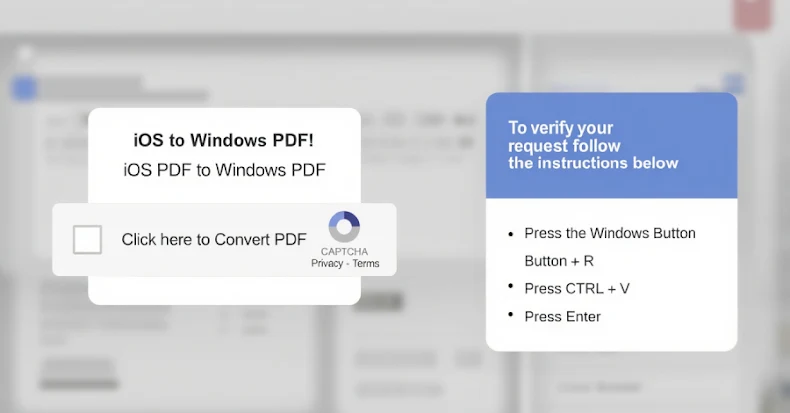
The first vulnerability, CVE-2026-3909, with a CVSS score of 8.8, is an out-of-bounds write issue in the Skia 2D graphics library. This flaw allows remote attackers to access memory beyond the intended bounds via a specially crafted HTML page. The second, CVE-2026-3910, also scored at 8.8, concerns an inappropriate implementation within the V8 JavaScript and WebAssembly engine, enabling attackers to execute arbitrary code within a sandbox when exploiting a manipulated HTML page.
Discovery and Response
Both vulnerabilities were discovered and reported internally by Google on March 10, 2026. In line with standard procedure, Google has withheld specific details of the exploits to prevent further malicious activity by threat actors. The company has acknowledged the existence of these exploits in the wild, emphasizing the urgency for users to update their browsers.
This development follows Google’s recent efforts to address other high-severity issues, such as a use-after-free bug in Chrome’s CSS component, which was similarly patched in the last month. Since the beginning of the year, Google has addressed three actively exploited zero-day vulnerabilities in Chrome, highlighting an ongoing commitment to cybersecurity.
Recommended Actions for Users
To ensure maximum security, Google advises users to update their Chrome browsers to versions 146.0.7680.75/76 for Windows and Apple macOS, and 146.0.7680.75 for Linux. Users can check for updates by navigating to More > Help > About Google Chrome and selecting Relaunch. This action is crucial to safeguard against potential exploits.
Additionally, users of other browsers built on Chromium, such as Microsoft Edge, Brave, Opera, and Vivaldi, are also urged to apply these updates as they become available. Staying current with security patches is essential in mitigating risks posed by these vulnerabilities.
As cyber threats continue to evolve, proactive measures like timely updates remain vital in protecting users from emerging security risks. Google’s rapid response to these threats underscores the importance of maintaining vigilance in the digital landscape.