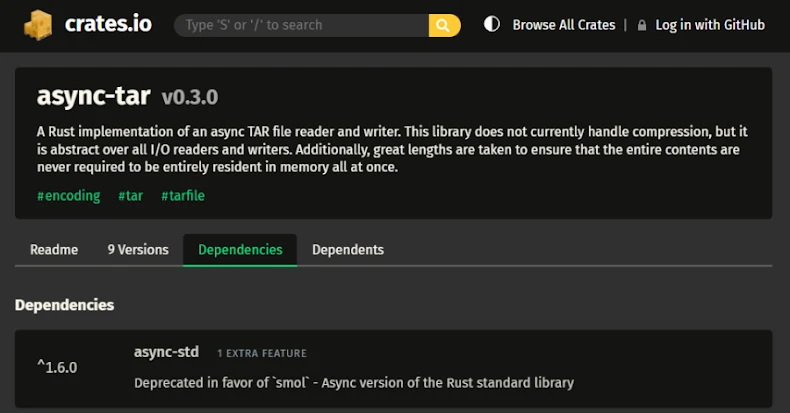
LeakNet, a ransomware group, has introduced the ClickFix tactic for initial access, leveraging compromised websites. This method represents a shift from traditional approaches like using stolen credentials, according to a report by ReliaQuest. ClickFix deceives users into executing malicious commands to resolve non-existent issues, diverging from conventional strategies.
Unique Approach to Initial Access
ClickFix offers significant advantages to LeakNet, including reduced reliance on third-party providers and lower acquisition costs per victim. Compromised websites display fake CAPTCHA verifications, tricking users into executing a ‘msiexec.exe’ command in Windows. This broad approach targets multiple industries, aiming for maximum impact.
LeakNet’s strategic shift from Initial Access Brokers (IABs) to ClickFix highlights a deliberate expansion of their operational capabilities. By using legitimate but compromised websites, the group avoids detectable network signals, enhancing stealth and reach.
Advanced Techniques and Tools
In addition to ClickFix, LeakNet employs a Deno-based loader to execute JavaScript in memory, minimizing on-disk traces and evading detection. The payload fingerprints systems, contacts external servers for further malware stages, and loops to fetch new code. This methodology aligns with their consistent post-compromise strategy.
ReliaQuest also noted a Microsoft Teams-based phishing attempt linked to LeakNet. Although attribution remains unclear, this indicates either LeakNet’s expanding tactics or other actors adopting similar methods. The use of DLL side-loading and PsExec for lateral movement further exemplifies their sophisticated approach.
Impact and Industry Response
LeakNet’s activities emphasize the need for robust cybersecurity measures. Their use of S3 buckets for data exfiltration, mimicking normal cloud traffic, complicates detection efforts. Google’s recent report highlights the persistence of ransomware actors, despite internal conflicts, with several groups consistently targeting victims.
As threat actors adapt to maintain profitability, their focus is shifting towards smaller organizations. This development urges companies to enhance their security defenses and remain vigilant against evolving threats. The resilience of the ransomware ecosystem, despite challenges, underscores the importance of proactive cybersecurity strategies.
The ongoing evolution of ransomware tactics, including ClickFix, reflects the dynamic nature of cyber threats. Organizations must stay informed and prepared to counteract these sophisticated attack vectors effectively.