In a significant cybersecurity revelation, experts have identified 36 malicious packages within the npm registry. These packages masquerade as plugins for the Strapi CMS but are intended to exploit Redis and PostgreSQL databases. By deploying reverse shells, stealing credentials, and establishing persistent access, these packages pose a serious threat to unsuspecting developers.
Disguised Malicious Packages Unveiled
Each package contains three files—package.json, index.js, and postinstall.js—and mimics a mature Strapi plugin by using version 3.6.8. However, they lack any associated description or repository. The naming convention of these packages, which begins with “strapi-plugin-” followed by terms like “cron” or “database,” is designed to deceive developers into downloading them. These packages were uploaded by four sock puppet accounts within a 13-hour window, making them appear legitimate.
Exploitation Tactics and Payloads
The malicious code is embedded in the postinstall script hook, executing automatically during installation. This execution does not require user interaction and operates with the same privileges as the installer, potentially exploiting root access in CI/CD environments and Docker containers. The payloads evolve from exploiting Redis for remote code execution to deploying reverse shells and scanning for sensitive data.
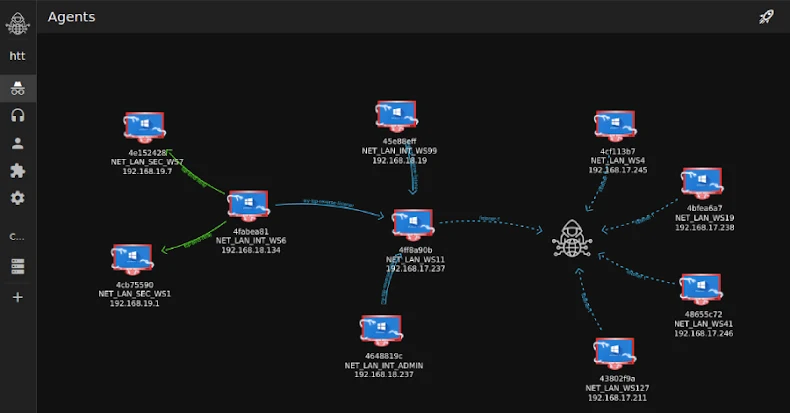
Attackers utilized Redis to escape Docker containers, implemented reverse shells, and harvested PostgreSQL database credentials. They also conducted extensive reconnaissance, mapping network topologies, and extracting sensitive information like cryptocurrency wallet files. These actions suggest a targeted attack on cryptocurrency platforms.
Broader Supply Chain Threats
This discovery is part of a broader trend of supply chain attacks aimed at the open-source ecosystem. Other incidents include credential exfiltration via GitHub pull requests, hijacking of the “dev-protocol” organization for malicious bot distribution, and the compromise of npm and PyPI packages to deploy malware. These attacks highlight the vulnerability of software supply chains, with attackers leveraging trusted platforms to distribute malicious code.
The impact of these attacks is far-reaching, transforming single localized intrusions into global threats. As attackers continue to industrialize supply chain compromises, the threat landscape is rapidly evolving. Organizations need to be vigilant, ensuring constant monitoring and updating of their software dependencies.
Group-IB has noted that software supply chain attacks are reshaping the global cyber threat landscape. These attacks target trusted vendors and open-source platforms to gain widespread access, turning development pipelines into channels for distributing malicious code.
Conclusion and Recommendations
The emergence of these malicious npm packages emphasizes the need for heightened vigilance in software development. Developers and organizations should conduct thorough security audits and rotate credentials if they have used any of the affected packages. The ongoing trend of supply chain attacks calls for a proactive approach to cybersecurity, ensuring the integrity and security of software supply chains.