Cybersecurity experts have recently uncovered a malicious package on the NuGet Gallery that was designed to infiltrate the financial sector. This package, masquerading under the name StripeApi.Net, was created to mimic the genuine library Stripe.net from the financial services company Stripe, which has been downloaded over 75 million times. Uploaded by the user StripePayments on February 16, 2026, this package has since been removed from the platform.
Impersonation Tactics and Credibility
The fraudulent package was meticulously crafted to resemble the official Stripe.net library, according to Petar Kirhmajer from ReversingLabs. The threat actor used the same icon and a nearly identical readme file, with only minor changes such as replacing ‘Stripe.net’ with ‘Stripe-net.’ This attention to detail was intended to deceive developers into believing they were using the legitimate package.
To further establish credibility, the malicious actor artificially boosted the download count to over 180,000. Interestingly, these downloads were dispersed across 506 versions, with each version averaging around 300 downloads, likely to avoid raising suspicion.
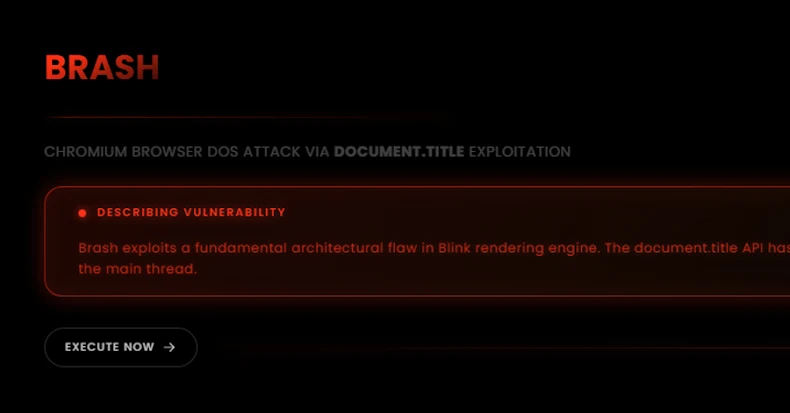
Functionality and Data Theft
Although the package mimicked some functionalities of the authentic Stripe library, it also altered key methods to capture and relay sensitive information, particularly the Stripe API tokens, back to the attacker. The rest of the code appeared fully functional, which meant unsuspecting developers might not notice any discrepancies in their applications.
ReversingLabs was quick to identify and report the malicious package shortly after its release, leading to its removal before it could cause extensive harm. This incident underscores a strategic shift in malicious campaigns, which have previously used fake NuGet packages to target the cryptocurrency market and steal wallet keys.
Implications for Developers
Developers who inadvertently downloaded and incorporated the typosquatted StripeAPI.net library would find their applications working as expected, with no immediate signs of malfunction. Payments would be processed normally, and from the developer’s perspective, everything would seem intact. However, unbeknownst to them, sensitive data was being covertly stolen and transmitted to malicious entities.
This incident highlights the critical need for developers to exercise caution and thoroughly verify the authenticity of libraries before integration. It also points to the growing importance of securing the software supply chain to protect against such cyber threats in the future.