Google has officially connected a supply chain attack on the widely used Axios npm package to a North Korean cyber group identified as UNC1069. This attribution was confirmed by John Hultquist, a chief analyst at Google Threat Intelligence Group, who emphasized the group’s history of employing supply chain attacks, particularly to target cryptocurrency. The ramifications of this compromise are expected to be extensive due to the package’s popularity.
Details of the Axios npm Attack
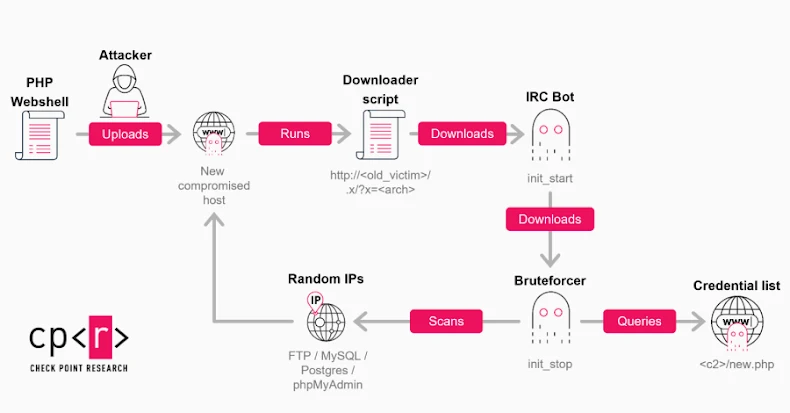
The breach involved threat actors gaining access to the package maintainer’s npm account, leading to the introduction of two tampered package versions, 1.14.1 and 0.30.4. These versions included a harmful dependency known as “plain-crypto-js,” which facilitates the installation of a cross-platform backdoor, capable of affecting systems running Windows, macOS, and Linux.
The attack didn’t modify Axios’s code directly but exploited a post-installation hook in the “package.json” file of the malicious dependency to execute the backdoor stealthily. Upon installation, the code runs automatically, compromising the system effectively.
Technical Insights into the Malicious Code
The “plain-crypto-js” package acts as a delivery mechanism for a concealed JavaScript dropper called SILKBELL. This dropper retrieves additional stages from a remote server, which vary depending on the victim’s operating system: PowerShell malware for Windows, a C++ Mach-O binary for macOS, and a Python backdoor for Linux. The dropper also cleans up traces of its activity to evade detection.
The backdoor, identified as WAVESHAPER.V2, is an evolution of a previous version used by UNC1069 against cryptocurrency targets. Elastic Security Labs first highlighted the link between this attack and UNC1069 due to overlapping functionalities.
Preventive Measures and Future Outlook
To counter this threat, users should carefully review their dependency trees to identify and remove compromised versions, pin Axios to a secure version, search for “plain-crypto-js” in “node_modules,” and terminate any malicious processes. Additionally, blocking the C2 domain and isolating affected systems are recommended actions.
Experts warn that the Axios incident should be seen as a model for future attacks rather than an isolated case. The sophistication of the operation suggests it was designed for scalability, potentially appearing in other package managers like PyPI and NuGet. Organizations are advised to scrutinize all package managers in their build pipelines and treat any exposed secrets as compromised.
This event underscores the need for heightened vigilance in software supply chain security, urging developers and organizations to implement robust protective measures against similar threats.